What is cyber insurance and how does it work?
Cyber insurance is a type of coverage designed to protect businesses and individuals from the financial losses usually caused by cyber incidents. As data breaches, ransomware attacks, and online fraud become more common, understanding how cyber insurance works is an essential part of modern risk management.
In this guide, we explain why cyber insurance exists, what kinds of risks it covers, and how insurers may respond when something goes wrong. It also breaks down common coverage options and policy limitations, helping clear up confusion around a subject that is often misunderstood yet increasingly critical in a digital-first world.
Please note: This information is for general educational purposes and not financial or legal advice.
What is cyber insurance?
Cyber insurance typically covers the aftermath of a cyber incident, including technical investigations, data recovery, legal obligations, regulatory requirements, and lost income due to operational disruption. It generally applies to events like data breaches, ransomware attacks, and other situations where digital systems or information are compromised.
According to IBM’s 2025 Cost of a Data Breach Report, the global average cost of a data breach is $4.4 million. Many of these costs can fall outside the scope of traditional insurance policies, and cyber insurance exists to address this gap. Simply put, its role is to help reduce the operational and financial impact of such incidents.
Who needs cyber insurance?
Organizations that handle sensitive data or rely on digital systems are the primary candidates for cyber insurance. This includes small businesses, corporations, and nonprofits.
Companies that manage customer information, payment data, or confidential records face even higher exposure. According to research by the EC-Council University (ECCU), the most targeted industries in the U.S. are healthcare, retail, education, and professional services. Organizations that operate at a national level are also potential targets of cyberterrorism.
One common myth is that cyber insurance is only necessary for large corporations. In reality, smaller organizations are often targets for cyberattacks because they tend to have fewer security resources.
Reports from the Identity Theft Resource Center show that roughly 81%, or about four out of five, small businesses surveyed experienced a security incident or data breach within a single year.
Another misconception is that cyber insurance replaces cybersecurity defense. Insurance doesn’t stop attacks from happening. Similarly, security tools like antivirus software don’t remove the need for coverage.
While individuals can technically purchase cyber insurance, it isn’t commonly used. That’s because personal cyber risks are usually smaller in scale and better covered by identity theft insurance.
For example, ExpressVPN’s Identity Defender offers personal identity theft insurance up to $5 million* for eligible losses. It also incorporates tools like ID Alerts and a Credit Scanner that monitor for signs of identity theft.
Note: Identity Defender is available to U.S. users on select plans.
What does cyber insurance cover?
There are many types of cyber insurance, and policies vary widely, but most focus on covering the financial and operational impact of cyber incidents.
Here’s a breakdown of the main types. You can also check out our comprehensive list of cyber insurance types for more detailed information.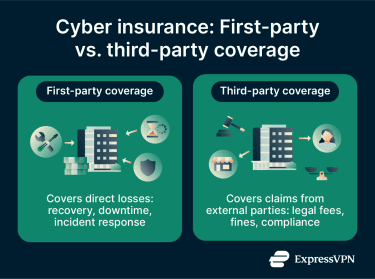
First-party coverage
First-party coverage applies to losses experienced directly by the affected organization. This includes cybersecurity spending tied to responding to an incident and getting operations back on track.
Third-party liability coverage
Third-party liability coverage addresses claims made by external parties affected by a cyber incident. This often involves customers, partners, or vendors whose data was exposed or misused. Coverage may also apply when an organization is accused of failing to protect sensitive information or meet legal obligations.
Additional services and protections
Many cyber insurance policies include support services beyond direct financial coverage.
- Access to cybersecurity experts for incident response.
- Legal guidance for compliance and regulatory issues.
- Public relations support to manage communication after an incident.
- Risk assessment tools to evaluate exposure.
- Security resources to monitor and identify potential data leaks.
These added protections can help organizations recover more effectively and maintain stability during complex cyber events.
Cyber insurance claims process
The process for cyber insurance claims generally involves structured steps that allow insurers to verify incidents, assess damages, and determine coverage under the policy.
Note: The processes below are provided for general guidance. For advice specific to your situation, consult with your insurance provider.
How the claim process typically works
Insurers usually outline the claims process in the policy itself, including who to contact, how quickly an incident must be reported, and what information is required. Many also provide a dedicated claims hotline, email address, or online portal, especially for cyber incidents that require a fast response.
With that said, the most common pattern is as follows:
- Identification and documentation of the incident: The organization confirms that a cyber incident has occurred and records key details. Important information includes when the incident happened, how it was discovered, and which systems or data were affected.
- Notification of the insurer: The insurer is formally informed about the incident within the timeframe required by the policy. Timely notification is typically essential for the claim to move forward.
- Submission of supporting information: Relevant documentation is provided to support the claim. This may include incident reports, system logs, or findings from third-party specialists.
- Claim review and assessment: The insurer reviews the submitted materials, asks for clarification or additional details where necessary, and evaluates whether the incident qualifies for coverage and at what level.
Common reasons claims might be denied
If a cyber insurance claim is denied, the organization won’t receive compensation for the reported losses. The denial notice typically explains the reasoning and references the specific section of the policy used to support the decision.
Common reasons include:
- Cybersecurity failures: If the organization is found to have neglected or misrepresented security controls required by the policy. For example, failing to use relevant security tools, update critical software, or patch known vulnerabilities.
- Unapproved third parties: If a breach happens under the remit of a third party that wasn’t approved or known about by the insurer.
- Lack of mitigation processes: If the correct steps weren’t taken to limit damage and costs immediately after an incident.
- Late or insufficient reporting: If a breach or attack isn’t reported within the required time stated by the policy, or if it doesn’t provide the required information.
- Policy limitations: If the incident happened outside the policy period, exceeds policy limits, or falls under any of the policy’s exclusions.
How appeals usually work
- Denial notice review: The appeal process begins with an examination of the denial notice. These notices usually provide a written explanation for the claim rejection, including the rationale for the decision and any available appeal procedures.
- Evidence collection: This stage involves gathering records and documentation related to the claim. The materials correspond to the insurer’s stated reasons for denial and provide additional context or clarification.
- Appeal submission: Appeal submission involves drafting a clear written request that addresses the insurer’s reasoning and includes relevant evidence.
Once the appeal is submitted, the insurer reviews and reassesses the claim based on the additional evidence and policy interpretation, then issues a revised decision.
Understanding policy limits and exclusions
What are policy limits?
Policy limits set the maximum payout the insurer will provide for a covered cyber event. Limits may apply per incident, annually, or for specific types of coverage like data restoration, legal costs, or business interruption. For example, a policy might cover up to $500,000 for first-party expenses and a separate $1 million for third-party liability.
What’s typically not covered?
Exclusions are circumstances where the insurer won’t provide coverage. Common exclusions in cyber insurance include:
- Insider threats: Intentional harm caused by employees or owners can fall outside of the cybersecurity remit. Some providers may cover insider threats but exclude damage caused by senior management or owners to prevent insurance fraud.
- Social engineering attacks: Manipulation techniques like phishing are often categorized as fraud or theft, rather than cyber incidents. Some insurers offer separate social engineering coverage for an additional cost.
- Known vulnerabilities: Cyber insurance is intended to cover unforeseen incidents. Pre-existing issues with systems or networks carry a higher risk and may not be covered.
- State-sponsored attacks: Many policies include exclusions for acts of war or nation-state cyber operations, though the scope and interpretation of these exclusions can vary.
- Injuries or property damage: Physical harm to equipment or employees usually isn’t directly tied to cyber incidents.
- Non-cyber-related network failures: Outages caused by internal errors, misconfigurations, or equipment failure are typically not covered by cyber insurance.
- Insurance that breaches local law: In some jurisdictions, certain regulatory fines or penalties may not be legally insurable.
Factors to consider when choosing a cyber insurance policy
Selecting a cyber insurance policy involves aligning coverage with an organization’s specific risks rather than price or popularity alone. The focus is on matching the policy to the types of threats relevant to the organization.
Assessing cybersecurity risk level
A cybersecurity risk assessment helps an organization understand how and where it’s exposed to cyber incidents based on how it uses technology and data. This step focuses on identifying what systems or information could be affected and how serious the impact would be. A clear view of risk makes it easier to choose coverage that matches real-world exposure rather than assumptions.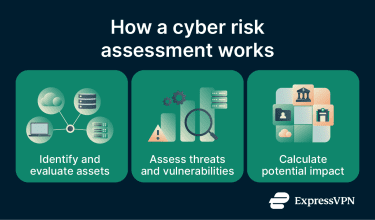
Comparing policies and providers
When comparing cyber insurance providers, cost isn’t the only deciding factor. Policy differences can include coverage limits, exclusions, available response support, and claim conditions.
Insurers may vary in experience, particularly with cyber-related incidents. Some providers focus exclusively on cyber risks, while others include cyber coverage as an add-on to traditional insurance.
Reporting requirements, response procedures, claim evaluation processes, and documentation expectations should also be examined to understand how the policy operates.
What insurers expect before offering coverage
Insurers typically assess how well an organization manages cyber risk before offering coverage. They expect a clear understanding of data handling and effective procedures for responding to incidents.
Many insurers require organizations to maintain a baseline set of cybersecurity measures. Implementing these controls may also reduce premiums or coverage restrictions.
Here are some examples:
- Password policies with complexity requirements and regular changes.
- Multi-factor authentication (MFA) for remote access and sensitive systems.
- Firewalls and antivirus software to block unauthorized access and detect malware.
- Regular software updates and patch management to fix security vulnerabilities.
- Data backup procedures to ensure recovery in case of ransomware or system failure.
- Employee training to recognize phishing, social engineering, and other common attacks.
FAQ: Common questions about cyber insurance
Is cyber insurance worth the cost?
Who needs cyber insurance?
What’s a typical example of a cyber claim?
Are there policies for specific threats like ransomware?
Can a cyber insurance claim be denied if my security controls are weak?
How do I find a reputable cyber insurance provider?
*The insurance is underwritten and administered by American Bankers Insurance Company of Florida, an Assurant company, under group or blanket policies issued to Array US Inc, or its respective affiliates, for the benefit of its Members. Please refer to the actual policies for terms, conditions, and exclusions of coverage. Coverage may not be available in all jurisdictions. Review the Advanced Tier Summary of Benefits and the Pro Tier Summary of Benefits.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN