A beginner-friendly guide to confidential computing
Organizations have long had ways to protect data when it’s stored or sent across the internet using encryption. But there’s a catch: those protections usually stop when the data is actually being processed.
That’s because, in most systems, data has to be decrypted before it can be processed. In other words, it becomes readable to the processor and potentially visible to anything that controls the underlying hardware. If that system is compromised, sensitive data could potentially be exposed at the very moment it’s being used.
Confidential computing is designed to close this gap. This guide introduces the basics of confidential computing: how it works, where it’s used, and the key benefits it offers for both individuals and organizations.
What is confidential computing?
Confidential computing is a hardware-based privacy-enhancing technology (PET) that protects data while it’s being processed. It does this by creating a secure, isolated environment inside the processor where data can be computed on without being visible to the rest of the system.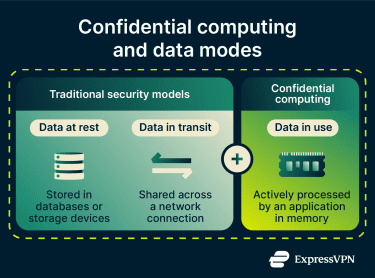
This includes the operating system, virtual machine, cloud provider, or anyone else with access to the machine, such as privileged users, even those with root access.
How does confidential computing work?
Confidential computing relies on two key components: trusted execution environments (TEEs) and remote attestation. Together, they ensure that data is both protected during processing and only handled by systems that can be trusted.
Trusted execution environment (TEE)
Confidential computing protects data while it’s being used by processing it inside a TEE, sometimes also known as a secure enclave.
A TEE is a protected area inside a processor that’s isolated from the rest of the system. This isolation is enforced by hardware (either physically or logically), which means even the operating system or other applications can’t access what’s happening inside it.
Here’s how it works in practice:
- Sensitive data is sent to the TEE in encrypted form.
- Inside the TEE, the processor decrypts the data.
- The data is processed securely.
- The results are encrypted again before leaving the enclave.
Because all of this happens within the processor’s protected boundary, the data isn’t exposed to the rest of the system at any point.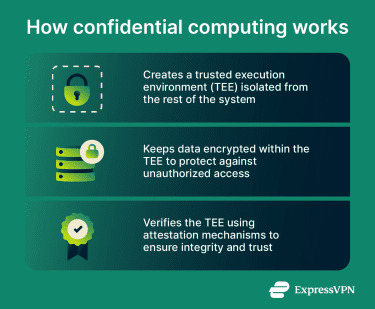
Remote attestation
Before sending sensitive data to a TEE, there needs to be a way to confirm that the environment is legitimate and hasn’t been tampered with. Without this protection, an attacker could set up a system that claims to be a TEE but it’s not.
Remote attestation solves this problem. It allows a TEE to prove that it’s genuine and running in a trusted state before any data is shared.
When a TEE starts up, the processor generates a cryptographic report of everything running inside it. This report is signed with a key that’s burned into the chip during manufacture, so it can’t be forged or replicated by software.
A remote system can verify this signature using the hardware manufacturer’s public key. This is a standard cryptographic signature check that proves the report was produced by genuine hardware.
The report also includes a set of values (register measurements) that reflect what code is running and how the enclave was started. The remote system must check that these values match what it expects for a trusted application.
If the signature is valid and the measurements match the expected values, the remote system can establish a secure channel and communicate with the enclave. If not, it won’t interact or send any data.
Real-world applications of confidential computing
Confidential computing is being used across many industries, including healthcare, AI platforms, financial services, and blockchain. Here’s how it helps organizations and users in practice.
AI, machine learning (ML), and large language models (LLMs)
Confidential computing allows AI providers to deploy and operate large language models (LLMs) and machine learning (ML) algorithms within secure, isolated environments. This can help reduce the risk of unauthorized access, tampering, data theft, and compliance issues.
For users, this means stronger privacy when interacting with AI services. For example, when you use ExpressAI, your inputs and outputs are processed inside TEEs. This means your data is isolated from the system and infrastructure, is inaccessible to ExpressVPN or the model providers, and is not used to train or improve the AI models, keeping your interactions private by design.
Beyond this, other AI providers may also use confidential computing to train models on sensitive datasets from their own sources without exposing the raw data. TEEs can ensure that even while processing, the data remains protected and isolated.
Healthcare
Hospitals, research institutions, and pharmaceutical companies often work with highly sensitive patient data. Confidential computing can allow them to share and analyze this data securely without exposing raw patient information. By using TEEs, organizations can aggregate data from multiple sources to improve diagnostics, research, and drug development while protecting patient privacy.
For example, a pharmaceutical company could use confidential computing to analyze clinical trial data from multiple hospitals while maintaining compliance with privacy regulations. Hospitals and clinics can also use the technology to coordinate care across institutions, giving physicians access to broader datasets that support better patient outcomes.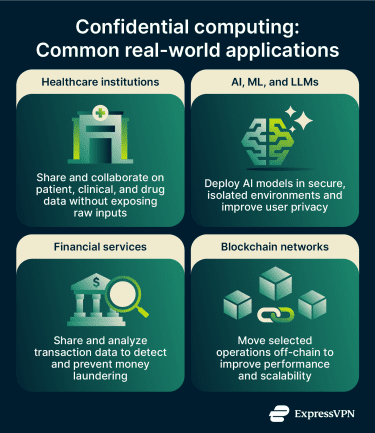
Financial services
Financial institutions, such as banks, reinsurers, and fintech firms, often face challenges detecting fraud because they’re often limited to single datasets, which may not be enough to spot suspicious transactions. Sharing financial data could improve detection, but it introduces significant risks, including breaches, regulatory noncompliance, and reputational damage.
Confidential computing helps address this by enabling institutions to securely share and analyze sensitive data without exposing it. It allows organizations to run fraud detection workloads in the cloud while keeping customer data protected. The technology can also support other sensitive processes, such as credit scoring and know your customer (KYC) checks.
Blockchain networks
A blockchain is a decentralized network of nodes operated by validators that work together to reach consensus. Nodes typically maintain copies of transaction histories, which helps ensure integrity and availability across the network. While this model promotes transparency, it can also introduce privacy, performance, and scalability challenges.
Confidential computing helps address these issues by enabling certain operations to run off-chain in secure environments. This can improve scalability while keeping sensitive data protected. It can also be used to process encrypted transaction data in a way that limits visibility to validators, helping reduce risks such as Maximal Extractable Value (MEV) attacks, which can lead to worse price execution and higher fees for users.
Key benefits of confidential computing
By securing sensitive data with hardware-level protections, confidential computing benefits both organizations and end users.
Benefits for users
Confidential computing helps keep your sensitive data protected. This can reduce the risk of personal information being exposed or misused, which in turn helps lower the likelihood of identity theft, fraud, or other forms of unauthorized access.
For everyday services, this means stronger privacy with applications that handle your data. For example, some virtual private networks (VPNs) use secure enclaves to process sensitive assignments without exposing them to the host system. With ExpressVPN’s zero-knowledge dedicated IP service, the system that assigns your dedicated IP address is designed so that even ExpressVPN doesn’t know which specific IP is assigned to you.
By keeping data protected at the hardware level, confidential computing keeps your information secure even while it’s being processed. When you use services built with this technology (like ExpressVPN’s dedicated IP address or ExpressAI), you can do so with confidence that your data remains private
Benefits for organizations
Common advantages of confidential computing for corporations, institutions, or other organizations include:
- Improved cloud and hybrid security: In cloud and hybrid environments, multiple organizations often share the same physical infrastructure. Confidential computing ensures that sensitive data is processed in an isolated environment, meaning other services or tenants running on the same hardware have no access to it.
- Intellectual property protection: Proprietary AI models, algorithms, and business logic can be shared with partners for joint analysis without either side ever seeing the other's underlying code or data.
- Stronger edge data security: Data processed at the edge, such as on Internet of Things (IoT) devices or in cloud systems located in less controlled physical environments, is more vulnerable to unauthorized access. Confidential computing can protect these workloads at the hardware level, regardless of how secure or insecure the surrounding environment is.
- Simplified regulatory compliance: Regulations like the General Data Protection Regulation (GDPR) or Health Insurance Portability and Accountability Act (HIPAA) require organizations to demonstrate that sensitive data is protected during processing. Hardware-level isolation and cryptographic attestation are tools that can assist with compliance, providing evidence that goes beyond policy documents alone.
- Secure collaboration: Multiple parties can analyze shared datasets without any party seeing the other's raw data, making previously impossible collaborations across competitors, research institutions, or regulated industries technically and legally feasible.
- Insider threat mitigation: Even privileged users such as system administrators or cloud provider staff cannot access data during processing. A compromised account gains nothing in terms of data for the attacker.
Potential challenges for organizations
While confidential computing offers strong privacy and security benefits, implementing it can sometimes introduce challenges, such as:
- Limited visibility: While isolation protects sensitive data, it can make it more difficult for IT teams to monitor system behavior and troubleshoot issues.
- Performance overhead: TEEs use extra processing and memory protections, which can slightly slow down applications.
- Complexity: Confidential computing may require applications to be adapted or redesigned to run efficiently inside a TEE. Setting up attestation (the process that verifies the enclave is genuine) can also be challenging, and hybrid environments with multiple cloud platforms may need extra configuration.
- Vendor lock-in: Some confidential computing solutions are vendor-specific due to the lack of widely adopted standards. This can make it more difficult to migrate workloads between cloud providers.
- Side-channel attacks: Some TEE implementations may be vulnerable to very advanced side-channel attacks that attempt to extract secrets from the isolated environment. That said, such attacks are typically difficult to pull off since they require physical access and are actively mitigated through hardware and software improvements.
Best practices for decision-makers
Organizations looking to implement confidential computing can address potential challenges by following certain best practices.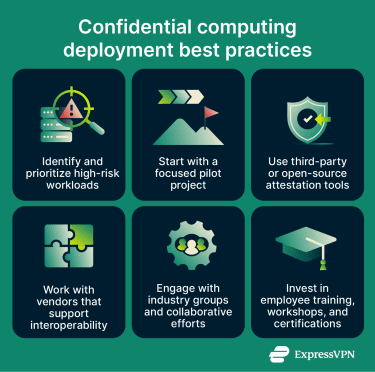
- Prioritize sensitive workloads: Identify high-risk workloads, such as AI model training, multiparty analytics, or personally identifiable information (PII) processing, and assess where data may be exposed during computation.
- Start with pilot projects: Instead of large-scale deployments, begin with a focused pilot for a specific use case. This helps demonstrate value, build internal expertise, and generate stakeholder buy-in.
- Use public or third-party attestation tools: Implementing attestation can be complex. Using established third-party or open-source solutions from legitimate entities, such as the Confidential Computing Consortium (CCC), can simplify deployment and improve reliability.
- Prioritize vendors that support interoperability: Work with providers that support open, interoperable standards for TEEs and attestation. This makes it easier to integrate across platforms and reduces vendor lock-in.
- Join collaborative efforts: Engage with industry groups, such as the CCC, collaborate with key stakeholders, and engage with relevant cloud providers and hardware vendors to stay aligned with evolving standards and best practices.
- Invest in employee training: Address skill gaps through training programs, workshops, and certifications to build internal expertise in confidential computing and secure deployment models.
Industry adoption
Recent research commissioned by the CCC shows a noticeable increase in confidential computing adoption, signaling a shift from niche to mainstream. The study surveyed over 600 IT leaders across 15 industries and found that 75% of organizations are adopting confidential computing. Of those, 57% are piloting the technology, while 18% have already moved into production.
The report also highlights regulatory pressure as a key driver. Around 77% of organizations cite the EU’s Digital Operational Resilience Act (DORA) as a major reason for considering confidential computing. DORA encourages stronger data‑in‑use protections, and confidential computing is one tool that can help meet those expectations.
Surveyed leaders also point to workload security, external threats, PII protection, and AI model training as key adoption drivers. Organizations expect benefits such as improved data integrity, stronger confidentiality guarantees, and better regulatory compliance.
Overall, confidential computing is shifting from a niche capability to a mainstream security approach. While adoption is still maturing, increasing regulatory demands and the need to secure data in use are driving broader implementation across industries.
FAQ: Common questions about confidential computing
What is the meaning of confidential computing?
What is the difference between TEE and confidential computing?
What are the advantages of confidential computing?
What are the principles of confidential computing?
Where is confidential computing used?
How is confidential computing different from cloud computing?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN