WannaCry ransomware explained: The attack that changed cybersecurity
In May 2017, ransomware known as WannaCry spread rapidly across computer networks worldwide. Within hours, hospitals, manufacturers, telecommunications providers, and government agencies were dealing with locked computers and disrupted services. The outbreak affected hundreds of thousands of machines across more than 150 countries.
The attack demonstrated how a single software vulnerability could disrupt critical systems worldwide.
In this guide, we explain what WannaCry is, how the attack worked, and how it spread so widely. We also look at the damage it caused and what organizations learned from the incident.
What is WannaCry ransomware?
WannaCry is a self-propagating ransomware. Ransomware is malware that locks files or systems and demands payment to restore access. Most ransomware at the time spread through phishing emails or malicious downloads and needed victims to click or open something before it could infect a machine.
WannaCry was different because it had built-in worm capabilities. A computer worm is malware that spreads automatically from computer to computer. This meant WannaCry could move on its own between vulnerable Windows computers on a network. Once on a machine, it encrypted files and displayed a ransom demand in Bitcoin.
Where WannaCry came from
WannaCry’s ability to spread so rapidly came from an exploit called EternalBlue. EternalBlue targeted a vulnerability in Microsoft’s implementation of the Server Message Block (SMB) protocol, which Windows computers use to share files and communicate across a network. The vulnerability was cataloged as CVE-2017-0144.
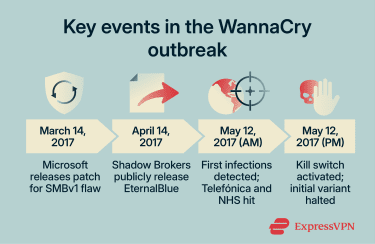
Microsoft released a security update for the flaw in March 2017 as part of bulletin MS17-010, two months before the WannaCry outbreak. But many organizations had not yet applied the patch, leaving large numbers of systems exposed.
EternalBlue became widely known after a group called the Shadow Brokers published a cache of offensive tools in April 2017. The group claimed the tools had been stolen from the Equation Group, a threat actor that had already been extensively analyzed by Kaspersky researchers. Kaspersky referred to it as the “Equation Group” because of its heavy use of encryption algorithms, obfuscation strategies, and other unusually sophisticated techniques across its malware.
The authors of WannaCry incorporated EternalBlue into their ransomware, turning it into a worm that could move automatically from one vulnerable computer to another. That is what made the outbreak so disruptive: once a single unpatched machine was infected, the malware could scan for other exposed systems on the same network and spread without requiring users to click anything.
How does WannaCry ransomware work?
WannaCry operated in three stages: it identified vulnerable machines on a network, installed itself using a backdoor, and encrypted files so the victim couldn't access them. Each stage happened automatically.
How WannaCry spread across networks
Every computer on a network uses numbered ports to handle different types of traffic. Some ports are conventionally associated with specific services; for example, port 80 is typically used for web traffic, port 443 for encrypted web traffic, and port 445 for SMB. However, services can also run on nonstandard ports depending on configuration.
The SMB protocol has gone through several versions over the years. Version 1 (SMBv1) had already been considered insecure and deprecated by the time WannaCry appeared, but many organizations still had it enabled. It contained the flaw that WannaCry exploited. Any machine with port 445 open and SMBv1 still running was a potential target.
Once active on an infected machine, WannaCry scanned for other computers with Transmission Control Protocol (TCP) port 445 open. It checked both the local network and random addresses across the wider internet. When it found a vulnerable machine, it used EternalBlue to gain access and a second tool, DoublePulsar, to load the ransomware.
DoublePulsar is a backdoor, meaning it creates a hidden entry point that lets software be installed on a machine without authorization. It was also part of the Shadow Brokers leak. Some systems already had it installed from earlier use of the same tools to scan and exploit exposed machines. By April 2017, tens of thousands of computers were estimated to have this backdoor installed.
Because the process was entirely automated, a single infected computer on a corporate network could spread WannaCry to every unpatched machine it could reach.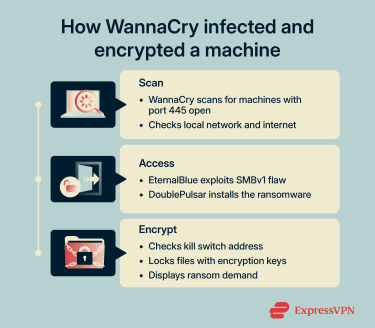
What vulnerability did WannaCry exploit?
The flaw WannaCry exploited (CVE-2017-0144) was a type of programming error known as a buffer overflow. This happens when software writes more data to a block of memory than it was designed to hold. In the case of SMBv1, the error allowed a specially crafted network request to run unauthorized code on the target machine. This is known as arbitrary code execution, meaning an attacker can run any code they choose on the system.
The flaw affected a wide range of Windows versions, including Vista, 7, 8.1, 10, and several Server editions.
Two categories of machines remained exposed after Microsoft issued the patch. The first, as mentioned, were machines whose administrators hadn't installed it. The second was machines running unsupported versions of Microsoft, like Windows XP and Windows Server 2003, which initially received no fixes at all. After WannaCry began spreading, Microsoft took the unusual step of releasing an emergency patch for those unsupported systems.
How WannaCry encrypts files
Before encrypting files, WannaCry checked whether it could reach a specific web address embedded in its code. At the time of the attack, this address wasn’t registered to any real server.
On a normal computer, a request to that address fails because it doesn’t resolve to a real server, so the malware continues running. However, malware is often analyzed in sandboxes, isolated testing environments used by security researchers. These systems sometimes simulate a real internet connection and may return a response even for addresses that don’t exist.
If WannaCry received a reply from that address, it assumed it was being analyzed and shut itself down. Because the address initially had no server behind it, the check failed, and the malware continued running.
Once encryption began, WannaCry locked the victim’s files, preventing them from being opened. It targeted common file types, such as documents, images, and media. Each file was encrypted with its own key, and those keys were then locked using a master key controlled by the attackers. This meant victims couldn't recover their files without the attackers' cooperation.
After the process finished, the malware displayed a ransom note demanding payment in Bitcoin to restore access.
Key dates and timeline of the WannaCry attack
On May 12, 2017, WannaCry was deployed at scale for the first time. Over the following days, the attack triggered a global response from researchers, Microsoft, and government agencies.
- May 12, 2017 (morning): The first WannaCry infections were detected. Some sources place the earliest activity in Asia, while others point to Europe. Mobile network provider Telefónica in Spain was among the first major organizations to publicly report being hit.
- May 12, 2017 (afternoon): British cybersecurity researcher Marcus Hutchins activated WannaCry's kill switch, effectively halting the initial variant's spread.
- May 13, 2017: Microsoft released emergency patches for unsupported operating systems, including Windows XP and Windows Server 2003.
- May 14–15, 2017: New WannaCry variants appeared with different kill-switch domains. Researchers Matt Suiche and Check Point analysts registered those domains, stopping the second and third variants.
- December 2017: The U.S. and U.K. governments formally attributed the attack to the Lazarus Group.
How WannaCry spread worldwide so fast
Because WannaCry continuously and automatically scanned for vulnerable machines, it crossed organizational and national boundaries within hours.
By the end of May 12, organizations across Asia, Europe, and the Americas had been affected. Renault-Nissan, Deutsche Bahn, Russia's Ministry of Internal Affairs, and the U.K. National Health Service (NHS) all reported disruption.
What was the impact of the WannaCry attack?
Symantec, whose enterprise security division is now part of Broadcom, estimated the global financial impact of WannaCry at roughly $4 billion, though estimates vary widely by methodology. The cost came from a combination of lost business activity, disrupted operations, and IT recovery expenses.
Among the best-documented cases was the NHS in England. The U.K. National Audit Office (NAO) found that more than 80 trusts and 600 other NHS organizations, including GP practices, were disrupted. Staff couldn't access patient records. Medical equipment, including MRI scanners, went offline. Five hospitals had to divert ambulances to other facilities. The NAO estimated that over 19,000 appointments were cancelled. A study published in npj Digital Medicine calculated the direct cost to infected trusts at £5.9 million (roughly $8 million) in lost hospital activity.
Healthcare was particularly exposed because many NHS trusts were running unpatched Windows 7. Without the patch, these systems remained vulnerable. The NAO investigation found that every infected organization could have protected itself through relatively straightforward measures, including applying the patch and properly configuring its firewalls.
Other organizations were affected too, although often in different ways. Telefónica said its internal network was hit, but that none of its customer network services were affected and normality was restored within 48 hours. Deutsche Bahn later reported that WannaCry affected ticket machines and display boards in stations, while train traffic and the security of customer and customer data were not at risk.
How the WannaCry attack was slowed
The initial WannaCry variant wasn't stopped by a coordinated government response. It was stopped by a 22-year-old security researcher working from his bedroom in England.
The role of Marcus Hutchins
Marcus Hutchins, who blogged under the name MalwareTech, began analyzing WannaCry samples on the morning of May 12. While examining the code, he noticed the malware was trying to contact an unregistered address: iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com. He registered it. Once the address went live, new WannaCry variants that still contained the kill switch logic began shutting down.
The reason this worked ties back to the encryption process described above. Before locking any files, WannaCry checked whether that hardcoded address was live. On a real computer, an unregistered address returns nothing, so encryption proceeded. But once Hutchins registered it, every new WannaCry copy received a response, which it interpreted as a signal to shut down.
Machines that were already encrypted before the registration stayed locked, but new infections dropped sharply.
The kill-switch address quickly became a target in its own right. In the days that followed, attackers tried to knock it offline by flooding it with junk traffic from botnets. This type of attack is known as a distributed denial-of-service (DDoS) attack.
If the address went offline, WannaCry copies would stop receiving responses and start encrypting again. Hutchins prevented this by placing it behind a DDoS protection service, which spread the traffic across multiple servers so no single point could be overwhelmed.
Is WannaCry still a threat today?
WannaCry is still a threat today, but in a much narrower sense than it was in 2017. Microsoft says WannaCry is fully addressed by the MS17-010 security updates, and its guidance for that vulnerability also recommends disabling SMBv1, the old file-sharing protocol the worm abused. In other words, properly updated systems are not the main concern anymore; the bigger risk is older or poorly maintained Windows machines that never got patched or still rely on SMBv1.
What keeps the issue relevant is that the underlying bug family has not become purely historical. CVE-2017-0144, one of the Microsoft SMBv1 remote-code-execution flaws linked to WannaCry, is still listed in the Cybersecurity and Infrastructure Security Agency’s (CISA’s) Known Exploited Vulnerabilities Catalog, which means defenders are still expected to treat it as an actively important weakness. So while another worldwide WannaCry-style wave is much less likely on fully updated networks, organizations with legacy systems, unsupported devices, or weak patching practices can still face real risk from the same weakness or malware that abuses it.
How ransomware has evolved since WannaCry
Modern ransomware operations these days look very different from WannaCry. Groups like Cl0p, a ransomware group known for targeting large corporations, often gain access through phishing or software vulnerabilities. They spend weeks or months inside a network before deploying ransomware.
They identify the most valuable data and disable backups first. Many now employ double extortion. This means they don't just encrypt files; they also steal data and threaten to publish it unless the victim pays.
Ransomware-as-a-Service (RaaS) platforms have further lowered the barrier to entry. These are operations where developers build the malware and rent it to affiliates who carry out the actual attacks, typically in exchange for a share of the ransom payments.
How to protect against WannaCry and similar ransomware
The defenses that would've stopped WannaCry also apply to most modern ransomware and advanced persistent threats.
Patch management and system updates
Organizations that had applied the available patch weren't affected by WannaCry. A patch management process that tests and deploys critical security updates within a defined timeframe significantly reduces exposure to known flaws.
For systems that can't be patched immediately, disabling SMBv1 removes the specific attack surface WannaCry used. Microsoft has recommended disabling SMBv1 since 2016, and Windows 10 version 1709 and later have it turned off by default.
Network segmentation and access controls
Many of the networks WannaCry hit had no internal boundaries. Every machine could communicate freely with every other machine. Once the worm infected one computer, nothing stopped it from spreading to the others.
Dividing a network into separate zones, each with its own access rules, limits how far any malware can travel. For example, a hospital's billing department and its diagnostic equipment don't need to share the same network segment. If one zone is compromised, the others remain isolated.
At the network perimeter, which is the boundary between an organization's internal network and the public internet, blocking unsolicited inbound traffic on SMB ports (particularly port 445) prevents threats like WannaCry from entering directly. Within the network, restricting that traffic to only the systems that actually need it further narrows exposure.
The same principle applies to user accounts and permissions. Rather than giving every employee or system broad access across the network, organizations can limit each account to only what's needed for its specific role. This is known as least-privilege access. If one account is compromised, the attacker can only reach what that account was authorized to touch.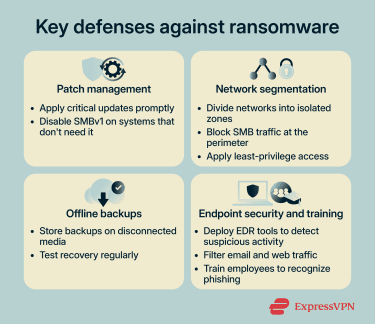
Offline backups and recovery planning
Some organizations that were hit had backups, but those backups sat on the same network as everything else. WannaCry encrypted them, too. Offline backups, sometimes called air-gapped backups, are stored on media that's physically disconnected from the network. Some organizations also use immutable backups, which prevent stored data from being modified or deleted for a set period.
Because they aren't reachable from the network, ransomware can't touch them. Testing those backups regularly matters just as much as having them. If a backup hasn't been tested, there's no guarantee it'll work when it's needed.
Endpoint security and employee training
Endpoint detection and response (EDR) tools monitor individual devices for suspicious behavior. For example, a program suddenly encrypting large numbers of files can trigger an alert. EDR can flag it and contain the threat before it spreads to other machines.
Email filtering and web gateways screen incoming messages and web traffic for known threats. These tools add a layer of protection against phishing, which is how most modern ransomware that doesn't self-propagate reaches its victims.
Employee training is important, too. Employees who can recognize a phishing email and know how to report it reduce the chance of an initial compromise turning into a wider incident.
FAQ: Common questions about WannaCry ransomware
How did the WannaCry attack spread so quickly?
Why was the WannaCry attack so damaging?
Is WannaCry still a threat today?
The EternalBlue exploit that WannaCry used is also leveraged by other malware families, so the threat extends beyond WannaCry itself. Applying Microsoft's MS17-010 patch or disabling SMBv1 eliminates the vulnerability.
Did paying the WannaCry ransom restore encrypted files?
What did the cybersecurity industry learn from WannaCry?
Those that hadn't or were running unsupported operating systems suffered the worst consequences. The attack accelerated investment in patch management, network segmentation, and offline backups across both public and private sectors.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN