Expressvpn Glossary
IPsec
What is IPsec?
Internet Protocol Security (IPsec) is a suite of protocols that secures data transmitted across IP networks through encryption and authentication. It maintains data confidentiality, integrity, and authenticity during transmission between devices, networks, or servers.
Operating at the network layer (Layer 3) of the Open Systems Interconnection (OSI) model, IPsec protects data packets independently of the applications or services that generate them.
How does IPsec work?
IPsec relies on two main protocols for packet protection:
- Authentication Header (AH): Provides packet authentication and integrity, verifying the packet’s source and ensuring it hasn’t been altered.
- Encapsulating Security Payload (ESP): Encrypts the payload (the data inside the packet) for confidentiality and can also authenticate the packet if configured to do so.
Before communication begins, participating devices or gateways negotiate encryption and authentication parameters using the Internet Key Exchange (IKE) protocol. Once verified with digital certificates or pre-shared keys, they establish a trusted link called a Security Association (SA).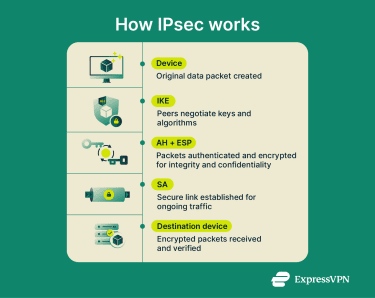
IPsec can operate in two modes:
- Transport mode: Encrypts only the packet’s payload while leaving the header visible. Commonly used for direct device-to-device communication.
- Tunnel mode: Encrypts the entire original packet, including the header, and encapsulates it within a new one. This mode is used for network-to-network communication, such as site-to-site or remote-access virtual private networks (VPNs).
Each packet is encrypted, labeled with headers and trailers, transmitted, and then decrypted and verified at the destination according to the agreed parameters.
Why is IPsec important?
IPsec is one of the most widely adopted standards for securing IP communications. Because it operates at the network layer, IPsec can secure nearly all forms of IP-based communication. It provides three key protections:
- Confidentiality: Prevents unauthorized parties from reading transmitted data.
- Integrity: Ensures that data is not altered during transmission.
- Authentication: Confirms the identity of the communicating devices or gateways.
Where is IPsec used?
IPsec is implemented in various network security scenarios, including:
- VPNs: Encrypts data through secure tunnels between users and servers.
- Site-to-site connections: Links remote offices securely over the internet.
- Remote employee access: Enables secure connections to internal systems through IPsec-based VPN gateways.
- Voice over Internet Protocol (VoIP) and video conferencing: Protects signaling and media data from interception.
- Government and enterprise data transfers: Safeguards sensitive information exchanged between agencies or data centers.
Benefits and limitations
IPsec delivers strong, network-layer protection for data. Here are its key advantages:
- Provides strong encryption and authentication at the IP layer.
- Interoperable across platforms due to open standards.
- Suitable for diverse configurations, including end-to-end and network-to-network protection.
- Proven reliability in enterprise, government, and telecommunications environments.
But it also involves some trade-offs in how it’s deployed and maintained:
- Configuration can be complex, especially in mixed-network environments.
- Encryption and authentication introduce processing overhead that may reduce performance on lower-capacity devices.
- Successful operation requires compatible IPsec versions, cryptographic suites, and parameters at both endpoints.
Further reading
FAQ
What is the difference between IPsec and SSL VPN?
Internet Protocol Security (IPsec) operates at the network layer (Layer 3) of the Open Systems Interconnection (OSI) model and protects all IP traffic between devices or networks. Secure Sockets Layer (SSL) VPNs, on the other hand, rely on the Transport Layer Security (TLS) protocol and operate at the transport (Layer 4) and application (Layer 7) layers. They usually secure traffic for specific applications (most often web-based services) and can often be accessed through a standard web browser without installing special software.
IPsec is better for site-to-site or full network access, while SSL VPNs are more suited to controlled, browser-based remote access.
Is IPsec still secure today?
Yes. When configured with current encryption and integrity algorithms, such as Advanced Encryption Standard with Galois/Counter Mode (AES-GCM) and Secure Hash Algorithm 2 (SHA-2), and managed with proper keys and updates, Internet Protocol Security (IPsec) remains secure by modern standards.
What are the main components of IPsec?
Internet Protocol Security (IPsec) includes the Authentication Header (AH) for data integrity and source authentication, the Encapsulating Security Payload (ESP) for encryption and optional authentication, and the Internet Key Exchange (IKE) protocol for negotiating keys and Security Association (SA).


