-
Golden ticket attack: What it is and how to defend against it
In many Windows environments, Active Directory (AD) is responsible for authenticating users and controlling access to systems. When attackers gain deep access to these identity systems, they can forge...
-

The VPN was just the beginning: Meet the new security suite
One subscription now secures your network, thoughts, credentials, communications, and identity. ExpressVPN has evolved from a single tool into a comprehensive security suite. Think of it as your ultim...
-
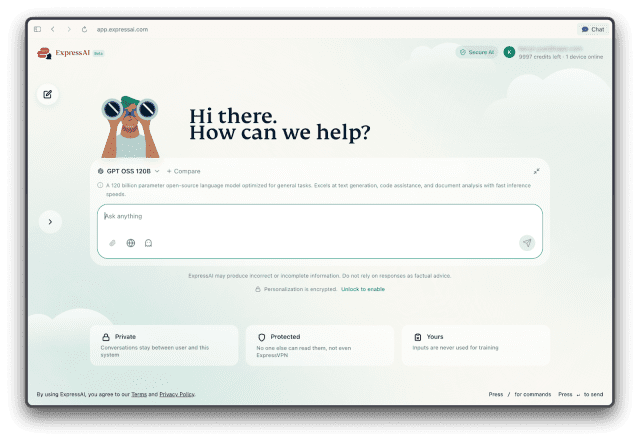
Introducing ExpressAI: A private-by-design AI platform
Most AI platforms keep your data, so we built one that doesn’t Most AI platforms log, retain, or reuse what you submit. ExpressAI was built so you don’t have to accept that trade-off. Every inter...
-

Is mobile banking safe? Your questions answered
Mobile banking is generally safe if you follow good security practices (like keeping your banking app up to date) and avoid higher-risk situations such as using public Wi-Fi. Most risks come from atta...
-

How to get rid of adware on Mac and prevent future infections
If your Mac suddenly floods you with pop-ups, redirects your searches, or keeps changing browser settings you just fixed, something is interfering with your system. These problems can continue even af...
-
What is a hacker? Types, risks, and how to stay safe
“Hacker” is one of the most misunderstood terms on the internet. In movies and headlines, hackers are often portrayed as mysterious criminals breaking into systems from dark rooms filled with glow...
-
Lost Mode on iPhone: How to enable it and secure your device
Lost Mode is an Apple security feature that helps you protect and locate your device if it goes missing. When you turn it on, your phone locks, shows a custom message plus optional contact information...
-
SSH key authentication explained: How it works, why it matters, and how to set it up
Passwords help protect accounts and remote access, but weak or reused credentials can still be guessed, stolen, or abused. Secure Shell (SSH) key authentication offers a more secure way to sign into s...
-

What is DRM? Understanding digital rights management
You try to watch a video, but it won’t play. Or you take a screenshot on a streaming service and get a black screen. This is often because of digital rights management (DRM). DRM sets the rules behi...
-
Cloud-as-a-Service (CaaS) explained: How it works, benefits, and real-world examples
Cloud-as-a-Service (CaaS) is a broad term for cloud computing services that are hosted by a third-party provider and made available to customers over the internet, typically on a subscription or pay-p...
Featured







