What is credential stuffing? Understanding this cyber threat
Credential stuffing is a type of cyberattack where criminals use stolen usernames and passwords from one data breach to try to access accounts on other websites or services. It works because many people reuse the same login details across multiple services.
This article explains how credential stuffing works and what helps reduce the chances of falling prey to this type of cyberattack.
How credential stuffing attacks work
Credential stuffing operates at scale. Attackers gather large databases of leaked credentials from data breaches, malware infections, or phishing campaigns. They then use automated tools to submit those username and password combinations across various login forms in rapid succession.
The credentials are already valid somewhere, so what the attackers are checking is whether the same combination unlocks additional accounts. Even a low success rate can translate into thousands of compromised accounts when attempts are made in the millions.
This combination of reused credentials and automation is what makes credential stuffing so effective. As a result, it’s widely reported as one of the most common techniques used in account takeover attacks.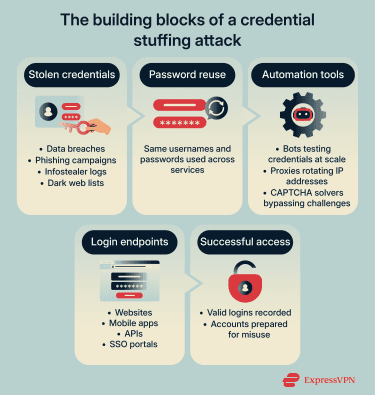
Credential stuffing vs. brute force attacks
A brute force attack attempts to guess a password without prior knowledge. Attackers try character combinations, common patterns, and word lists until something works.
Sometimes, credential stuffing is classified as a subset of brute force attacks because both involve repeated login attempts. However, the methods differ significantly.
Brute force attacks rely on guessing. Credential stuffing relies on previously compromised credentials.
A long, complex password can prevent a brute force attack. That same strong password isn’t protected in a credential stuffing campaign if it’s reused elsewhere.
Credential stuffing vs. password spraying
Password spraying targets many valid usernames on a single service using one common or likely password at a time. Before spraying begins, attackers typically gather a list of real usernames from public sources such as company staff directories, email address patterns (for example, firstname.lastname@company.com), data breach leaks, or other open-source intelligence (OSINT). They then try one password across that username list, pause to avoid lockouts and alerts, and repeat with another likely password later. The goal is to find at least one account with a weak or predictable password without drawing attention through repeated failures on any single account.
Credential stuffing, by contrast, uses real username–password pairs leaked in previous data breaches and tries each pair across many different services. The attacker isn’t guessing passwords; they are replaying credentials that are known to have worked somewhere before, betting that users reused the same password on other sites. Each credential pair typically maps to one real person, so the attack tests whether that individual reused their password across multiple services. However, credential stuffing is not a targeted attack against a single individual. In practice, attackers run this process at massive scale, replaying millions of leaked username–password pairs across multiple platforms at once.
Attack vectors used to target accounts
Any system that accepts a username and password can be targeted, including:
- Web login forms
- Mobile app authentication screens
- API authentication endpoints
- Single sign-on (SSO) portals
Examples of commonly targeted services
Attackers typically focus on services that offer financial value, store personal data, or have resale potential. These accounts can be resold in bulk or used directly for fraud, making them prime targets for credential stuffing campaigns. Frequently targeted categories include:
- Streaming platforms with paid subscriptions.
- Online shopping accounts with saved payment methods.
- Banking and fintech apps.
- Social media and email accounts.
- Gaming accounts with digital assets.
Risks and impact of credential stuffing
Credential stuffing often leads to account takeovers across multiple services when the same login details are reused. A single exposed credential can increase the risk of financial fraud, identity misuse, and unauthorized access to sensitive data for both individuals and organizations.
Account takeover and fraud
The most direct result of credential stuffing is account takeover. Since the attackers have the correct username and password, it won’t trigger any account alerts. Once they’re inside, it’s easy for them to change recovery emails, reset passwords, and prevent the real account owner from logging in. If the account contains payment methods, gift cards, loyalty points, or subscription access, the attackers can use or resell those assets almost immediately.
Financial platforms pose an even higher risk. Access to banking, fintech, or payment apps can allow direct fund transfers, fraudulent purchases, or money laundering through legitimate accounts. In many cases, victims only realize something happened after charges appear or access is lost.
Email and social media accounts are used to commit scams in a more indirect way: when attackers control an account, they can launch phishing and social engineering attacks that appear to come from a legitimate and trusted contact. Friends, family, coworkers, or customers are far more likely to trust a message that comes from a familiar source.
Regaining access can be time-consuming. It may involve password resets, identity verification checks, fraud disputes, and, in some cases, the suspension or permanent closure of the affected account.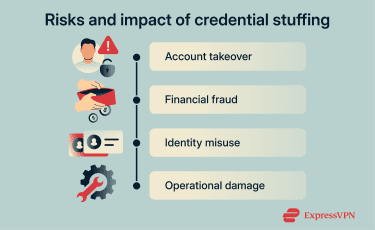
Consequences for organizations
For organizations, credential stuffing can give attackers access to company assets without having to bypass standard security measures. Employee accounts, administrative dashboards, and cloud services become entry points for deeper compromise.
Once inside, attackers may gain access to internal systems and sensitive resources, depending on the permissions of the affected account.
Even when attackers don’t go deeper, the attack itself creates operational impact. Massive volumes of automated login attempts can strain infrastructure, trigger fraud investigations, overwhelm security monitoring systems, and consume incident response resources. Organizations may spend significant time and money responding to an attack that never involved a technical breach, only reused credentials.
How to prevent credential stuffing attacks
While the consequences of credential stuffing can be severe, most cases can be prevented by following basic online security practices. With the right habits in place, credential stuffing becomes far less likely to succeed against you or your business.
How individuals can protect their accounts
Even if your credentials get stolen, there are steps you can take to reduce the chances of a successful credential stuffing attack.
Using unique passwords
Using a unique password for every account ensures that a breach in one service doesn’t expose others.
A reliable password manager is a convenient tool you can use to reduce this risk by generating and storing unique passwords for every account.
Identity monitoring tools
Continuous monitoring helps detect exposure before attackers can use stolen credentials. If your email address or login details appear in a breach, changing the affected password prevents attackers from reusing it elsewhere.
Tools like ExpressVPN’s Identity Defender monitor breach datasets and alert you when your personal information appears. This allows you to respond quickly by updating passwords and securing affected accounts. While breach monitoring doesn’t stop credential stuffing attempts, it reduces the risk of successful account takeover by helping you identify and fix exposed credentials before attackers can use them.
Enabling multi-factor authentication
Multi-factor authentication (MFA) adds a second barrier after the password. Even if attackers successfully log in with stolen credentials, they still need to complete the login with a second factor. Common MFA methods include:
- Authenticator apps that generate time-based one-time codes.
- Hardware security keys that must be physically present.
- Device-based biometrics such as fingerprint or facial recognition.
- Push notifications, sent to a trusted mobile device.
- SMS or email verification codes.
This stops many credential stuffing attempts from turning into full account takeovers. The credentials may still be valid, but access gets blocked at the second step.
However, if attackers already control an email account, they can intercept codes sent there and use them to change account settings. This is why phishing-resistant MFA methods offer stronger protection against credential stuffing attacks.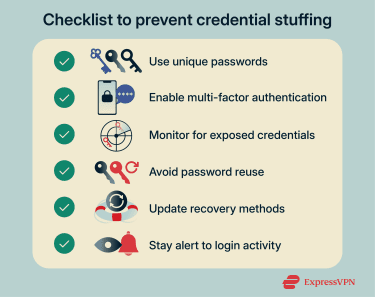
How businesses can prevent credential stuffing
Defense in organizations must focus on detecting abnormal login behavior and automated activity.
Rate limiting and bot detection
Credential stuffing is a volume attack. Attackers feed massive credential lists into login pages and wait for successes. Without limits, these tools can test thousands of username and password pairs per minute.
Rate limiting changes that dynamic. By restricting how many login attempts can occur within a short window from the same IP address or across many accounts, authentication systems slow the attack down dramatically. What would normally take minutes now takes hours or days, which makes the activity easier to detect and far less worthwhile for the attacker.
Combined with bot detection, which looks for patterns that don’t match human behavior, rate limiting forces automated tools to reveal themselves through speed, repetition, and abnormal traffic patterns rather than the credentials they use.
CAPTCHA and behavioral analysis
CAPTCHA challenges add friction that automated tools must overcome, which helps reduce large volumes of scripted login attempts. While they’re still useful, they’re not as reliable as they once were. Some attackers use CAPTCHA-solving services to bypass these challenges.
That’s why behavioral analysis plays an important role alongside CAPTCHA. Instead of relying on visual puzzles, these systems analyze how a visitor interacts with the login page, including typing rhythm, mouse movement, session timing, and navigation flow. Automated tools struggle to mimic these human patterns consistently.
Together, CAPTCHA and behavioral analysis help separate real users from automated credential testing, especially when used as part of a broader defense strategy
Monitoring and alerting on login attempts
Credential stuffing leaves very specific fingerprints. Some of the red flags to watch for include:
- A sudden spike in failed logins across many different accounts.
- Login attempts hitting thousands of usernames from a rotating set of IP addresses.
- Repeated login attempts coming from countries where the service has little or no user base.
- A short burst of login activity across many accounts followed by a small number of successful logins.
Reporting these behaviors allows IT teams to respond before attackers sort through results and start using the working accounts. Actions might include temporarily locking targeted accounts, forcing password resets, adding additional verification steps, or blocking suspicious IP addresses.
API and authentication security controls
Strong API and authentication controls help stop credential stuffing before login attempts succeed. These measures focus on validating credentials, limiting exposure, and enforcing strict access policies across all authentication points.
Organizations can integrate breach intelligence APIs that block passwords known to have appeared in previous leaks. If a user attempts to log in with a compromised password, the system can force a reset before access is granted. This directly prevents reused credentials from being accepted.
API security tools also ensure that only legitimate traffic can reach authentication endpoints. By inspecting request patterns, validating payload structure, and filtering abnormal traffic, these systems block automated tools from interacting freely with login systems.
Access management plays an important role as well. Reviewing user permissions and enforcing a least-privilege model limits what any single account can access if it becomes compromised. Combining this with a zero-trust approach, which requires continuous verification of every request, lessens the impact of successful credential testing.
These controls protect every authentication path where credentials might be tested.
FAQ: Common questions about credential stuffing
Can credential stuffing affect accounts that weren’t breached?
How do attackers get the stolen credentials?
How can I check if my credentials were exposed?
What tools can help defend against credential stuffing attacks?
For organizations, rate limiting, bot detection, behavioral analysis, and API authentication controls form the core defensive layers. These measures work together to eliminate the conditions that credential stuffing relies on.
How many login attempts are used in a credential stuffing attack?
Why don’t websites automatically block credential stuffing?
What does credential stuffing look like from a user’s perspective?
Can credential stuffing bypass CAPTCHA?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN