What is pretexting in cybersecurity? Definition, examples, and prevention
Understanding how pretexting works and how to recognize it can meaningfully reduce the risk of exposure. This article covers what pretexting is, how it plays out in real-world scenarios, and the practical steps you can take to prevent it.
Note: This information is for general educational purposes and not financial or legal advice.
What is pretexting?
Pretexting is a social engineering tactic in which an attacker uses false pretenses, often by impersonating a trusted person or role, to persuade a target to disclose sensitive information or take an action they otherwise wouldn't.
It’s typically targeted rather than broad: attackers research the target’s role and relationships, then pose as a believable party (for example, a colleague, vendor, bank representative, IT administrator, or government office). The pretext is designed to make the request seem routine or legitimate, such as asking to verify payment details or confirm account information, so the target complies without independent verification.
Depending on the scenario, the objective may include credentials, account details, or other personal or financial information that can enable fraud or identity theft. Pretexting often involves impersonation, but the two terms are not identical: impersonation is one technique used to support a pretext.
Related social engineering tactics
Social engineering is an umbrella category that includes multiple tactics attackers use to manipulate people into disclosing information, transferring money, or granting access. Common examples include:
- Phishing: Deceptive emails or messages that prompt actions such as clicking links, opening attachments, or sharing credentials.
- Vishing: Phone-based scams that attempt to extract information or persuade a target to act.
- Smishing: Text-message phishing scams that push links, callback numbers, or attempt to collect credentials or other sensitive information.
- Baiting: Enticing offers, such as “free” downloads or lost media, that lure a target into unsafe actions.
- Tailgating: Gaining physical access to restricted areas by following an authorized person in, often by appearing legitimate or claiming a routine reason to enter.
How do pretexting scams work?
Pretexting scams are often structured rather than purely random. A clear view of how they unfold makes it easier to spot inconsistencies and intervene before damage occurs.
Pretexting process
Pretexting often starts with reconnaissance. Attackers may collect personal and organizational details from public sources, leaked data, or social media, sometimes described as open-source intelligence (OSINT), to understand a target’s role, relationships, and routines.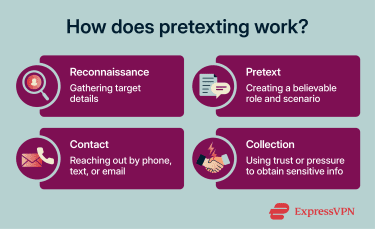
A pretext is commonly built from two elements: a character and a situation. The character is the role the attacker adopts, such as an executive, IT staff member, service provider, or someone the target is inclined to trust. The situation is the reason given for the request, sometimes generic (“an account update is required”), sometimes highly personal or tailored.
To bolster credibility, attackers may include supporting details, such as spoofed email addresses or phone numbers. In some cases, they may also use a compromised legitimate email account or phone number to send the message, making verification harder.
Once contact is established, the interaction is steered toward a concrete outcome, typically disclosure of confidential information or actions that enable further access. Because the request may seem routine at the time, the target may not realize what happened until the attacker uses the information.
What information do pretexters seek?
Targets vary, but pretexting commonly aims to obtain credentials, multi-factor authentication (MFA) codes or approvals, financial account details, and personally identifiable information (PII), including Social Security numbers (SSNs), that can enable fraud or identity theft. It may also seek confidential business information or actions that grant access to restricted systems.
Techniques used in pretexting
Pretexting techniques are methods used to build, support, and sustain a false story so the request feels legitimate and routine. The channels (email/phone/text) are often secondary to the story and context being presented.
- Role impersonation: Selecting a trusted identity that fits the target’s environment, such as IT, finance, a vendor, HR, or support.
- Scenario framing: Choosing a reason that sounds routine and plausible in context, for example, an account update, invoice question, access request, delivery issue, or compliance task.
- Credibility details: Using small specifics that make the story feel authentic, such as correct names/titles, internal terminology, vendor references, or believable timing.
- Gradual asks: Starting with a low-risk request, then moving to higher-risk requests once the target engages.
- Channel steering: Directing replies to attacker-controlled contact points (a provided number, message thread, portal, or link) instead of established channels.
- Workflow insertion: Positioning the request inside real business processes, such as payment changes, access approvals, password resets, or MFA re-enrollment, to reduce scrutiny.
- Pressure language: Using authority, urgency, or routine framing to discourage verification.
- Story consistency: Keeping the narrative coherent under questions and aligning any supporting artifacts with the scenario, for example, ticket references, invoices, and signatures.
Types of pretexting scams
Pretexting can appear in different types of scams depending on the target and context, but the common pattern is the same: impersonation plus a plausible reason for the request. Recognizing common variants helps identify suspicious requests earlier.
Account update and password reset scams
Attackers impersonate IT support or a service provider and claim an account requires an urgent update or reset. The aim is to obtain credentials, MFA codes, or other login approvals that can enable account takeover.
Business email compromise requests
Business email compromise (BEC) scams involve criminals posing as trusted business contacts (often executives, finance staff, or vendors) to push a high-impact request, such as a payment transfer or a change to banking details. In the 2024 Data Breach Investigations Report (DBIR), Verizon says pretexting incidents (most with BEC as the outcome) accounted for about one-quarter (24–25%) of financially motivated attacks in the past two years.
Fraudsters may send invoices that appear legitimate and attempt to redirect funds by changing account numbers or payment instructions, which can result in significant losses.
Also read: CEO fraud: How it happens and how to protect your business.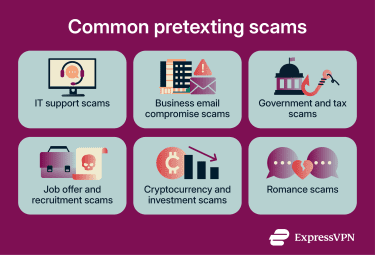
Government and tax scams
Scammers impersonate government agencies, including tax authorities, and claim that a tax debt is overdue or that a large refund is available. Threats and “pay now” pressure are common, and the goal is typically to extract personal or financial information or force immediate payment. The Internal Revenue Service (IRS) guidance also notes that impersonators often try to appear to be the IRS, whereas a real IRS contact generally begins with a letter or notice.
Also read: Tax identity theft: How it happens, how to spot it, and how to prevent it.
Job offer and recruitment scams
Scammers pose as recruiters or employers and use a fake hiring process to collect sensitive information. They often request personal identifiers (including SSN) and bank details under the pretext of employment paperwork or direct deposit setups. Some scams also pressure targets to pay upfront fees or send money for supposed equipment.
Also read: LinkedIn scams: How to spot and report them.
Cryptocurrency and investment scams
Investment scammers impersonate advisors, support staff, or public figures and steer victims toward high-return opportunities. These scams often result in irreversible transfers, and reported losses tied to crypto-related investment fraud are substantial in the FBI reporting.
Learn more: Read our articles on Coinbase scams, fake crypto wallets, and pig butchering scams.
Romance and social media scams
On dating sites or social media, scammers build trust over time and then use the relationship to pressure victims into sending money or sharing access. In the already mentioned FBI's 2024 OC3 report, the Confidence/Romance category recorded over $672 million in reported losses.
Also read: Military romance scams: How to protect yourself
Real-world pretexting examples
Understanding pretexting is easier when it is anchored to concrete, documented incidents:
In the workplace
In 2023, Reuters reported that MGM Resorts (a hotel and casino operator) suffered a major outage that sources cited by Reuters linked to the hacking group Scattered Spider and said multiple MGM systems remained paralyzed for three consecutive days as the company investigated. Bloomberg reported that the intrusion was believed to have involved attackers tricking the company’s IT service desk, a social engineering entry method consistent with Scattered Spider’s documented tactics described by the Cybersecurity and Infrastructure Security Agency (CISA).
MGM recovered by taking affected systems offline, restoring operations in phases, and bringing guest-facing systems back online over the following days. In an October 2023 Security and Exchange Commission (SEC) filing, the company said operations at its domestic properties had returned to normal and virtually all guest-facing systems had been restored.
Targeting personal accounts
In 2025, the Brooklyn District Attorney’s Office said a man was indicted in a phishing and social-engineering scheme that allegedly stole nearly $16 million from roughly 100 U.S.-based Coinbase users. Prosecutors said the man contacted users, posing as a Coinbase representative, warned that their assets were at risk from a hacker, and persuaded them to transfer cryptocurrency to a new wallet that the users believed they controlled but that was actually accessible to the defendant.
Coinbase said it worked with the Brooklyn District Attorney’s Office to support affected users and help identify the alleged scammer. The company also published scam-prevention guidance, stating that Coinbase will never ask users to move crypto to a “safe wallet,” request passwords or 2-step verification codes, or make unsolicited calls asking users to transfer funds.
Using customer support
The stock‑trading platform Robinhood said an unauthorized party “socially engineered a customer support employee by phone” by posing as a customer who needed assistance. Reuters reported Robinhood’s estimate that the attacker accessed email addresses for about 5 million users (with other subsets affected by additional data exposure).
Robinhood said it contained the intrusion, notified law enforcement, hired Mandiant to investigate, and informed affected customers. In 2025, the SEC also said Robinhood had settled charges tied in part to deficiencies in its cybersecurity and identity theft program.
The consequences of pretexting
Consequences vary by incident and may affect both individuals and organizations.
Impact on individuals
Individuals risk identity theft and financial loss when personal data or account access is obtained through deception. Recovery can involve time-consuming account remediation, disputes, and monitoring.
The Bureau of Justice Statistics (BJS) reported that 59% of identity-theft victims experienced direct financial losses (totaling $16.4 billion in 2021). At a broader consumer level, the Federal Trade Commission (FTC) reported $2.95 billion in losses to imposter (impersonation) scams in 2024, highlighting the scale of impersonation-based fraud affecting individuals.
Also read: Is identity theft protection worth it?
Impact on organizations
Organizations can face direct losses from unauthorized transfers, invoice diversion, or related fraud. Verizon’s 2024 DBIR reports that the median transaction amount in BEC cases was around $50,000 and places pretexting (often culminating in BEC) among major financially motivated attack patterns.
Incidents involving deception, fraud, or data exposure can also erode customer and partner trust and have longer-term impacts on brand and stakeholder confidence, particularly when the incident affects sensitive data or critical services.
How to identify a pretexting scam
Recognizing the signs of a pretexting attack is the first step toward preventing it. Here are common indicators and verification methods.
Common red flags to watch for
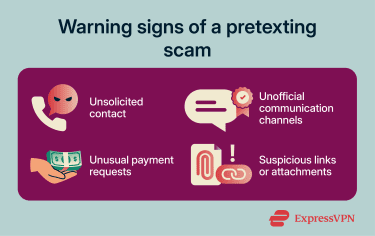
- Unsolicited contact or mismatched channels: Unexpected calls or messages from unknown numbers/senders or requests to switch from regular channels to personal messaging apps should be treated with skepticism.
- Unusual payment instructions: Requests to change payment details, send wire transfers, or pay via gift cards or cryptocurrency without independent verification are major indicators of a scam.
- Suspicious attachments or links: Emails or texts containing unexpected attachments or links, especially from domains with typos or unusual characters, can indicate spoofing and typosquatting.
What you shouldn’t share
To reduce risk, avoid sharing:
- Passwords or MFA codes: Legitimate organizations shouldn’t ask for passwords or one-time MFA codes.
- SSNs and full birthdates: Share this information only after verifying the identity, purpose, and official channel, and only when there is a legitimate need.
- Credit card security codes or PINs: Legitimate banks and card issuers generally don’t ask for these in unsolicited phone calls, texts, or emails.
- Other people’s personal details: Third-party personal information should be treated as sensitive and disclosed only through authorized, verified processes.
How to prevent pretexting attacks
While it’s impossible to eliminate all risk, organizations and individuals can reduce exposure by combining behavioral controls, such as training and verification, with technical controls, especially those that help reduce spoofing.
Security awareness training
Regular, role-specific security awareness training helps staff recognize pretexting patterns and follow consistent reporting and escalation procedures. Training can be strengthened through scenario-based exercises that reflect the real requests employees receive, such as payment changes, password resets, and vendor access requests.
Also read: Employment identity theft: What it is and how to protect yourself.
Strong verification and access controls
High-risk actions should require stronger identity checks and a trusted way to confirm the request. MFA helps, but the process also needs guardrails so resets or approvals don’t happen just because someone sounds convincing.
Also read: What is access control? How it works and why it matters.
Utilizing DMARC and related email protections
Email authentication reduces spoofing risk and improves the detection of unauthorized use of a domain. Examples include:
- Domain‑based Message Authentication, Reporting, and Conformance (DMARC): A protocol that lets a domain owner publish policies for how receivers should handle messages that fail authentication checks, and enables reporting to help monitor abuse.
- Sender Policy Framework (SPF): A Domain Name System (DNS) record that identifies which hosts are authorized to send mail using a domain in supported Simple Mail Transfer Protocol (SMTP) identities.
- DomainKeys Identified Mail (DKIM): A cryptographic signature added to outgoing email to help receiving systems verify that a message was authorized by the domain and was not altered in transit.
These protections work together: SPF and DKIM provide authentication signals, while DMARC builds on them to tell receiving systems how to handle messages that fail those checks and to provide reporting.
Reporting and response protocols
Organizations should establish clear reporting paths for suspicious requests and ensure that response teams can act quickly (for example, for credential resets, access reviews, and containment). Written plans can also define when to involve legal counsel and how external communications should be handled.
Help desk and vendor procedures
Help desks and customer service teams should follow standardized identity-verification steps and avoid making sensitive changes based solely on inbound requests. Vendor access should be restricted to approved methods, with verification procedures that don't rely on contact details provided during the same interaction.
What to do if you suspect pretexting
If you suspect pretexting, the priority is to stop further disclosure and preserve enough detail for investigation and reporting.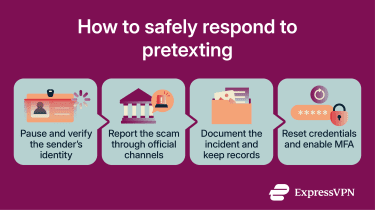
Stop the interaction and verify
End the interaction and don’t provide additional information. Verify the request through a trusted channel rather than using contact details included in the message.
Report and escalate quickly
Report the attempt through internal channels (for example, a supervisor or IT/security team) so that blocking and review steps can begin. External reporting requirements vary by sector and jurisdiction, and individuals may also be able to report scam attempts through consumer-protection or cybercrime reporting channels.
Also read: How to report phishing.
Document details for investigation
Record the time, contact method, sender details, phone numbers or email addresses used, and any messages, attachments, or links received. This helps support the investigation and any subsequent reporting.
Reset credentials and monitor accounts
If you shared any credentials, MFA codes, or sensitive information, secure affected accounts immediately and monitor for unusual activity. If you reused the password elsewhere, change it there too. For organizations, security teams should also check for any compromise beyond the initial request.
FAQ: Common questions about pretexting
What's the difference between pretexting and phishing?
What are the 4 Ps of phishing?
Is pretexting illegal?
How does pretexting lead to identity theft?
What steps can businesses take to prevent pretexting?
Why does pretexting work on people?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN