Your comprehensive guide to cyber threat monitoring
As cyberattacks grow more frequent and complex, organizations need clear and persistent visibility into their environments to identify threats before they escalate. Cyber threat monitoring helps address that challenge by observing networks, systems, and digital activity for signs of malicious behavior.
This guide explains how cyber threat monitoring works and why it matters for modern cybersecurity. It outlines common monitoring tools, core processes used by security teams, and practical best practices that strengthen defenses.
What is cyber threat monitoring?
Cyber threat monitoring is the continuous process of collecting, analyzing, and acting on security data from across an organization's digital environment to detect malicious activity, suspicious behavior, and emerging threats as early as possible.
Instead of responding to incidents after they occur, it allows security teams the chance to identify cyberattacks in progress and respond faster, often reducing the damage they can cause.
Why is cyber threat monitoring important?
Modern organizations rely on interconnected systems, cloud services, and remote work environments. This creates more opportunities for attackers to exploit vulnerabilities or steal data.
At the same time, the frequency of cyberattacks continues to rise. According to Checkpoint's 2026 Cyber Security Report, organizations faced an average of 1,968 cyberattacks per week in 2025, an 18% year-over-year increase.
Globally, attacks are occurring at an alarming rate. Some estimates suggest more than 2,200 cyberattacks occur every day, or roughly one every 39 seconds. Without active monitoring, many of these threats can remain hidden for long periods.
Cyber threat monitoring helps organizations perform faster investigations, reduce potential damage, and stay aware of emerging risks by achieving the following objectives.
Reduce dwell time and attack impact
Dwell time refers to how long an attacker remains inside a system before being detected. The longer attackers go unnoticed, the more opportunity they have to steal data, move through systems, or disrupt operations. Cyber threat monitoring helps shorten this window by identifying suspicious activity early.
When threats are detected sooner, security teams can isolate affected systems, investigate incidents, and limit how far attackers can move within the environment.
Improve visibility across the attack surface
An attack surface refers to all the systems, devices, accounts, and applications that attackers could potentially target. As organizations adopt cloud services, remote work tools, and connected devices, this attack surface continues to grow.
Cyber threat monitoring helps organizations maintain visibility across these environments, enabling security teams to identify unusual patterns in network activity, account behavior, and system events that might otherwise go unnoticed.
Support compliance and business resilience
Many industries must comply with cybersecurity and privacy requirements that expect organizations to protect sensitive data, maintain appropriate security controls, and respond effectively to incidents.
For example, frameworks such as the General Data Protection Regulation (GDPR) require organizations that process personal data to implement appropriate technical and organizational measures to ensure security appropriate to the risk. In the U.S., similar requirements exist under laws such as the California Consumer Privacy Act (CCPA), which is primarily a privacy law but also intersects with data security obligations and breach-related liability. Cyber threat monitoring can support these obligations by helping organizations:
- Detect suspicious activity that could signal a breach.
- Investigate incidents and document response actions.
- Demonstrate that security controls are actively maintained.
Beyond regulatory requirements, monitoring also supports business resilience. By identifying threats early and responding quickly, organizations can reduce downtime, protect customer data, and maintain trust during security incidents.
How does cyber threat monitoring work?
Although the exact approach may vary between organizations, the process generally follows a similar pattern.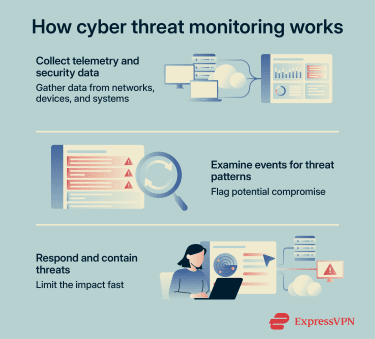
Collect telemetry and security data
The first step in cyber threat monitoring involves gathering information from across an organization’s digital environment. This information is commonly referred to as telemetry, which describes technical data generated by systems, applications, and devices during normal operation. Telemetry provides a detailed record of activity that security teams can review to identify unusual patterns or suspicious behavior, and other potentially adverse events.
Analyze events for indicators of compromise
After gathering telemetry data, the next step is to analyze it for signs of malicious activity. These may include indicators of compromise (IOCs), such as unusual login activity, unexpected data exfiltration, or unknown software running on a device, as well as anomalies and behavioral patterns associated with attacker activity.
This analysis usually draws on threat intelligence feeds to match observed activity against known attacker tactics, techniques, and procedures.
Prioritize alerts and investigate incidents
With potential threats identified, security teams must determine which alerts require immediate attention. This is necessary because security teams can receive a high volume of alerts daily, not all of which represent genuine threats.
Respond and contain threats in real-time
Organizations must act quickly to limit the impact once they identify a confirmed threat. Rapid response helps prevent attackers from gaining deeper access to systems or spreading malicious activity across the network. Containment actions may involve isolating affected systems, blocking suspicious connections, or disabling compromised accounts. These actions help stop malicious activity while security teams continue investigating the incident and work toward containment and recovery.
What types of threats should you monitor and where?
The threat landscape is broad and constantly evolving. Current reporting shows that ransomware and credential abuse remain major risks. Verizon’s 2025 Data Breach Investigations Report found that ransomware was present in 44% of the breaches reviewed, while credential abuse remained the most common initial access vector. In Verizon’s Basic Web Application Attacks pattern, about 87% of breaches involved the use of stolen credentials
These threats can originate from a variety of sources, including compromised devices, targeted user accounts, malicious insiders, or activity occurring entirely outside an organization's network. As such, many organizations monitor the following vectors.
Network and endpoint threats
Network and endpoint threats target an organization's infrastructure and the devices connected to it. Network threats specifically involve suspicious activity moving across a network, while endpoint threats affect individual devices, such as laptops, servers, and mobile phones.
Endpoint threats are particularly serious because compromised devices can provide attackers with a foothold for malware, data theft, or lateral movement to other systems. Common network and endpoint threats include:
- Malware infections: Malicious software can run quietly on a device and perform harmful actions, such as stealing information or disrupting systems.
- Suspicious network traffic: Unusual communication between systems can indicate command-and-control (C2) activity, lateral movement, or unauthorized data transfers.
- Unauthorized software or processes: Unknown programs running on devices may signal that malware or attacker tools have been installed.
Identity and access threats
Many modern cyberattacks focus on user accounts rather than software vulnerabilities alone. If attackers gain access to legitimate credentials, they can often enter systems while appearing to be authorized users.
These threats are commonly referred to as identity-based attacks because they involve the abuse of legitimate accounts and permissions. Identity and access threats often involve situations like:
- Stolen login credentials: Passwords obtained through phishing or data breaches can allow attackers to sign in as legitimate users.
- Account takeover attempts: Attackers may repeatedly try to access accounts or attempt logins from unusual locations.
- Privilege misuse: An account with elevated permissions may be abused to access sensitive systems or data.
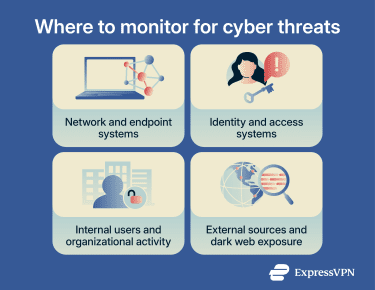
Insider threats and human risk
Not all cyber threats originate from external attackers. In some cases, risks come from people who already have access to systems. These are known as insider threats. An insider threat can involve employees, contractors, or partners who misuse their access intentionally or accidentally. The National Counterintelligence and Security Center defines insiders as trusted individuals who may use their authorized access to cause harm.
This type of risk is more common than many organizations expect. According to Cybersecurity Insiders’ 2024 Insider Threat Report, cited by BM, 83% of organizations reported at least one insider attack in the last year. Human risk often appears in several forms, including:
- Accidental data exposure: Sensitive files may be shared with the wrong recipients or uploaded to unsecured platforms.
- Policy violations: Employees might install unauthorized software, reuse weak passwords, or bypass security controls for convenience.
- Malicious actions: A trusted individual may deliberately steal, leak, or damage organizational data for personal, financial, or competitive reasons.
Insider threats are especially challenging because insiders often already have authorized access, which can make suspicious activity harder to distinguish from normal behavior.
External threats and dark web exposure
Some cyber risks exist outside an organization’s own systems. Attackers may share stolen information or discuss planned attacks on underground online communities, usually on the dark web. The dark web generally refers to intentionally hidden services that are not indexed by standard search engines and often require specialized software, such as Tor, to access.
Examples include:
- Stolen credentials appearing online: Usernames and passwords from previous breaches may be traded or sold.
- Leaked company data: Confidential information may surface on forums or file-sharing sites.
- Discussions about targeting organizations: Attackers sometimes advertise access to compromised systems or discuss future attacks.
Dark web monitoring can help reveal early warning signs of potential attacks, and tools like ExpressVPN Identity Defender’s ID Alerts can notify users when exposed personal information appears in known breaches or data leaks. This ExpressVPN product is currently available only to eligible Advanced and Pro subscribers in the U.S.
Which tools are used for cyber threat monitoring?
Cyber threat monitoring relies on a combination of security tools that collect data, analyze activity, and highlight suspicious behavior. Each tool focuses on a different part of an organization’s environment, such as user accounts, network traffic, or individual devices. Below are some of the most common tools used to support cyber threat hunting.
SIEM and log management platforms
Security information and event management (SIEM) platforms collect and analyze security data from across an organization’s systems. These platforms bring together information from many sources and store it in one central location.
SIEM tools primarily work with logs, which are records that systems generate whenever certain events occur. These records may include login attempts, software activity, or system configuration changes. A SIEM platform helps organizations:
- Aggregate data from multiple systems: Logs from servers, applications, and security tools are gathered in one place.
- Identify unusual patterns: The system analyzes collected data to detect activity that may indicate suspicious behavior.
- Provide a centralized view of security events: Analysts can review activity across the environment without checking each system separately.
EDR and XDR solutions
Endpoint detection and response (EDR) solutions monitor individual devices, such as laptops, mobile devices, and servers, that connect to the organization's network. These tools continuously track activity on these devices and analyze events to detect suspicious behavior or potential threats. When unusual activity is detected, the system alerts security teams and may also initiate response actions, such as isolating an infected device or stopping malicious processes.
Extended detection and response (XDR) expands this approach by integrating multiple security systems. Instead of focusing only on endpoints, XDR collects and correlates information from endpoints, network traffic, cloud environments, email systems, and user activity to provide broader visibility into potential security threats.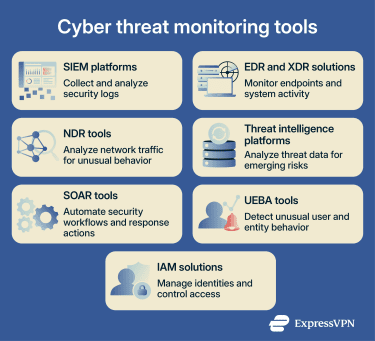
Network detection and response (NDR) tools
NDR tools analyze patterns in network traffic and communications between systems to identify suspicious behavior. They often use behavioral analysis and anomaly detection to identify activity that deviates from normal network behavior. Examples can include unusual connections between internal systems, unexpected communication with external servers, or abnormal data transfers that may signal a potential security threat.
This makes them particularly useful for detecting threats such as lateral movement within a network or communication with attacker-controlled infrastructure.
For a closer look at how NDR compares with broader detection platforms, see the differences between NDR and XDR solutions.
Threat intelligence platforms (TIP)
Threat intelligence refers to information about known cyber threats, attacker tactics, techniques, and procedures (TTPs), and indicators of malicious activity, such as IP addresses, domains, or file hashes. This information helps organizations recognize patterns linked to previous attacks.
TIPs are tools designed to collect, manage, and analyze threat intelligence from multiple sources, including internal security tools, commercial threat feeds, and open-source intelligence. Some of these tools use AI and machine learning to process large volumes of data and highlight potential emerging risks.
TIPs can support security teams by:
- Identifying known malicious infrastructure or attacker activity.
- Detecting patterns associated with previously reported cyber threats.
- Providing context that helps analysts better understand and prioritize potential risks.
SOAR and automation tools
Security orchestration, automation, and response (SOAR) platforms help coordinate security activities across different tools and systems within an organization’s security environment. Their primary goal is to streamline security operations and reduce analysts' manual workload, and support faster incident response.
SOAR platforms automate routine tasks and structure investigation workflows. Instead of handling every step manually, security teams can rely on predefined playbooks to perform repetitive tasks such as collecting data, enriching alerts, or initiating response procedures.
User and entity behavior analytics (UEBA) tools
User and entity behavior analytics (UEBA) tools focus on analyzing the behavior of users and systems within an organization’s environment. These tools usually rely on advanced analytics and machine learning to establish a baseline of normal activity and monitor for deviations that may indicate potential security risks.
This allows them to identify unusual actions that might otherwise go unnoticed. An example would be a user accessing sensitive data at unusual times, logging in from unexpected locations, or transferring unusually large amounts of data.
IAM solutions
Identity and access management (IAM) solutions help organizations control who can access systems, applications, and data by ensuring individuals can access only the resources necessary for their roles.
They do this by managing digital identities and enforcing access policies. This process typically involves authentication methods such as passwords, two- or multi-factor authentication (2FA/MFA), or other identity verification mechanisms.
IAM tools also generate valuable records related to authentication, access, and account activity. These records can reveal patterns that may indicate unauthorized access, misuse of privileges, or other suspicious account behavior.
Best practices for effective cyber threat monitoring
Effective cyber threat monitoring requires more than deploying security tools. Organizations need clear processes to identify real threats, respond efficiently, and improve their security posture. Below are several important practices that support effective cyber threat monitoring while keeping alerts manageable for analysts.
- Define detection use cases and escalation paths: Detection use cases specify the types of suspicious activity to watch for, while escalation paths outline who handles alerts and how incidents are investigated. Aligning these with Zero Trust principles can help organizations continuously verify access requests and apply least-privilege controls.
- Implement layered monitoring: Layered monitoring combines UEBA, IAM, external exposure monitoring, and network traffic analysis. A central security analytics platform can correlate these indicators, helping detect complex threats that a single tool might miss.
- Tune alerts to reduce false positives: Adjusting detection rules and alert thresholds helps minimize unnecessary notifications, allowing analysts to focus on events that are more likely to indicate real threats.
- Automate repetitive triage tasks: Automating routine steps such as gathering system data, reviewing related events, and enriching alerts can speed up investigations and reduce manual work. Where appropriate, AI-assisted tools can support initial triage and intelligence gathering, while human analysts remain responsible for higher-risk decisions.
- Validate defenses with simulations and testing: Regular testing and simulations help confirm that monitoring systems can detect realistic attacks and that detection rules work as intended.
- Review incidents to improve detection logic: Post-incident reviews provide insight into attacker behavior and monitoring effectiveness, helping teams refine rules and improve alert accuracy over time.
- Train staff: Ongoing training helps analysts and security teams stay current on threat trends, tools, and investigation techniques. Training also reinforces best practices for interpreting alerts, responding to incidents, and using monitoring platforms effectively.
Common challenges in cyber threat monitoring
Cyber threat monitoring isn’t without difficulties.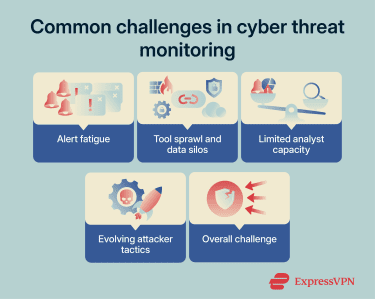
Alert fatigue
Monitoring systems can generate a large number of alerts every day. Although these alerts are meant to highlight suspicious activity, many may turn out to be harmless. When analysts must review too many alerts, it can lead to alert fatigue, making it difficult for security teams to prioritize which alerts require immediate attention.
Tool sprawl and data silos
Many organizations rely on multiple security tools to monitor different parts of their digital infrastructure. While these tools provide valuable visibility, using too many separate systems can create complexity. This situation is often called tool sprawl.
When tools operate independently and don’t easily share data, information can become isolated in data silos. This makes it harder to detect threats across the entire environment and slows down incident response.
Limited analyst capacity
Cyber threat monitoring often depends on skilled analysts who review alerts, investigate suspicious activity, and determine whether a threat is present. However, many organizations continue to face skills and staffing gaps in cybersecurity roles.
This shortage can limit how effectively monitoring programs operate. When teams are understaffed, analysts may struggle to keep up with incoming alerts or investigations.
Evolving attacker tactics
Cyber attackers constantly adapt their techniques to avoid detection, so monitoring strategies that worked in the past may become less effective as attacker behavior changes. This constant evolution means monitoring systems must be regularly updated and refined. Detection rules, threat intelligence, and monitoring strategies need ongoing adjustment to ensure they remain effective against emerging threats.
FAQ: Common questions about cyber threat monitoring
What is the difference between threat monitoring and threat detection?
How often should cyber threats be monitored?
Can small businesses use cyber threat monitoring?
What is the difference between SIEM and EDR?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN