Cyber espionage explained: How cyber spying works and how to strengthen digital defenses


Cyber espionage occurs when an unauthorized actor uses digital networks, systems, or services to gather information, often for political or economic advantage. As more information is created, stored, and transmitted digitally, it has become an increasingly significant cybersecurity concern.
This article examines typical cyber espionage targets, common methods used by attackers, and practical measures organizations can take to strengthen their defenses.
What is cyber espionage?
Cyber espionage (also known as cyber spying or digital espionage) is the digital evolution of traditional espionage. Both share the goal of obtaining operational, technical, or personal information. The difference is that traditional espionage typically relies more on human agents or physical infiltration, whereas cyber espionage exploits computer systems and digital tools. For example, malware or phishing are common tools of cyber spies.
Cyber espionage is usually aimed at organizations or individuals that possess sensitive or high-value information, like governments or corporations.
Is cyber espionage a crime?
Cyber espionage often involves activities that fall under various national and international laws. For example, cyber espionage between nation-states is often considered a legal grey area. There’s an overall lack of consensus on its status in international law; the Tallinn Manual (a NATO-commissioned academic study of law and cyberwarfare) states that ‘[a]lthough peacetime cyber espionage by States does not per se violate international law, the method by which it is carried out might do so.’
Economic cyber espionage is more commonly prohibited under national legislation. In the U.S., two relevant federal laws are the Computer Fraud and Abuse Act (CFAA) and the Economic Espionage Act (EEA). The CFAA makes it illegal to access a computer without permission or to exceed authorized access to obtain protected information. The EEA targets the theft of trade secrets, criminalizing the theft of proprietary information to benefit a foreign entity or harm the owner.
Cyber espionage vs. cyberwarfare
Cyberwarfare is usually defined as cyber operations conducted or directed by one state against another. Cyber espionage can be a precursor to cyberwarfare, often taking place during the reconnaissance stage of cyberwarfare. For example, an attacker might use cyber espionage to identify security vulnerabilities in the target's network.
Cyberwarfare also includes actions that go beyond intelligence gathering, aimed at disrupting or damaging critical systems. For example, an attacker might launch a distributed denial-of-service (DDoS) attack to take down government websites or financial networks.
Cyber espionage vs. cybercrime
Cybercrime refers to any illegal activity carried out using computers or networks. This could include cyber espionage, depending on the circumstances, but is more generally used to describe other types of crimes, such as identity theft or ransomware attacks.
Typical cyber espionage targets
Here are some of the most common targets of cyber espionage, why they’re so frequently targeted, and the potential consequences for victims.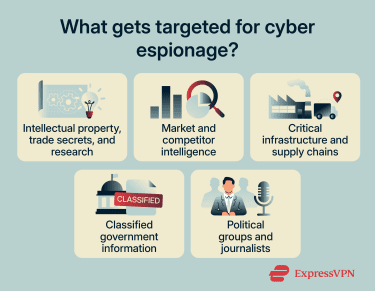
Intellectual property, trade secrets, and research
Organizations engaged in developing new technologies are often targeted for cyber espionage. This is because stolen designs, formulas, or research findings can give competitors an economic edge.
A victim of this type of cyber espionage may see reduced returns on research and development investments. They may also suffer long-term financial damage if competitors are able to replicate or undercut their products.
Market and competitor intelligence
Businesses may be targeted for information such as market strategy and pricing. Access to this kind of data could enable rivals to anticipate moves, craft competing offers, or target high-value customers with more attractive terms.
Besides financial losses, exposure of client data can also lead to legal or regulatory penalties and damage the business’s reputation.
Critical infrastructure and supply chains
Critical infrastructure targets can include power grids and transportation networks, as well as key supply chains that support these sectors. Intelligence on system vulnerabilities and operational procedures can be used to plan future attacks.
The consequences of such attacks could include disruption of vital services, compromised public safety, or damage to national or organizational stability.
Classified government information
Government agencies and institutions hold highly sensitive data, including national security strategies and diplomatic communications. This makes them a prime target for state-sponsored actors who seek intelligence to inform state strategy or policy decisions.
Political groups and journalists
Attackers may target political organizations to gather information on a rival party’s plans or strategies. They might also seek personal information on individual members that could be used against them.
Journalists may be targeted to identify confidential sources, which can reduce insiders’ willingness to share sensitive information. In some cases, this could also put those sources at risk.
Common cyber espionage methods
Below are some of the most common attack vectors used to gain access to sensitive systems and extract information.
Phishing and social engineering
Phishing is a type of social engineering attack that exploits human behavior rather than technical weaknesses. In phishing attacks, the threat actor tricks people into clicking malicious links, opening infected attachments, or revealing login credentials.
Successful attacks can provide unauthorized access to internal systems or install malicious software that allows attackers to gather sensitive information without detection.
Phishing messages may be sent in bulk to large numbers of people, like spam, in hopes that someone will fall for it. Alternatively, they may be carefully crafted to target a specific individual or small group, using personal or professional details to make a message appear more authentic. This is a tactic known as spearphishing.
Credential theft and password attacks
This broad category includes techniques that are used to gain access to sensitive systems by obtaining usernames and passwords. A common technique is guessing weak passwords using a brute force attack. Another technique involves exploiting previously exposed credentials from earlier data breaches as part of a credential stuffing attack (though this requires the target to use the same password across different accounts).
Once valid credentials are obtained, attackers can impersonate a legitimate user. This allows them to bypass security controls and access internal systems to gather information.
Malware and remote access tools
Some types of malware, including spyware and keyloggers, are designed to secretly monitor systems and capture sensitive information.
Attackers use a variety of methods to deliver malware onto target systems. For example, they might:
- Exploit security vulnerabilities in apps and tools used by organizations.
- Take advantage of unsecured devices, such as routers with weak or default passwords.
- Gain access through remote access tools with overly broad permissions. In this case, the attacker could even gain full control over the device.
Insider threats
Insider threats occur when employees or contractors misuse their access to sensitive information. They may sell confidential data to rivals or provide unauthorized entry to systems or networks. This type of cyber espionage can be especially difficult to detect and stop because the threat actor has legitimate access and privileges, allowing them to bypass many security controls.
How to defend against cyber espionage
Defending against cyber espionage requires a combination of proactive monitoring and strong technical safeguards, as well as ongoing staff awareness. Here are key strategies organizations can use to help protect their systems and data.
Detection
Early detection is a critical step in limiting the damage caused by cyber espionage. The following signs can indicate potential espionage:
- Unusual network activity: Unexplained data transfers, logins at odd hours, or access patterns that deviate from normal behavior.
- Unauthorized access attempts: Repeated failed logins, access from unknown IP addresses or devices, or unusual use of privileged accounts.
- Unexpected system changes: Modifications to files, configuration settings, or software that weren’t authorized.
- Suspicious app behavior: Unknown processes, unusual CPU or memory usage, or attempts to connect to external servers.
Monitoring tools, such as intrusion detection systems (IDS), extended discovery and response (XDR), and data loss prevention (DLP) solutions, can help organizations track activity. These are often combined with regular log analysis to review events and identify anomalies, and threat hunting for proactive, human-led investigation of potential breaches.
Security
These are the key solutions organizations generally implement to protect against cyber threats like cyber espionage.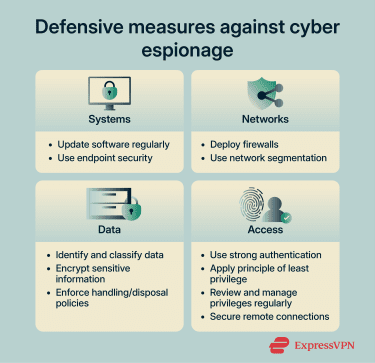
Systems
- Keep software and operating systems up to date: Security updates address known vulnerabilities that attackers could exploit.
- Use endpoint security solutions: Antivirus software attempts to block known malware, application control prevents unauthorized apps from running, and device management programs help enforce security policies.
Networks
- Configure firewalls effectively: Rules and policies can be configured to control incoming and outgoing traffic. For example, an organization may whitelist trusted IP addresses and block unused ports.
- Use network segmentation: Networks can be divided into separate zones, so if an attack occurs, it can be contained within one area.
Data
- Classify and inventory data: Identifying what sensitive data the organization holds, where it resides, and who has access to it, helps prioritize protection efforts.
- Encrypt sensitive data: Encryption helps protect data in storage and transit by making it difficult to read or modify without the correct decryption key.
- Establish secure data handling and disposal practices: Having approved procedures for storing, sharing, and destroying data helps ensure sensitive information is protected throughout its lifecycle.
Access
- Implement strong authentication: Examples include mandating strong, unique passwords and multi-factor authentication (MFA).
- Apply least privilege access controls: Users and systems are granted only the permissions necessary for their roles.
- Review and manage privileges regularly: Frequent audits keep track of access rights and unnecessary permissions (e.g., revoking privileges when an employee leaves).
- Help secure remote access: External connections can be further shielded by security tools, which add a layer of encryption, such as remote access virtual private networks (VPNs).
Staff training
Educating staff is a crucial component of preventing cyber espionage. Cybersecurity training in organizations might cover topics such as safe handling of sensitive data and secure use of devices, including bring-your-own-device (BYOD) policies. Employees may also be taught how to recognize phishing attempts and other common cyber threats.
Regular refresher sessions are also useful to help reinforce these practices and build a culture of cybersecurity awareness.
Cyber espionage cases and examples
Operation Aurora
Operation Aurora was a coordinated cyber espionage campaign uncovered in late 2009 and publicly disclosed in January 2010 by Google. The attacks exploited a vulnerability in Microsoft Internet Explorer and affected many high-profile companies, including Google, Adobe, and Yahoo.
The attackers used malware delivered via spearphishing to access the Gmail accounts of human rights activists and steal intellectual property. While many security analysts attribute the campaign to state-sponsored actors, the identity of the perpetrators remains a subject of debate. Attribution in cyber operations is inherently complex and often lacks public consensus.
The incident had a significant global impact. Microsoft released an emergency security patch to fix the exploited vulnerability. Google also reevaluated its operations in the affected region following the breach.
More broadly, Operation Aurora raised awareness of advanced persistent threats (APTs) and prompted organizations worldwide to strengthen their defenses.
Operation Shady RAT
Operation Shady RAT was a long-running cyber espionage campaign uncovered in 2011 by security firm McAfee. The operation had been active since at least 2006 and affected over 70 organizations in 14 countries, including government agencies and global corporations.
Like Operation Aurora, the attackers gained access to high-security servers using malware delivered through spearphishing emails. Once inside victim systems, they were able to monitor networks and extract sensitive information, including government data, trade secrets, and confidential communications.
The GhostNet mystery
GhostNet was a large-scale cyber espionage operation uncovered in 2009 by researchers at the University of Toronto's Munk Centre for International Studies. The investigation revealed a network of compromised computers in over 100 countries, including systems belonging to foreign ministries and international organizations.
The attackers used a combination of drive-by attacks and spearphishing emails to infect target systems and gain remote control.
GhostNet highlighted the potential for attackers to conduct large-scale digital surveillance of diplomatic and governmental networks. It also exposed cybersecurity vulnerabilities in international communications.
FAQ: Common questions about cyber espionage
What is cyber espionage or cyber spying?
Who carries out cyber espionage?
How is cyber espionage different from cyberwarfare?
The goal of cyber espionage is intelligence gathering: covertly obtaining information for political, economic, or strategic advantage. Acts of cyber espionage can serve as reconnaissance for potential future cyberwarfare.
How is cyber espionage detected?
How do you defend against cyber espionage?
What are the consequences of cyber espionage?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN