Expressvpn Glossary
Access control system
What is an access control system?
An access control system is a security mechanism that regulates who or what can view or use physical and digital resources. It’s designed to reduce risk by combining identity checks with permission controls.
The main purpose of this system is to ensure that users are who they claim to be and have the appropriate permissions to access specific data. It limits access to campuses, buildings, rooms, and physical assets, as well as computer networks, system files, and data.
How does an access control system work?
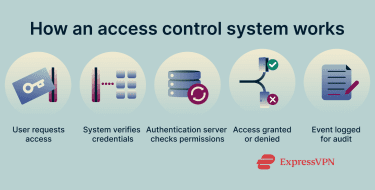
The system relies on a sequence of steps to manage identities and protect resources:
- Authentication: The system confirms a user’s identity. This is often done using a password, biometric scan, multi-factor authentication (MFA), or a security token.
- Authorization: Once identity is verified, the system determines which resources the user is allowed to access. Authentication and authorization work together to secure the entry point.
- Access: The system grants or denies entry to the resource based on the authorization step.
- Monitoring: The system logs user activity to track behavior and identify potential anomalies.
- Audit: Administrators review these logs for compliance and security analysis.
Types of access control systems
There are several types of access control system models, each offering a different level of granularity:
- Discretionary access control (DAC): Resource owners decide who can access their data. They grant permissions, often using an access control list (ACL).
- Mandatory access control (MAC): Access depends on strict security labels or classifications set by a central authority. Users can’t change these permissions.
- Role-based access control (RBAC): Permissions are tied to a user’s specific role within an organization. This model is common in business environments.
- Attribute-based access control (ABAC): The system evaluates specific attributes, the environment, and context (such as time of day or location) to decide access.
Why are access control systems important?
Access control systems help organizations:
- Protect sensitive information and important infrastructure from theft or damage.
- Prevent unauthorized access and limit insider threats.
- Comply with standards like International Organization for Standardization (ISO) 27001 and the EU’s General Data Protection Regulation (GDPR).
- Support secure integration with virtual private networks (VPNs), firewalls, and identity management tools.
Physical vs. logical access control
Security strategies often divide into physical vs. logical access control.
- Physical access control: Restricts access to physical spaces, such as buildings, server rooms, elevators, and campuses. Common methods include keycards, PINs, and biometrics.
- Logical access control: Protects digital systems, networks, and data. It controls entry via credentials, encryption, and authentication software.
Further reading
- TrustedServer: Deep dive into the security of our server tech
- Zero-trust network access (ZTNA) explained
- What are network protocols? A complete guide


