Port-out scam explained: How phone numbers get stolen and how to stay safe
Phone numbers play a big role in digital life. Many services use them to verify identity, reset passwords, and send security codes across banking, email, social media, and crypto accounts. A port-out scam takes advantage of that: instead of hacking user accounts directly, attackers hijack the phone number first and then use it to gain access to other services.
This guide explains how port-out scams work, the risks they pose, steps to take after an incident, and key measures to help prevent them.
What is a port-out scam?
A port-out scam, also called a number or phone porting scam, happens when a fraudster uses the legitimate process of transferring a phone number between carriers to move it to another account without authorization. The transfer is typically made to a carrier where the attacker controls an account, often without the victim’s knowledge or consent. Once the transfer is complete, they begin to receive the victim’s calls and text messages.
How is a port-out scam different from SIM swap fraud?
Port-out scams and SIM swap fraud refer to different attacks with a similar outcome. SIM swap fraud happens when a fraudster moves the victim’s phone number to a SIM card or eSIM profile that they control while keeping the number with the same carrier. In a port-out scam, the attacker transfers the victim’s phone number to another carrier and, often, to another account entirely.
Why are port-out scams dangerous?
The danger of a port-out scam lies in how central a phone number is to a user’s digital identity. Many online services, including banks, email providers, investment platforms, and social media networks, rely on SMS-based two-factor authentication (2FA) as a security layer. When a fraudster gains control of a user’s phone number, they effectively gain access to that security layer.
A successful port-out scam may allow an attacker to:
- Intercept private calls and messages intended for the victim.
- Receive security and authentication codes.
- Reset credentials for important accounts, locking the victim out.
- Drain money from bank accounts or apply for credit in the victim’s name.
- Impersonate the victim and commit identity theft.
How port-out scams work
Most port-out scams follow a similar pattern, and they typically involve the following: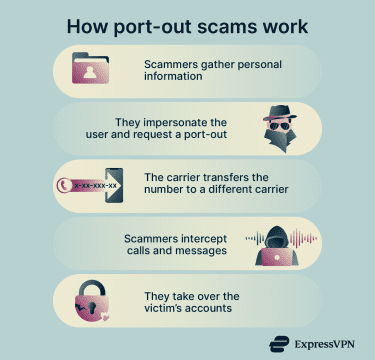
- Information gathering: Attackers collect information about the victim, such as addresses, passwords or PINs, Social Security number (SSN) or other identity document details, and birth dates. They may gather this data from social media, phishing attacks, stolen or leaked databases on the dark web, or data brokers.
- Impersonation: Fraudsters then target the victim’s carrier using social engineering. They essentially use the collected information to impersonate the victim and request a number port-out.
- Porting: If the impersonation attempt succeeds, the carrier initiates the port-out process, transferring the victim’s phone number and service to a new account with a different carrier under the attacker’s control.
- Interception: At this point, the attacker is able to receive calls and text messages intended for the victim.
- Account takeover: Using intercepted messages and SMS-based verification codes, attackers can bypass security checks and gain unauthorized access to email, banking, or social media accounts.
Warning signs of a port-out scam
When a phone number is ported, some carriers send notifications to the account holder. In the absence of an alert, common warning signs of a successful port-out scam include:
- Sudden service disruption: The phone suddenly loses signal and displays “No Service” or “SOS Only,” even in areas with normally strong coverage.
- Loss of text and call capabilities: The device becomes unable to make or receive calls or send messages, except for emergency calls.
- Suspicious notifications: Alerts about password resets, unfamiliar logins, or unrecognized transactions appear.
- App disruptions: Messaging apps like WhatsApp or Telegram may stop working or require re-verification after a port-out.
- Account lockout: Victims may get signed out of important accounts and be unable to log back in.
- Strange calls and messages: Friends, family, or other phone contacts may report suspicious activity from the victim’s number or be unable to reach them.
What to do if you’ve been targeted
Port-out scams can lead to financial and reputational damage, so time is of the essence when dealing with suspected attacks. If you suspect a port-out scam, follow these steps:
Contact your mobile carrier right away
Contact your mobile carrier as soon as possible and report the fraud. Acting quickly might allow the provider to reverse the port-out or help you regain control of your phone number and account. Most carriers offer dedicated phone numbers for reporting port-out scams, which you can find on their websites. Some providers also offer support through live chat.
Secure your banking, email, and crypto accounts
Attackers often target critical accounts, including email, banking, investment, and social media services. Act fast and update your passwords to reduce the chance of unauthorized access.
Use strong passwords that are unique and at least 12 characters long. If you haven’t already, enable multi-factor authentication (MFA) to add an extra layer of protection during login.
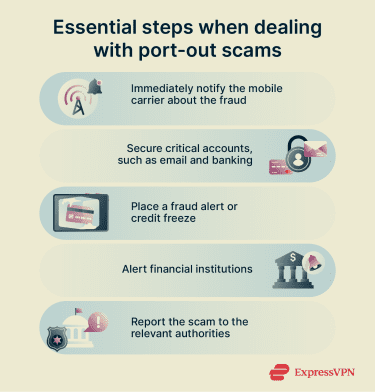
Notify relevant financial institutions
Call your bank or credit union and let them know that your phone number has been compromised and that it may be used to access your account. Ask them about how to protect your accounts and credit cards, and any other fraud-prevention methods they recommend. In the U.S., consider also notifying Experian, Equifax, or TransUnion and requesting a fraud alert or asking them to place a credit freeze.
If your bank uses text messages for authentication, you can also ask whether they offer alternatives, such as authenticator apps or push notifications.
Report the fraud and document the incident
In addition to contacting your carrier and financial institutions, it’s a good idea to report the fraud to relevant authorities, such as consumer protection agencies.
If you’re in the U.S., you can file a report with the Federal Trade Commission (FTC) at IdentityTheft.gov. This will generate a personal recovery plan and an official Identity Theft Report, which you can use to dispute fraudulent accounts. You can also consider filing a complaint with the FCC regarding the carrier that processed the fraudulent port request.
If financial losses occurred, you may want to file a police report with your local law enforcement as well. Keep copies of all correspondence with your carrier, financial institutions, and credit bureaus for your records, as this information can help authorities investigate the case.
How to protect yourself from a port-out scam
Certain measures can help reduce exposure to port-out scams. The best protection is a combination of carrier-level security features, strong account hygiene, and reduced dependence on SMS-based authentication.
Secure your mobile account
Many carriers provide fraud prevention tools that you can activate through your account dashboard or mobile app. Depending on the provider, available options may include:
- Set up a port-out PIN or passcode that must be provided when contacting the carrier about the account.
- Turn on account alerts to receive notifications about password reset requests or suspicious login attempts.
- Enable port-out protection, also called a port-out lock or freeze, to prevent the number from being transferred to another carrier.
Improve online account security
A phone number is only as valuable to an attacker as the accounts it can unlock. Reducing dependence on SMS-based authentication limits exposure. Instead, you can opt for authenticator app codes, in-app push notifications, or biometric authentication.
Next, turn on activity alerts for critical accounts to receive notifications about unauthorized access attempts so you can take action more quickly. Additionally, create strong logins and use a unique password for each account. A password generator can help create strong credentials, while a password manager can securely store and manage them.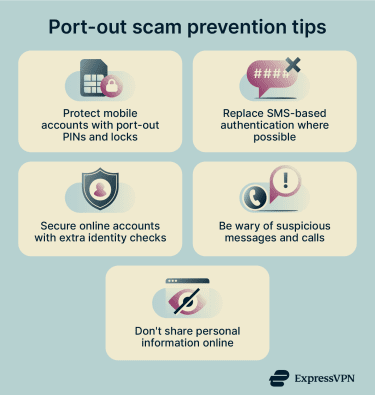
Be wary of suspicious messages and calls
Learning how to detect phishing is essential, as it’s a common way attackers gather information to hijack phone numbers. Avoid engaging with unsolicited calls or messages that:
- Create a sense of urgency and pressure you into quick action.
- Use threatening language to induce fear, such as claims that an account is compromised.
- Encourage interaction with suspicious links or file attachments.
Fraudsters may also impersonate trusted entities, including mobile carriers. Most providers don’t contact customers to request sensitive information such as passwords, PINs, SSNs, or payment details. If an unsolicited message claims to be from a carrier or another authority, contact the organization directly using official channels to verify the request.
Don’t overshare online
Avoid sharing personally identifiable information (PII), such as email or home addresses, full names, or birth dates, on social media, forums, or other public platforms. Scammers may collect such details and use them to craft personalized phishing messages that trick victims into revealing more information or interacting with malicious links and files.
The connection between port-out scams and identity theft
Port-out scams can lead to identity theft, where an attacker steals someone’s personal and financial information and uses it without their consent. These scams typically rely on fraudsters already having access to their victim’s personal data.
However, if successful, such attacks can trigger further exposure as scammers gain unauthorized access to valuable information, like credit card numbers and bank account details. Attackers may then use this data to compromise financial accounts, drain funds, take out loans, create fraudulent accounts, or carry out other forms of fraud while impersonating the victim.
How to reduce your risk of identity theft
In addition to protecting against port-out scams, it helps to recognize the warning signs of identity theft. Early detection allows potential victims to act quickly and limit the damage. Common signs include:
- Sudden, unexplained drops in credit score.
- Unrecognized credit card or bank account activity.
- Unauthorized credit report inquiries.
- Calls about unfamiliar accounts or debts.
- Data breach notifications.
Other preventive measures include regularly checking credit reports, reviewing credit card and bank account statements, and safeguarding physical documents and mail.
Using an identity theft protection service can also help by monitoring credit activity, sending alerts about unusual changes, scanning for exposed personal data on hidden websites or forums, and supporting identity restoration.
Some services also offer additional features, such as data removal from broker sites or financial monitoring. For example, ExpressVPN offers an Identity Defender app with identity monitoring and data removal tools for eligible users in the U.S.
FAQ: Common questions about port-out scams
Can a port-out scam happen without my knowledge?
How long does it take to recover a stolen phone number?
Does a port-out PIN stop all account takeover attempts?
Which accounts should I secure first after a port-out scam?
Should I freeze my credit after a port-out scam?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN