Expressvpn Glossary
Account takeover
What is an account takeover?
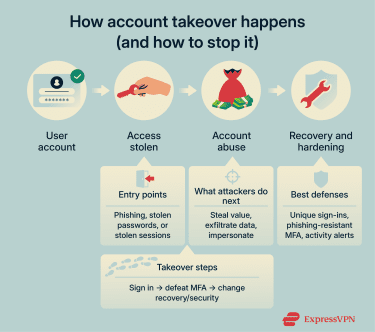
An account takeover is a type of cyberattack where an intruder gains unauthorized access to an online account. This is often achieved by stealing valid login details and signing in as the account holder.
After gaining access, cybercriminals can typically bypass standard security checks because the login appears legitimate. They might take control of the account, change its security or recovery settings, and use it for fraud, data theft, or extortion.
How does an account takeover happen?
Account takeovers often start with attackers getting login information through one of the following ways:
- Stealing credentials: Phishing, malware, or leaked credentials from data breaches and underground markets can expose usernames and passwords that are then reused across services.
- Credential stuffing or brute force: Automated tools attempt large numbers of logins, either with known username/password pairs (credential stuffing) or by guessing passwords, until one works.
- Session hijacking: An attacker steals an existing authenticated session from a browser or device to access an account without reentering the password.
- Bypassing multi-factor authentication (MFA): Attackers may use MFA bombing (sending repeated approval requests until the user accepts one out of frustration), SIM swapping (transferring the victim's phone number to gain access to SMS codes), or social engineering to trick users into approving login attempts or sharing verification codes.
Common account takeover targets
Attackers often focus on accounts that provide financial value or access to sensitive data, or a way to unlock other accounts. These can include:
- Banking and payment apps: These accounts can be used to transfer money, make unauthorized purchases, or commit financial fraud.
- Email and cloud storage accounts: Access to email or stored files can expose sensitive data, enable password resets for other services, or facilitate identity theft.
- Social media and messaging platforms: Compromised profiles can be used to impersonate account owners, send scams, spread malicious links, or damage reputations.
- E-commerce and loyalty programs: These accounts may store saved payment details, addresses, or reward points that attackers can exploit.
- Work accounts: Business accounts can provide access to internal systems, company data, and connected services through single sign-on (SSO) or Software-as-a-Service (SaaS) platforms.
Why is account takeover a threat?
Account takeovers can have long-lasting consequences for both individuals and organizations, including:
- Financial loss: Attackers can transfer funds, make unauthorized purchases, or drain stored balances and reward points.
- Identity risks and privacy exposure: Compromised accounts can expose private data, messages, and documents that attackers may use for fraud, impersonation, or additional attacks.
- Loss of access to critical services: Victims may be locked out of essential accounts such as email or banking if attackers change recovery details or security settings, making password resets and account recovery more difficult.
- Reputation damage: If attackers use compromised accounts to spread scams or malicious content, it can harm personal or professional relationships and trust.
- Lateral movement: Attackers leverage compromised accounts and credentials to access connected services, reset other accounts, or move deeper into a corporate environment.
- Regulatory and compliance risk: When an account takeovers result in personal data exposure, organizations may face reporting obligations, enforcement actions, or penalties under applicable privacy laws such as the California Consumer Privacy Act (CCPA) or the General Data Protection Regulation (GDPR).
Further reading
- What to do if you’ve been hacked on social media
- Spam vs. phishing: Key differences and how to stay safe online
- What to do if your Discord account is hacked
- How to recover a hacked Google account
- How to recover a hacked WhatsApp account


