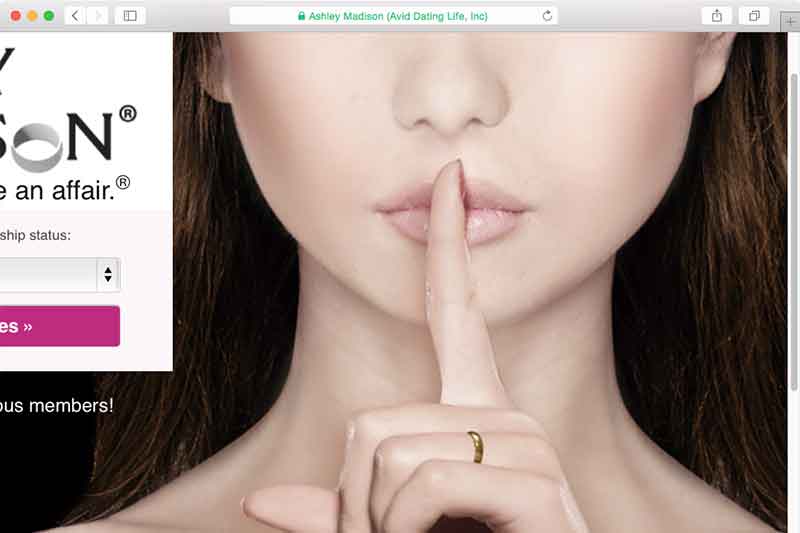
The first thing you see when you visit Ashley Madison, the Internet’s go-to adultery site, is a woman perching a finger to her lips. Unfortunately, shoddy security systems weren’t enough to keep Ashley’s confidential information a secret, with hackers successfully stealing more than 33 million users’ emails, credit card info and transaction details.
Ouch.
How It Happened
The hackers, known as the Impact Team, were able to obtain private data from both the site’s users and owners and said they would publish the information unless Madison’s parent company, Avid Life Media (ALM), would shut down its various sites. The hackers claimed ALM was intentionally deceiving its customers by not only creating fake profiles but also refusing to delete its existing ones.
ALM did not comply.
The hackers responded by releasing more than 10GB worth of data in July, and then 20GB over two separate occasions in August. While the first batch of information contains users’ private information, the latest batches focus more on ALM and its employees.
Bone-Chilling Revelations
The new information isn’t good. Now that journalists have had enough time to comb through the latest data dumps, startling revelations are coming to light, including the fact that the majority of Ashley Madison’s female users were fake.
Even worse, it’s now painfully obvious ALM was not only aware of their security weaknesses, they did absolutely nothing to fix it.
If big-name corporations aren’t taking the proper steps to secure your private information, who will?
Why You Should Be Worried
Even if you aren’t personally connected to the Ashley Madison hack, you could still be involved. That’s because a handful of the accounts registered were done under other people’s names and emails. And on a totally different but still totally terrifying note, data aggregation firms are currently slurping up the leaked data and are actually using it to sell to other companies.
A Lesson in Internet Security
While credit card info, names, photos and email addresses of the users were leaked, their passwords, thankfully, were hashed.
Unfortunately, a number of these passwords are so weak that practically anyone can break them. Just ask security expert Dean Pierce, who reportedly cracked more than 4,000 Ashley Madison passwords in just a matter of days. The two most common passwords? “123456” and “password.”
We’ll let that sit for a minute…
All jokes aside, the Ashley Madison hack is scary--not only because it shows just how vulnerable so-called “high-security” domains are but also because it uncovers a fundamental flaw: people still don’t know how to create strong passwords.
“Nobody Was Watching”
In a recent Motherboard interview, the hackers openly bragged about how easy it was to penetrate the site. According to them, “Nobody was watching. No security.”
In the same interview they also mentioned having collected 300GB worth of employee emails and other sensitive documents, meaning this may only be the beginning of the financial and legal problems for ALM.
Avoid Getting F*cked
So what can we learn from all this? Two things. First, make sure you’re using secure passwords (we recommend using a randomly generated password), and second, any site—no matter how big—may be vulnerable, so it’s important you take the right preventative measures by beefing up your own personal security.
The next time you think about using your dog’s name for your password, think again.
Could the Ashley Madison scandal finally be the wake-up call for companies everywhere to improve their IT security? Leave a comment and let us know what you think.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN