DoS vs. DDoS attacks: Key differences and how to protect yourself

Ever heard the terms "DoS" and "DDoS" thrown around when people talk about cyberattacks? They sound similar (and they are), but there’s an important difference that can mean the difference between a mild annoyance and a major outage.
In this article, we’ll break down what sets a denial-of-service (DoS) attack apart from a distributed denial-of-service (DDoS) attack, explain how each works, and share practical tips to help you stay protected. No jargon, no panic, just clear, straightforward advice to help you understand these threats and defend against them.
What is a DoS attack?
A denial-of-service (DoS) attack is a cyberattack that aims to make a system, server, or network unavailable by overloading it with more traffic or requests than it can handle. This can leave it slow, unresponsive, or completely offline for legitimate users.
Typically, DoS attacks come from a single device controlled by the attacker. Using simple scripts or tools, they flood the target with repeated requests. Because they rely on one source rather than a large botnet, they’re usually easier to detect and block but can still cause serious disruption, especially for systems with limited capacity or poor defenses.
What is a DDoS attack?
A distributed denial-of-service (DDoS) attack is like an upgraded, more powerful version of a DoS attack. Instead of coming from one device, it uses many devices working together to overwhelm the target. These devices (often infected with malware) form what's known as a botnet.
During a DDoS attack, all of these systems send traffic at the same time, flooding the target from multiple directions. This makes the attack much harder to block and can take down even large websites or networks. Because of their scale and coordination, DDoS attacks are more difficult to stop and can cause much more damage than a simple DoS attack.
DoS vs. DDoS: What’s the difference?
It’s easy to mix up DoS and DDoS attacks since both aim to overwhelm a target with traffic until it stops responding. But there are important differences in how they’re carried out and the scale of damage they can cause.
Source of the attack
The main difference is where the traffic comes from:
- In a DoS attack, all traffic originates from a single machine. The attacker uses their own device directly to flood the target.
- A DDoS attack uses many systems at once. These devices are typically infected with malware and controlled as part of a botnet, sending traffic from multiple locations simultaneously.
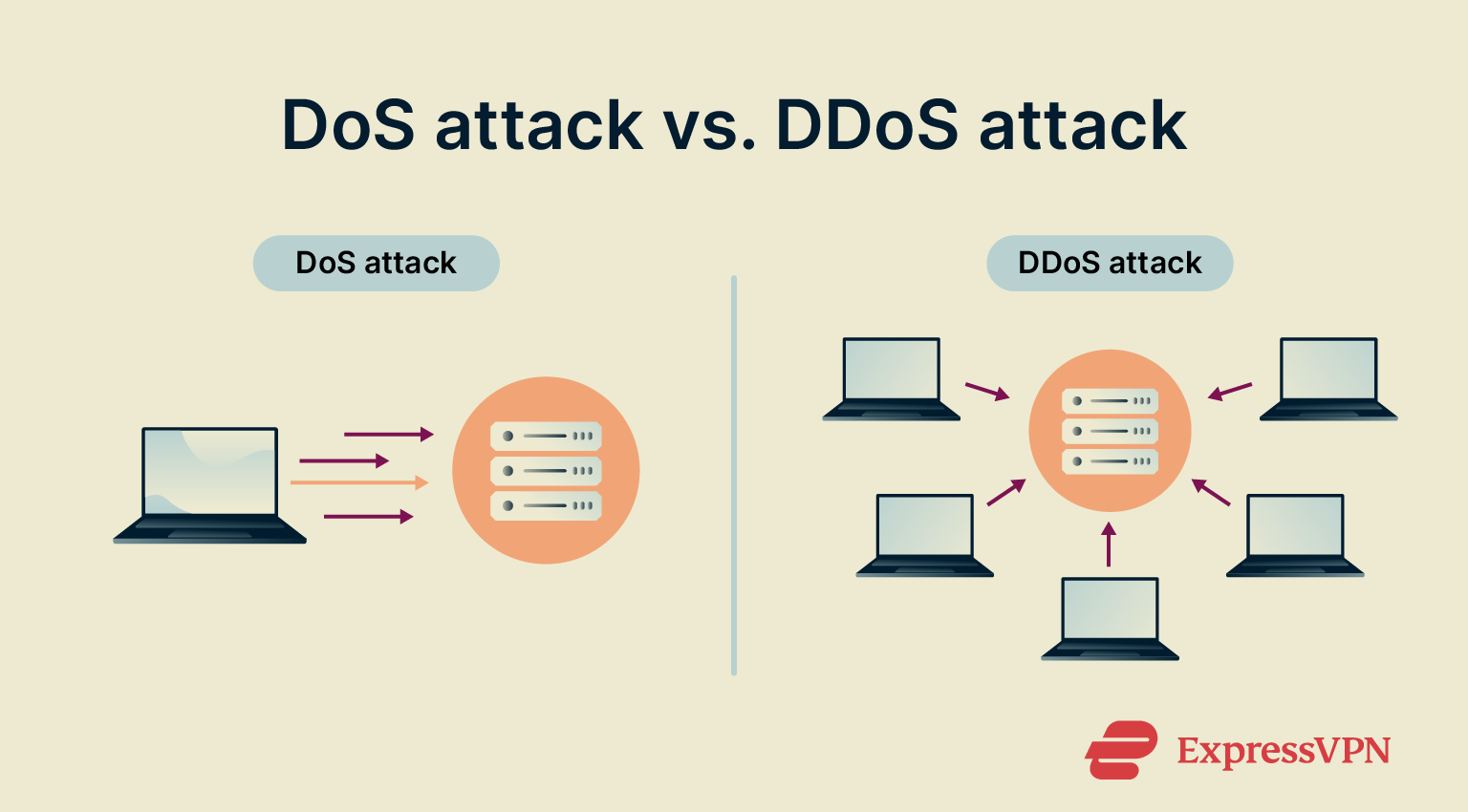
Scale and impact
A DoS attack is limited by the power of one device. It can still put serious pressure on a website or service, but there’s a limit to how much traffic it can generate.
A DDoS attack doesn’t have that limitation. With hundreds or thousands of bots working together, the traffic can ramp up quickly and overwhelm even large, well-protected networks.
Detection and mitigation difficulty
Since a DoS attack comes from one location, it’s usually easier to detect and block. Filtering the traffic or blocking the offending IP address is often enough.
A DDoS attack is much harder to defend against. The traffic comes from many sources at once, making it difficult to tell legitimate users from attackers. You can’t just block one IP address, and even blocking many addresses can risk cutting off real users. Defending against it typically requires advanced filtering, rate limiting, and scanning the whole network for bot activity.
Cost and consequences
DoS attacks are relatively easy and cheap to launch; just one device and the right tools are enough. They’re simpler to organize and typically easier to contain.
DDoS attacks are more sophisticated and can be far more damaging. They often last longer, cost more to mitigate, and can take entire systems offline, leading to serious downtime and financial losses. Attackers sometimes use them to extort businesses by threatening prolonged outages.
Radware’s report estimates the cost of downtime during a successful application-layer DDoS attack at over $6,000 per minute, adding up to hundreds of thousands of dollars per hour.
Side-by-side comparison of DoS vs. DDoS attacks
| DoS attack | DDoS attack | |
| Source | Single device | Multiple devices (botnet) |
| Traffic origin | One location | Many locations |
| Execution | Uses direct scripts or tools from attacker’s device | Coordinated attack with malware-infected systems |
| Traffic volume | Lower, limited to one machine’s capacity | Much higher, amplified by many systems |
| Detection | Easier to detect and trace | Harder to trace due to multiple sources |
| Blocking | Can often be stopped by filtering the source | Requires advanced filtering, rate limiting, or bot detection |
| Setup complexity | Simple to organize | More complex infrastructure with command-and-control servers |
| Impact | Can take down specific apps or services | Can disrupt entire networks or platforms |
| Cost to launch | Low | Higher, though tools like botnet kits make it more accessible |
| Consequence severity | Usually local or limited | Can be widespread and harder to recover from |
Common types of DoS and DDoS attacks
While it’s tempting to group DoS and DDoS attacks into neat categories, the reality is more complicated. Many attacks blur the lines between layers, and there isn’t always a single clear-cut way to label them.
That said, we can still understand them by what they try to overwhelm, whether it’s raw bandwidth, how connections are handled, or the applications themselves.
High-volume attacks (volumetric)
These attacks aim to flood a target with massive amounts of data, exhausting bandwidth so that legitimate traffic can’t get through.
- User Datagram Protocol (UDP) floods: Bombard servers with requests that trigger time-wasting responses, even when no real service is there.
- Ping floods: Overwhelm systems with Internet Control Message Protocol (ICMP) echo requests (“pings”) until they can't respond to anything else.
- Amplification attacks: Use spoofed requests to get services like Domain Name System (DNS) or Network Time Protocol (NTP) to reply with large amounts of data to the victim. These services aren’t vulnerable per se; the issue lies with how UDP doesn’t verify source IPs. Attackers take advantage of that to “bounce” traffic toward their target.
Connection-handling attacks
These target how systems manage multiple connections and sessions. They often aim to exhaust server resources without using a lot of bandwidth.
- SYN flood: Exploits the Transmission Control Protocol (TCP) handshake by sending many “connection start” requests and never finishing them, tying up the server.
- Slowloris: Sends tiny bits of data over many connections very slowly, keeping them open and using up server slots.
- Teardrop: Sends overlapping or malformed data fragments that crash systems trying to reassemble them, especially older or unpatched machines.
Application-level attacks
These go after the actual programs and services that users interact with, like websites or online apps. Instead of flooding bandwidth, they try to overload processing power or crash specific features.
- Billion laughs attack: A type of XML bomb that tricks applications into expanding a tiny file into a massive data structure, crashing the system. The first entity is often the string “lol,” which gets repeated billions of times, hence the name “billion laughs.”
- Slowloris (again): Also fits here because it targets how the app manages requests, not just the transport layer.
- Regular expression denial of service (ReDoS): Triggers crashes by exploiting overly complex regular expressions in input validation.
- Email bombing: Floods inboxes with thousands of automated messages, often using sign-up forms or newsletter systems. It’s a type of DoS that can hide important messages like login alerts or password resets, and it’s sometimes used as cover for fraud.
Learn more: If any of these terms feel a bit too technical, you can check out our easy-to-read internet security glossary for clear, simple explanations.
Why do DoS and DDoS attacks happen?
DoS attacks aren’t just random chaos. Attackers often have clear goals in mind, from making money to pushing political messages or disrupting rivals.
- Ransom and financial extortion: Attackers overwhelm a company’s systems, then demand payment to stop. For businesses that rely on being online, this can create urgent pressure to pay quickly.
- Competitive sabotage: Businesses can also be targeted by rivals looking to cause damage during a big launch or sale. Even brief downtime can hurt revenue and customer trust.
- Hacktivism and political motives: Some groups use DoS attacks as digital protests, targeting governments or companies they oppose. It’s a way to draw attention to a cause by disrupting services.
- Revenge, pranks, and mischief: With easy-to-use attack tools, some individuals launch DoS attacks for personal grudges, curiosity, or just to cause trouble, even if they don’t fully grasp the damage it can cause.
Real-world DDoS attack examples
DDoS attacks aren’t just theoretical; they’ve caused real, costly disruptions for some of the biggest names online. Here are a few well-known examples that show how damaging these attacks can be in practice:
HTTP/2 rapid reset attack on tech giants
In 2023, companies like AWS, Google, and Cloudflare were hit by a new type of DDoS method called the HTTP/2 Rapid Reset attack. It exploited a weakness in the HTTP/2 protocol to send a flood of rapid requests and cancellations, overwhelming servers without needing huge botnets.
At its peak, this attack reached around 398 million requests per second. Even with strong defenses, these major platforms were caught off guard by how effective this new technique was.
Google’s massive UDP amplification attack
Google experienced one of the largest DDoS attacks ever recorded, peaking at 2.5 Tbps. This UDP amplification attack used thousands of misconfigured servers to reflect and amplify traffic toward Google’s systems. The attack lasted for months and was much bigger than anything they’d seen before.
Learn more: If you want to dive deeper into some of the biggest attacks in history, check out this roundup of famous DDoS attacks.
How to prevent DoS and DDoS attacks
DoS and DDoS attacks can target anyone, from individual gamers to large organizations. While you can’t always stop them completely, there are practical steps you can take to reduce your risk and improve your defenses.
For individuals
A reliable VPN like ExpressVPN helps protect you by hiding your real IP address, making it harder for attackers to find and target you, which is especially useful for gaming or hosting servers.
But a VPN isn’t a complete defense. It can’t stop an attack if your IP is already known or block attack traffic that’s already coming in. For serious or repeated attacks, you may need to change your IP through your internet service provider (ISP) or use services and gaming platforms that have built-in DDoS protection to help absorb and mitigate attacks automatically.
For organizations
Businesses and institutions are often bigger targets, so they need a layered and proactive approach. Some of the key practices include:
- Robust network architecture: Designing networks with redundancy and multiple failover paths helps reduce the impact if one component gets overwhelmed.
- Anti-DDoS software and appliances: Hardware and software solutions can filter out malicious traffic before it reaches your core infrastructure.
- Cloud-based DDoS protection services: Third-party providers can absorb and neutralize attacks on your behalf, which is especially helpful during large-scale events.
- Load balancing and bandwidth scaling: Distributing incoming traffic across multiple servers and scaling resources can prevent overload and service disruption.
- Incident response plan: Having a clear plan for what to do during an attack, including who to notify and how to respond, saves precious time when every second counts.
- Routine security checks: Regularly reviewing your infrastructure allows you to catch and fix weak points before they become a real threat.
FAQ: Common questions about DoS vs. DDoS attacks
What is the difference between DoS and DDoS attacks?
A denial-of-service (DoS) attack uses one computer to flood a target with traffic and slow it down. A distributed denial-of-service (DDoS) attack does the same but with many devices at once, making it faster, harder to stop, and more damaging. Since DDoS traffic comes from multiple sources, it's also much harder to trace.
Are DoS and DDoS attacks illegal?
Yes, launching a denial-of-service (DoS) or distributed denial-of-service (DDoS) attack is illegal in the United States. Under the Computer Fraud and Abuse Act (CFAA), intentionally harming a computer or server through these attacks can result in criminal charges, including up to 10 years in prison.
What happens during a DoS attack?
During a denial-of-service (DoS) attack, one computer floods a website or server with too many requests. This overloads the system and makes it hard, or impossible, for real users to connect. Sometimes, the server crashes or stops working until the attack ends.
What is the difference between DoS protection and DDoS protection?
Denial-of-service (DoS) protection blocks traffic from a single source, often using basic filters. Distributed denial-of-service (DDoS) protection is more complex since the attack comes from many sources at once. It needs advanced tools to spot and stop fake traffic without affecting real users.
Can I accidentally DDoS someone?
No, distributed denial-of-service (DDoS) attacks are deliberate and require tools, infected devices, or services that coordinate traffic floods. They don’t happen by mistake.
How do I know if I’m under a DDoS attack?
Your site might be under a distributed denial-of-service (DDoS) attack if it suddenly loads very slowly, shows 503 errors, or logs show many repeated connections from the same IP. Unusual traffic patterns are a strong warning sign, especially if other sites work fine while yours doesn’t.
Is a VPN enough to stop a DDoS attack?
A VPN can help hide your IP and block basic distributed denial-of-service (DDoS) attacks, but it won't protect you if the attacker already knows your real IP address.
Can a CDN help protect against DDoS attacks?
Yes, a content delivery network (CDN) can help absorb and distribute incoming traffic across multiple servers, making it harder for a distributed denial-of-service (DDoS) attack to overwhelm a single point.
With cloud CDN providers like Amazon, Google, Akamai, or Cloudflare, it’s even better: they absorb the brunt of the attack for you. Because they’re hosting and serving your content, their global infrastructure and defenses handle the attack traffic, helping keep your site online even under pressure.
Many CDNs also include built-in DDoS mitigation features that detect unusual patterns and filter out malicious traffic.
Can I trace where a DDoS attack came from?
Tracing a distributed denial-of-service (DDoS) attack to its true origin is extremely difficult. Attackers often use botnets made up of compromised devices around the world, which hide the real source. Even if you identify the IP addresses involved, they’re usually just infected machines, not the person behind the attack.
What is the largest DoS or DDoS attack?
One of the largest known distributed denial-of-service (DDoS) attacks by request rate was the HTTP/2 Rapid Reset attack in 2023, which targeted companies like AWS, Google, and Cloudflare, peaking at around 398 million requests per second.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN


















Comments
I wish I could take this all in I do believe I have email attackers an wish they'd leave me alone I am poor an not so smart . Please someone help me understand.
Just to know to help people from bad hurckers