Symmetric encryption explained: How it works, why it matters, and where it’s used
Whenever data is protected in transit or at rest, encryption often works behind the scenes. Among the many cryptographic techniques in use today, symmetric encryption is one of the oldest and most widely used. It remains a core building block of modern security systems and underpins many protocols and applications at scale.
In this article, we'll explain how symmetric encryption works, why it remains so important in modern cybersecurity, and where it's used in the real world. We'll also look at common algorithms and some of the practical challenges involved in managing shared secret keys.
What is symmetric encryption?
Symmetric encryption is a type of encryption in which the same secret key is used to both encrypt and decrypt data. The sender uses the key to encrypt the information, and the recipient uses that same key to decrypt it.
Symmetric-key techniques can also help protect integrity and authenticity. For example, a Message Authentication Code (MAC) can verify that data hasn’t been altered in transit, while authenticated encryption modes combine confidentiality and integrity in a single system.
Modern symmetric cipher design is heavily influenced by two principles described by Claude Shannon in 1949: confusion and diffusion. Confusion obscures the relationship between the key and the encrypted output. Diffusion spreads the effect of each input bit across the entire output, so that even a small change in the original data produces a significant change in the result. Together, these properties help reduce patterns that attackers could otherwise exploit.
Read more: The history of encryption: From ancient codes to digital security.
Why symmetric encryption matters
Symmetric encryption remains essential largely because it is fast. Symmetric algorithms rely on operations that are less computationally expensive than those used in public-key cryptography, allowing them to process large volumes of data quickly and efficiently. This makes symmetric encryption the practical choice when performance matters.
It also plays a central role in hybrid cryptographic systems. In these systems, asymmetric cryptography is used to establish or exchange a shared secret, and symmetric encryption is then used to protect the actual data. This approach combines the convenience of public-key cryptography with the speed needed for bulk data transfer.
Learn more: Read our detailed explainer on symmetric vs. asymmetric encryption.
How does symmetric encryption work?
Symmetric encryption follows a straightforward principle: take readable data, apply mathematical transformations using a secret key, and produce an unreadable output. The same key is then used to recover the original data.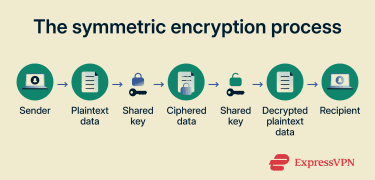
The encryption and decryption process
For block ciphers, the process begins by dividing input data into fixed-size blocks. Advanced Encryption Standard (AES), the most widely used symmetric algorithm today, processes data in 128-bit blocks regardless of key size. Older algorithms, such as the Data Encryption Standard (DES), which is now outdated, use 64-bit blocks.
Each block then passes through multiple rounds of transformation. In AES, these rounds combine substitution, permutation, and key mixing to turn plaintext into ciphertext. Decryption uses the same secret key to reverse that process and recover the plaintext.
How symmetric keys are shared
For two parties to communicate using symmetric encryption, both must possess the same secret key before exchanging protected data. This creates a fundamental challenge: if an attacker intercepts or copies the key during exchange, all data protected with that key can be compromised.
In practice, this problem is solved by pairing symmetric encryption with asymmetric techniques. A key-agreement protocol like Diffie–Hellman allows two parties to establish a shared secret over an untrusted channel without ever transmitting the key itself.
Alternatively, public-key cryptography can be used to encrypt or wrap a symmetric key for the recipient, often within a public key infrastructure (PKI)-based system. Once the shared key is established, symmetric encryption takes over for the actual data protection.
Types of symmetric encryption algorithms
Symmetric encryption isn't a single algorithm; it's a family of algorithms developed over decades, each designed to meet the security and performance demands of its time. Some are now considered legacy standards, while others remain in active use.
Before diving in, it's worth clarifying two terms that often get mixed up. An algorithm is a mathematical procedure for encrypting and decrypting data, such as AES and Blowfish.
A protocol is a broader set of rules that governs how encryption is applied in a real-world system, including how keys are exchanged, how connections are authenticated, and which algorithms are used. Transport Layer Security (TLS) and Internet Protocol Security (IPsec) are protocols: they rely on algorithms like AES under the hood, but handle much more than encryption alone.
Advanced Encryption Standard
AES is the most widely adopted symmetric encryption algorithm in use today. It encrypts and decrypts data in blocks of 128 bits using keys of 128, 192, or 256 bits.
AES was adopted as a federal standard in 2001 after a rigorous public competition to replace the ageing DES. Because it has been extensively analyzed and enjoys dedicated hardware support, AES is widely regarded as the gold standard for data encryption.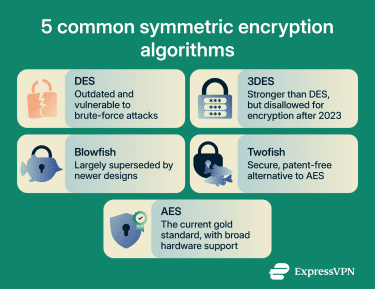
Data Encryption Standard and Triple DES
DES was published in 1977 and reaffirmed four times, most recently in 1999. It operates on 64-bit blocks using a 64-bit key, with 56 bits used by the algorithm and 8 parity bits for error detection.
Because the effective key length is only 56 bits, DES became vulnerable to brute-force attacks as computing power grew. To address this, the Triple Data Encryption Algorithm (TDEA, or 3DES) was introduced. It applies the DES algorithm three times in sequence using two or three independent keys, significantly increasing security over single DES.
However, applying DES three times doesn’t triple the security. In practice, attacks such as the meet-in-the-middle attack (where an attacker works forward from the plaintext and backward from the ciphertext to find a match in the middle) reduce the effective security of some 3DES variants, and the algorithm’s 64-bit block size is also a major limitation for modern use.
The National Institute of Standards and Technology (NIST) deprecated three-key 3DES through December 2023 and disallowed its use for encryption after that date, while still permitting certain legacy uses, such as decryption of already-protected data.
Blowfish and Twofish
Blowfish is a block cipher designed by cryptographer Bruce Schneier in 1993 as a fast, unpatented alternative to DES. It uses a 64-bit block size, a variable key length up to 448 bits, and a structure called a Feistel network, a design where data is split into two halves and repeatedly processed through rounds of substitution and mixing. Blowfish applies 16 such rounds, making it highly resistant to known attacks.
Its key initialization phase generates large key-dependent S-boxes (lookup tables that substitute input values to obscure patterns), and once that setup is complete, encryption is very efficient. The trade-off is that the setup itself is resource-intensive, making Blowfish less suited for applications that require frequent key changes or run in memory-constrained environments.
Its 64-bit block size also makes it less suitable for encrypting large volumes of data under a single key. Bruce Schneier has noted that while there is still no practical attack against Blowfish, its 64-bit block length is a limitation, and he recommends using Twofish instead.
Twofish is a 128-bit block cipher that accepts keys up to 256 bits. Like Blowfish, it uses a 16-round Feistel network with key-dependent S-boxes, but adds a Maximum Distance Separable (MDS) matrix: a mathematical structure that strengthens diffusion by ensuring that a change to any single input byte affects all output bytes.
Twofish was one of five finalists in the NIST competition, but ultimately lost out to AES. It remains a secure, patent-free alternative, though it is adopted less often than AES in practice.
Common uses of symmetric encryption
Symmetric encryption is used wherever large volumes of data need to be protected quickly and efficiently. Here are some of the most common applications:
- Secure communication: Network protocols like TLS (which secures HTTPS connections), virtual private network (VPN) tunnels, and Wi-Fi Protected Access 2 or 3 (WPA2/WPA3), all rely on symmetric encryption to protect data in transit. During connection setup, asymmetric techniques are often used to establish or derive shared session keys. From that point on, symmetric encryption handles the actual data protection.
- File and disk encryption: Symmetric encryption is the standard approach for protecting stored files and entire drives. Full-disk encryption tools like BitLocker and FileVault use AES to encrypt every block on a drive, preventing unauthorized access if a device is lost or stolen.
- Database and cloud security: Many cloud services encrypt stored data at rest by default, often using AES. In databases, features like Transparent Data Encryption (TDE) use symmetric encryption to protect data at rest without requiring application changes. Other approaches, such as column-level encryption, can protect sensitive fields like payment details or personal identifiers, though implementation details vary by platform.
- Backup and archive protection: Backups and archives often contain complete copies of an organization's data, making them high-value targets. Encrypting them helps ensure older copies of data remain confidential even if storage media is compromised.
Also read: End-to-end encryption: What it is and why it matters.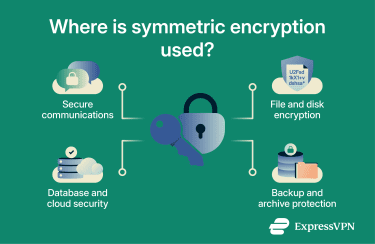
Key management best practices
Encryption is only as secure as its key management. If a key is leaked during distribution, stored insecurely, or used longer than it should be, the protection it provides can be weakened or lost. The practices below address important areas of the key lifecycle: rotation, storage, administration, and access control.
Key rotation
Rotate encryption keys on a regular schedule to limit the amount of data any single key protects and to contain the impact if a key is compromised. NIST uses the term "cryptoperiod" to describe the time span during which a key is authorized for use. Limiting this window restricts the amount of data available for cryptanalysis and reduces exposure.
When setting rotation intervals, consider factors such as algorithm strength, data sensitivity, operating environment, and re-keying cost. Shorter cryptoperiods can improve security, but frequent rotations add operational complexity. The goal is a schedule that balances risk against practical overhead.
Hardware security modules
NIST defines a hardware security module (HSM) as “a physical computing device that safeguards and manages cryptographic keys and provides cryptographic processing.”
By protecting sensitive key material within secure hardware, HSMs can significantly reduce the risk of key exposure compared to software-only environments. They are widely used for high-value or highly regulated workloads such as payment processing, certificate authorities, and government systems.
Centralized key management
When keys are managed separately across teams or systems, inconsistencies creep in: keys may be generated using different methods, reused across environments, or not retired on time. Centralizing key management through a dedicated service or platform addresses these risks by maintaining a single key registry, enforcing consistent policies, and managing the full key lifecycle from a single point.
Centralization also simplifies auditing and reduces administrative overhead, making it easier to demonstrate compliance with security standards.
Access control and auditing
Limit who and what can access cryptographic keys. Apply role-based permissions so that only authorized personnel and systems can retrieve, use, or rotate keys, and enforce the principle of least privilege throughout.
Maintain detailed logs of all key operations, such as creation, access, rotation, and destruction. Regular audits of these logs help verify that key management policies are being followed and provide an evidence trail in case of a security incident.
Also read: What is access control? How it works and why it matters.
Challenges and limitations of symmetric encryption
While symmetric encryption is fast and efficient, it comes with trade-offs that need to be understood and managed.
- Scalability: Every pair of communicating parties needs its own unique secret key. In a small group, this is manageable, but the number of keys required grows rapidly: a network of 100 users would need nearly 5,000 unique keys. Generating, distributing, and tracking that many keys becomes a significant operational burden.
- No built-in non-repudiation: Symmetric encryption alone doesn't prove which party sent a message. Shared-key mechanisms, such as MACs, can help verify integrity and authentication between parties that share the key, but they cannot provide non-repudiation because both sides hold the same secret. For this reason, symmetric encryption is typically paired with digital signatures when non-repudiation matters.
- Key compromise has a broad impact: If a symmetric key is exposed, every piece of data encrypted under that key is compromised. Unlike asymmetric systems, where only one key in the pair needs protection, symmetric encryption puts all the risk on a single shared secret. This makes strong key management essential rather than optional.
Also read: Hashing vs. encryption: Key differences. The security of either approach depends on the algorithm, key length, and implementation. In practice, most systems combine both: asymmetric encryption securely exchanges a symmetric key, and symmetric encryption handles the bulk data protection.
Businesses should avoid relying on symmetric encryption alone for key distribution unless they already have a secure way to establish and manage shared keys. Proper key management controls are essential.
FAQ: Common questions about symmetric encryption
Is symmetric encryption more secure than asymmetric encryption?
Which symmetric encryption algorithm is used most often?
When should a business use symmetric encryption?
Can symmetric encryption protect data at rest and in transit?
What happens if a symmetric encryption key is exposed?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN