What is personal information? Definition, examples, and protection
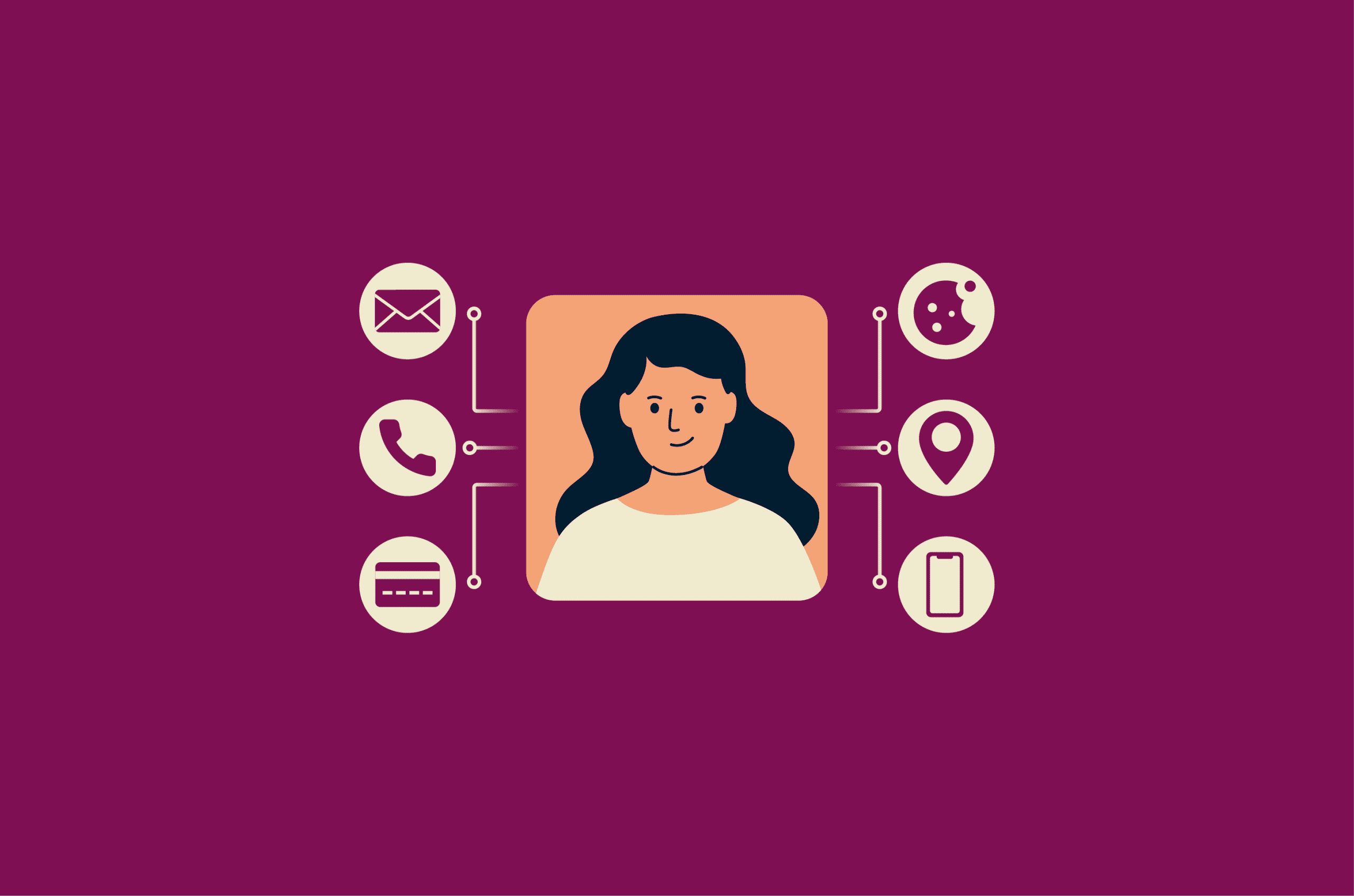
Every time someone signs up for an online account, enters a shipping address, or logs into an app, they share pieces of personal information.
In this guide, we break down what counts as personal information, how it's categorized, how it's collected and shared, and what protections apply under major privacy laws.
What is personal information?
The exact definition varies by law, but the core idea is similar across many privacy frameworks. Some laws describe personal information as data that relates to an identified or identifiable person, even when the information doesn’t identify that person by itself. Others define it as information that can reasonably be linked to a person or household.
Names, phone numbers, and email addresses are clear examples, but the category goes beyond obvious identifiers. An IP address, a browser cookie, or a combination of ZIP code and date of birth may also qualify when they can reasonably be linked to a person.
What doesn’t count as personal information
Information doesn’t qualify as personal information when it can’t reasonably be linked to an identifiable person. Data that has been truly anonymized, meaning re-identification is no longer reasonably possible, generally falls outside the scope of privacy law definitions.
Data that has only been pseudonymized may still be treated as personal information under many privacy laws. In pseudonymized data, identifying details are replaced but could still be restored using additional information.
Aggregated statistics (like the average age of users on a platform) also don’t count as long as no one can be singled out from them.
Some laws also exclude certain categories of public records. Under the California Consumer Privacy Act (CCPA), this can include information lawfully made publicly available from government records. This may include records such as property filings or professional licenses.
Still, data that appears anonymous or public in isolation can qualify as personal information if it’s combined with other information that makes someone identifiable.
Personal information vs. personally identifiable information
“Personal information,” “personal data,” and “personally identifiable information” (PII) are used in different legal contexts, and their definitions depend on the specific law being applied.
PII is commonly used in U.S. federal law and corporate compliance programs, but it lacks a single, universal definition across all U.S. legal contexts. It often refers to information that identifies a person, such as a full name, Social Security number (SSN), passport number, or biometric record.
“Personal data” under the EU’s General Data Protection Regulation (GDPR) and “personal information” under California’s CCPA are defined broadly. They include direct identifiers as well as certain indirect identifiers, such as online identifiers, that can relate to an identifiable person. The CCPA definition also extends to information linked to a household.
The term used in a privacy policy or breach notification usually reflects the legal framework under which the organization is subject.
Types of personal information
Many privacy laws group personal information by category, with stricter requirements applied to higher-risk data.
Basic personal identifiers
Full names, home addresses, email addresses, phone numbers, and dates of birth are the most commonly collected forms of personal information. Individually, some of these may not uniquely identify a person, but in combination, they can. These details are routinely collected during account creation, purchases, and employment applications.
Identification numbers and records
Government-issued identification numbers, including Social Security numbers (SSNs), passport numbers, driver's license numbers, and tax IDs, are unique to each person and difficult to change if compromised. A stolen SSN, for example, can be used to open fraudulent credit accounts, file false tax returns, or obtain services under someone else's identity.
Technical identifiers and online data
IP addresses, device IDs, browser cookies, advertising identifiers, browsing history, search history, and precise geolocation data fall into this category. How they're classified depends on jurisdiction.
Under the GDPR, online identifiers (including IP addresses) are considered personal data because they can identify a person. California's CCPA also lists IP addresses as a category of personal information.
In other U.S. frameworks, whether an IP address qualifies may depend on whether it can reasonably be linked to a specific person or household, based on how it's collected and stored.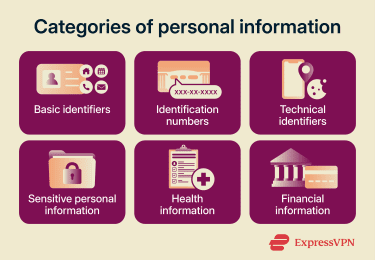
Sensitive personal information
The definition of sensitive personal information varies by law.
Under the GDPR, “special category” data includes information revealing racial or ethnic origin, political opinions, religious or philosophical beliefs, and trade union membership. It also covers genetic data, biometric data used for identification, health data, and data about a person’s sex life or sexual orientation. Processing this data is prohibited unless a specific legal basis applies, such as explicit consent.
The California Privacy Rights Act (CPRA) introduced a defined category of “sensitive personal information.” It includes SSNs, driver’s license numbers, precise geolocation, and financial account credentials. Similarly to GDPR, it also covers racial or ethnic origin, religious beliefs, genetic data, and biometric information, as well as the contents of mail, email, or text messages (unless the business is the intended recipient).
California consumers can direct businesses to limit the use and disclosure of sensitive personal information. Its use must be restricted to what’s necessary to provide the requested service.
Health-related information
Medical records, prescription information, and health data from apps or wearable devices can qualify as health data under the GDPR, which treats health data as a special category of personal data. In California, the CPRA treats personal information collected and analyzed concerning a consumer’s health as sensitive personal information.
In the U.S., the Health Insurance Portability and Accountability Act (HIPAA) governs how covered healthcare entities and their business associates handle protected health information. Health data collected outside HIPAA-covered entity or business associate relationships may instead be subject to general consumer privacy laws, such as the CCPA.
Financial information
Financial information can include bank account details, payment card data, credit reports, loan records, and transaction histories.
Under California’s CPRA, certain financial data (such as a financial account, debit card, or credit card number combined with required access credentials) qualifies as sensitive personal information.
In the U.S., the Gramm-Leach-Bliley Act (GLBA) requires covered financial institutions to explain their information-sharing practices and protect customer financial information.
How personal information is collected and used
Most people share personal information knowingly at some point, whether by filling out a form or creating an account. Collection also occurs in the background through tools and systems that automatically record activity.
How companies collect personal information directly
When someone creates an account, makes a purchase, applies for a job, or fills out a contact form, they provide information directly. The type of data collected depends on the service. An online retailer needs a shipping address. A bank may require identity documents. A job application can include employment history, education, and references.
How personal information is collected passively
Personal information is also collected without the individual's direct input. Websites use cookies and tracking pixels to record browsing activity. In many cases, these identifiers can be linked to a user or device, allowing individuals to be identified or profiled.
Mobile apps may request access to location data, contacts, or device identifiers. Analytics platforms compile interactions across sessions, and internet service providers (ISPs) may be able to see which domains a user visits, depending on how DNS requests and network traffic are handled.
Why companies collect personal information
Companies collect personal information to provide services, verify identity, process payments, and help prevent fraud. They also use it for analytics, product development, content personalization, and advertising.
In many cases, companies are less interested in a person as an individual than in placing them in commercially useful categories, such as likely buyers of certain products or people with particular habits or interests. To do this, they collect and combine data points such as browsing activity, purchase history, and inferred preferences to build consumer profiles.
Therefore, the privacy concern is not usually that a company wants to know who you are for its own sake, but that it can infringe on your privacy in the process of creating detailed profiles and using them to shape the ads, recommendations, and content you see online.
Data brokers and third-party sharing
Data brokers aggregate personal information from public records, commercial transactions, social media activity, and other sources where the data may be collected or shared under applicable laws. They compile consumer profiles and license or sell them to other businesses.
Personal information can also be shared across companies through advertising networks, analytics platforms, and business partnerships. When someone interacts with one service, their data may be shared with multiple third parties.
Related: How to remove yourself from data broker sites
Privacy laws that protect personal information
Privacy laws define personal information and establish rules for how organizations collect, use, and protect it. Notable frameworks include:
- General Data Protection Regulation (GDPR): Applies across the EU / European Economic Area (EEA) and to organizations outside the region that target or monitor individuals there. Requires a lawful basis for processing personal data and grants rights such as access, deletion, and data portability.
- California Consumer Privacy Act (CCPA) / California Privacy Rights Act (CPRA): Applies to certain businesses handling California residents’ data. Provides rights to access, delete, and opt out of the sale or sharing of personal information, and introduces limits on the use of sensitive personal information.
- Health Insurance Portability and Accountability Act (HIPAA): Regulates the use and disclosure of health information by healthcare providers, insurers, and related entities.
- Gramm-Leach-Bliley Act (GLBA): Requires U.S. financial institutions to disclose how they handle customer data and to safeguard nonpublic personal information.
- Children's Online Privacy Protection Act (COPPA): Governs how online services collect and use personal information from children under 13 in the U.S.
- U.S. state privacy laws: States such as Virginia, Colorado, Connecticut, and Texas have enacted laws that provide consumer rights similar to the CCPA, including access, deletion, and opt-out rights.
- Personal Information Protection and Electronic Documents Act (PIPEDA): Applies to private-sector organizations in Canada and governs how personal information is collected, used, and disclosed.
Related: Laws for deleting your personal data from the internet
How to protect your personal information
Privacy laws such as the ones listed above place obligations on companies that handle personal information. Individuals also have tools and practices available to reduce their own exposure.
How businesses are required to protect personal information
Most major privacy frameworks require companies that collect or process personal information to meet specific obligations. The details vary by law, but common requirements include:
- Data minimization: Companies should collect only the personal information necessary for the stated purpose. Under the GDPR, this is an explicit legal requirement. The CCPA requires that collection be reasonably necessary and proportionate to the purpose disclosed to the consumer.
- Retention limits: Personal information should not be kept longer than necessary. Once the purpose for collection has been fulfilled, companies are generally expected to delete or de-identify the data unless there is a legal, contractual, or operational reason to retain it.
- Security measures and access controls: Companies must implement reasonable safeguards to protect personal information from unauthorized access, disclosure, or loss. This can include restricting internal access for employees who do not need it.
- Encryption and pseudonymization: The GDPR specifically references them as measures that can reduce risk. Encryption makes data unreadable without a key.
- Breach notification: Many privacy laws require companies to notify affected individuals when a data breach involving personal information occurs. Whether notification is required may depend on the type of data involved, the level of risk or harm, and the applicable law. In some cases, regulators must also be notified. Timelines vary by law.
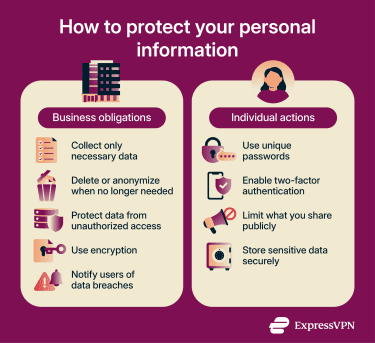
How individuals can protect their personal information
The choices individuals make about passwords, sharing habits, and storage also affect how much personal information is exposed and to whom.
Strong passwords and two-factor authentication
Using a unique, complex password for each account reduces the risk of unauthorized access. A password manager like ExpressKeys can generate and store these, so you don't need to memorize them.
Two-factor authentication (2FA) adds a second verification step, typically a code from an authenticator app or a hardware key. This makes it harder for an attacker to access an account, even with the password.
Safer sharing on social media
Social media profiles often contain personal information that users share voluntarily: full names, birthdays, locations, workplace details, and photos that may include metadata like GPS coordinates. This information can be used in social engineering attacks or identity theft.
Reviewing privacy settings on each platform, limiting what's visible publicly, and being selective about what you post can reduce exposure.
Secure storage for personal information
Sensitive documents such as tax returns, identification scans, and financial records should be stored in encrypted locations rather than in unprotected folders or cloud drives. Encryption makes data unreadable without the correct key, even if the device is lost or stolen. Storing sensitive information in plaintext files, email drafts, or shared documents increases the risk of exposure.
What to do in case of a data breach
If you receive a data breach notification or discover through a dark web scan that your credentials have been exposed, change the passwords for affected accounts immediately. If financial information was involved, monitor your bank and credit card statements for unauthorized transactions.
A fraud alert notifies lenders to verify identity before issuing credit. A credit freeze restricts access to your credit report, making it harder for someone to open accounts in your name. Either can be placed with the major credit bureaus (Equifax, Experian, TransUnion).
In the U.S., individuals can report identity theft and create a recovery plan at IdentityTheft.gov, maintained by the Federal Trade Commission (FTC). The FTC also accepts fraud reports at ReportFraud.ftc.gov. These tools are primarily for reporting identity theft or fraud affecting an individual, rather than for filing complaints about a company's handling of personal data.
In the EU, complaints can be filed with the relevant data protection authority.
To proactively check whether your personal information is exposed, you can search for your name, email address, or usernames in public search results, check breach-notification services such as ID Defender, and review data broker sites that may list your information. You can also take steps to reduce your digital footprint.
FAQ: Common questions about personal information
What is an example of personal information?
Is it safe to share personal information online?
What is the difference between personal information and sensitive data?
What is the difference between personal information and PII?
How can I protect my personal information?
Who can access my personal information?
Where can I report a data breach of my personal information?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN