-
How to stop remarketing ads from following you everywhere
You bought a laptop from an online store last month, and now you’re seeing ads from that retailer promoting accessories or new laptop models. This is likely the result of an advertising technique ca...
-

Customer data protection: Practical steps to keep customer information safe
Every time a customer shares their name, email address, payment details, or physical address with a business, that business takes on the responsibility of protecting that information. It’s required ...
-
What is machine learning? Understanding its significance and applications
Machine learning (ML) powers many of the apps, online services, and devices people use every day. It enables ride-sharing services, drives personalized recommendations on streaming platforms, and help...
-
What is personal information? Definition, examples, and protection
Every time someone signs up for an online account, enters a shipping address, or logs into an app, they share pieces of personal information. In this guide, we break down what counts as personal infor...
-
What is a cloud server? Everything you need to know
A cloud server is a virtual server hosted in a cloud computing environment that delivers computing resources like processing power, storage, and applications over the internet. In this guide, we’ll ...
-
Filter bubble explained: How algorithms shape what you see online
Online platforms, including search engines, social media apps, and video-sharing sites, try to show you content that you’re more likely to engage with. This can make the internet feel more relevant,...
-
How to recover deleted files on iPhone: 7 fast ways that work
Losing a file on your iPhone can feel final, but in many cases, it isn’t. Deleted photos, notes, documents, and other files often remain recoverable for a while. This guide walks you through practic...
-
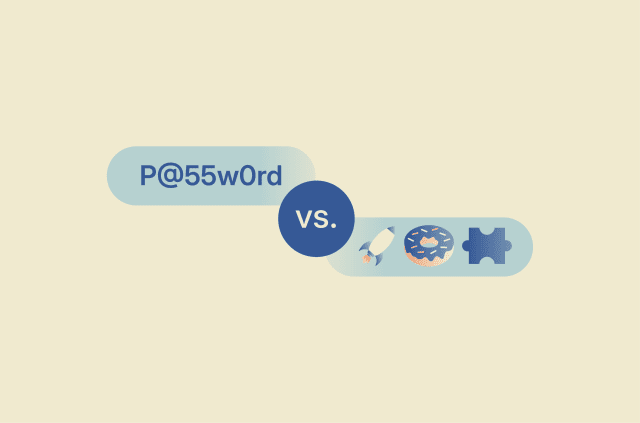
Passphrase vs. password: Which one gives you better security?
It’s easy to assume that any password is enough to protect your accounts, but not all secrets offer the same level of security. While traditional passwords have long been the standard for signing in...
-
How to delete your Google Play account safely and protect your data
Your Google account and Play Store profile are important hubs for managing many of the services and apps you use on a daily basis. However, for various reasons, you may wish to decouple a Google accou...
-
Triangulation fraud: How it works and how to prevent it
You order something online, it arrives exactly as promised, and everything seems fine. However, unbeknownst to you, a fraudster has used stolen credit card details to purchase the item, making you an ...
Featured


