What is a cybersecurity risk assessment and how does it work?

Security decisions are only as good as an organization's understanding of its own environment. When that understanding is incomplete, teams can struggle to see where real risk exists or how serious it might be.
To address this, organizations use cybersecurity risk assessments. This article explains what a risk assessment is, what it evaluates, how the process works, and how teams use the results to guide security decisions.
What is a cybersecurity risk assessment?
A cybersecurity risk assessment is a structured process for understanding an organization's digital environment and where it's exposed to risk. It examines the systems and data the organization relies on, the threats and weaknesses that could affect them, and the potential impact of a security incident.
By providing context for security vulnerabilities, risk assessments help cybersecurity teams to evaluate and prioritize which risks need to be dealt with first.
What does a cybersecurity risk assessment evaluate?
A risk assessment looks at a few key areas to build a realistic picture of your security posture.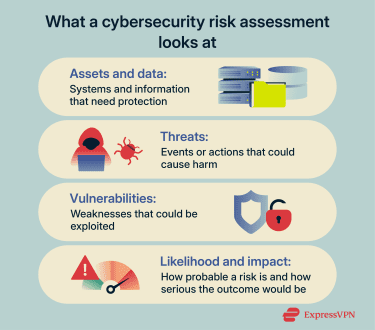
Assets and data
This includes systems like servers, employee devices, cloud services, applications, and databases. It also considers the type of data involved, especially information that would cause harm if exposed, lost, or unavailable.
Threats
Threats are anything that could cause damage. This can include external attacks like phishing or software exploitation, misuse of access by insiders, accidental mistakes, system failures, or events like power outages and natural disasters.
Vulnerabilities
Vulnerabilities are weaknesses that threats can exploit. Common examples include unpatched software, overly permissive cloud storage, weak authentication practices, and accounts with more access than necessary.
Likelihood and impact
For each risk, the assessment looks at how exposed the system is and what would happen if it were affected. Impact can include downtime, financial loss, regulatory penalties, and longer-term effects like loss of customer trust.
How to perform a cybersecurity risk assessment
A cybersecurity risk assessment typically follows a structured sequence designed to help organizations understand where they're exposed and make informed decisions about how to respond.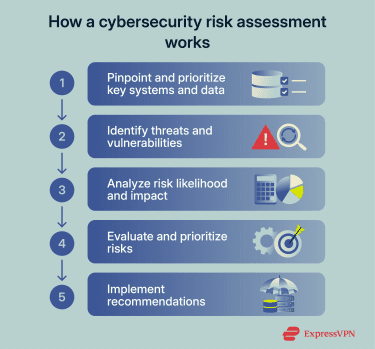
Step 1: Identify and prioritize assets
Begin by listing the systems, services, and data your organization relies on to operate, a process known as asset and architecture discovery. This includes identifying devices used by employees, servers that run applications, cloud services that store data, and any third parties that handle information on your behalf.
In practice, this information is often spread across teams. Cloud tools may be set up outside central IT, software subscriptions may be owned by individual departments, and older systems may still be running without clear ownership. Part of this step is uncovering those blind spots so they’re not overlooked during the assessment.
For each asset, consider two factors: the sensitivity of the data it handles and how important it is to business operations. A system that processes customer payments or stores personal data carries a different risk than an internal tool with limited use. Making this distinction early can help narrow the focus for the rest of the assessment.
Step 2: Identify threats and weaknesses
Once key systems and assets are identified, the next step is to look at what could realistically put them at risk. Threats and vulnerabilities can arise from the way assets are accessed, configured, and used.
Threats include external attacks such as phishing and other social engineering attempts, denial-of-service (DoS) attacks, exploitation of software vulnerabilities, credential theft, and ransomware. Internal sources of risk can include misuse of access and system failures caused by outages or faulty updates.
Vulnerabilities are the conditions that allow these threats to succeed. Technical vulnerabilities include unpatched software, exposed services, or weak authentication. Operational vulnerabilities can include shared accounts, overly broad access permissions, or limited security training.
Risk assessments use a number of methods to identify issues, depending on an organization’s infrastructure and the goals of the assessment. Security teams might run vulnerability scans (automated checks that look for known software flaws and unsafe configurations), reviews of system settings and access permissions, and checks to confirm that existing security controls are working as intended.
External sources such as government advisories and public threat databases, like the MITRE ATT&CK® knowledge base, can help identify which attack methods are most relevant to the organization’s industry and environment.
Step 3: Estimate likelihood and impact
For each identified risk, estimate how likely it is to occur and what the consequences would be if it did.
To assess likelihood, consider how exposed the affected system is, how easy the weakness would be to exploit, and whether similar attacks have been observed in your industry.
To assess impact, consider the full range of consequences a successful incident could produce. Outcomes can include service disruption, data exposure, financial loss, regulatory penalties, legal liability, and longer-term effects such as loss of customer trust. Not all consequences are immediate, so factor in recovery costs and reputational effects as well.
Some organizations use simple qualitative scales (such as low, medium, and high) to rate these factors. Others apply numerical scoring when more precision is needed, particularly for high-value systems or when presenting findings to leadership. Either approach works as long as it's applied consistently across the assessment.
Step 4: Prioritize risks
With likelihood and impact estimates in place, compare and rank the identified risks. A risk matrix can help visualize where each risk falls relative to others and make the ranking easier to communicate.
A lower-likelihood issue affecting a critical system may deserve attention before a higher-likelihood issue tied to a less important asset. Look for patterns as well, such as multiple risks affecting the same system or stemming from the same underlying weakness. Clusters like these often signal a broader problem worth addressing.
Step 5: Decide how to address each risk
For each prioritized risk, decide on an appropriate response. The response should match the level of risk and the organization’s tolerance, rather than defaulting to a single approach.
Some risks are reduced by making changes to systems or processes, such as fixing configuration issues, limiting access, or improving monitoring and security practices. Other risks may be transferred, for example, through contractual arrangements or insurance, when direct mitigation is not practical.
In some cases, a risk may be accepted. This is appropriate when its likelihood and impact are understood and fall within agreed limits. Acceptance should be a conscious decision, not the result of inaction.
Not every risk requires immediate action, but every risk should have a recorded decision. Documenting how and why a risk is being handled makes it easier to communicate decisions to stakeholders. It also ensures a record is kept that can be reviewed later as systems, threats, or business priorities change.
Related: What a hacker can teach you about keeping your systems safe
Cybersecurity risk assessment frameworks and tools
Frameworks and tools support risk assessments in different ways. Frameworks describe how an assessment should be carried out. Tools assist with collecting information and tracking decisions. Both standardize how information is gathered and analyzed, which helps security teams make objective and justifiable decisions.
NIST SP 800-30 risk assessment framework
The National Institute for Standards and Technology’s (NIST) SP 800-30 is a widely used guide for conducting cybersecurity risk assessments. It was developed for U.S. government systems, but many private organizations use it because it’s well-documented and lays out the process clearly.
The framework describes risk assessment as an ongoing cycle rather than a one-time task. At a high level, it focuses on four activities:
- Preparation: Defining the scope of the assessment and what systems are being reviewed.
- Assessment: Identifying threats, weaknesses, and possible consequences.
- Communication: Documenting findings and sharing them with decision-makers.
- Maintenance: Revisiting the assessment as systems, threats, or business needs change.
NIST SP 800-30 also groups threats by source, such as deliberate attacks, accidents, system failures, or environmental events. It provides guidance on estimating likelihood and impact, often using simple scales rather than precise numbers.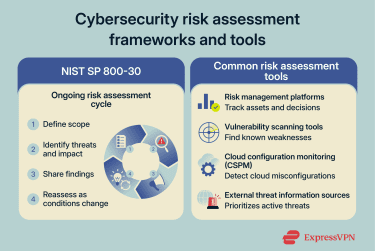
Common tools used for risk assessment
Risk management platforms
Risk management platforms are systems used to document, track, and manage assessments across an organization. They help teams record assets, threats, ownership, and decisions in a consistent way, across various tools and departments.
These platforms are often part of broader governance, risk, and compliance programs, which focus on documenting how an organization manages risk across different areas. They’re most useful for organizations that run assessments regularly or need clear records for internal reviews and audits.
Vulnerability scanning tools
Vulnerability scanning tools identify known weaknesses in systems and applications, such as missing updates, unsafe configurations, or common software flaws. They provide technical input for a risk assessment by highlighting where systems are exposed.
Scan results need to be reviewed in context. Not every finding represents meaningful risk, and the same issue can carry different weight depending on where it appears and what the system supports.
Cloud configuration monitoring tools
In cloud environments, security settings are often spread across many individual services, each with its own permissions and defaults.
Cloud configuration monitoring tools, also known as cloud security posture management tools (CSPM), review these settings to identify misconfigurations that increase exposure. Vulnerabilities in cloud software can include resources that are publicly accessible, weak access controls, or encryption issues.
External threat information sources
Some teams use shared information about real-world attacks to understand how security issues are being exploited outside their organization. This can include public incident reports, threat advisories from government agencies, industry information-sharing groups, and summaries of observed attack activity.
This information helps to determine which weaknesses are actively being targeted in practice, rather than treating all potential threats as equally likely.
Cybersecurity risk assessment best practices
The practices below focus on keeping assessments accurate, usable, and aligned with how the organization actually operates.
Conducting regular risk reviews
Risk assessments work best when they follow a predictable review rhythm. Instead of reassessing everything at once, teams often revisit high-impact systems more frequently and lower-impact areas less often.
Certain changes should prompt a review outside the normal schedule. These include launching new systems, moving data into new environments, business model changes, mergers, acquisitions, or making significant changes to how existing systems are used. Reviews tied to clear triggers make sure that assessments are aligned with reality rather than relying on fixed calendars alone.
Involving stakeholders and business owners
Risk assessments are more reliable when they include input from people who work with the systems every day.
- Business owners can identify which assets are most important and what actually happens if those assets are compromised or made unavailable.
- Technical teams can describe how systems are built and connected, including details that aren’t always written down or centrally tracked.
- Legal and compliance teams can explain which systems or data types carry regulatory exposure.
Bringing these views together reduces blind spots that wouldn’t be obvious from a single team’s perspective.
Documenting and communicating risk findings
Documentation ensures that action and accountability can be tracked over time. Assessment logs should state what risks were found, what assets they affect, and what decision was taken. They should also be up to date, clear, and organized in a way that’s accessible to the relevant stakeholders.
That said, different groups in an organization may need different levels of detail. Technical teams usually need information relevant to understanding a risk and addressing it. On the other hand, business leaders might only need a clear explanation of potential impact without technical depth.
Related: Cybersecurity tips for small businesses
Common challenges in cybersecurity risk assessments
Even when an assessment is carried out carefully, certain factors can limit its accuracy, both during the process and over time.
Common issues include:
- Incomplete visibility during discovery: Not all systems are easy to identify. Documentation may be outdated, environments may be complex, and relevant information may be held by specific teams or individuals who aren't directly involved in the assessment.
- Environmental change between assessments: New services get introduced, older systems stay in use longer than expected, access permissions shift, and data moves between environments. Assessment records don't always keep pace.
- Limited visibility into third-party services: External providers may handle sensitive data or support critical functions, but offer little transparency into their own security controls or infrastructure.
When these factors aren't fully accounted for, parts of the environment may carry risk that the assessment may not fully reflect.
Related: Biggest cyber attacks in history
FAQ: Common questions about cybersecurity risk assessment
What is the basic cybersecurity risk assessment?
A basic cybersecurity risk assessment is a structured way to understand which security issues could realistically affect an organization and how serious the consequences would be. It looks at systems and data, what could go wrong, and the potential impact. The goal is to identify which risks deserve attention first.
What are the main steps of a cybersecurity risk assessment?
The process usually starts by identifying key systems and data, then identifying threats and weaknesses that could affect them. Next, teams estimate the likelihood and impact to prioritize risks. Finally, they decide how to address the highest-priority issues and document those decisions.
What is the NIST 800-30 risk assessment?
NIST SP 800-30 is a guideline published by the National Institute of Standards and Technology (NIST) for conducting cybersecurity risk assessments. It outlines how to identify threats, weaknesses, likelihood, and impact in a consistent way. Many organizations use it as a reference, even outside government environments.
How can organizations prepare for a risk assessment?
Preparation usually involves identifying key systems, confirming who owns them, and gathering basic information about how they’re used. Teams often review existing documentation and access controls ahead of time. Clear scope and participation make the assessment easier to run and interpret.
What common mistakes should be avoided during risk assessments?
One common mistake is treating the assessment as a one-time exercise rather than something that needs regular updates. Another is focusing only on technical issues while ignoring business impact or operational use. Poor documentation can also reduce the usefulness of results over time.
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN