Expressvpn Glossary
Three-way handshake
What is a three-way handshake?
A three-way handshake is a process that establishes a Transmission Control Protocol (TCP) connection between two hosts (a client and a server). It ensures that they’re both reachable and ready to exchange data.
How does a three-way handshake work?
A TCP three-way handshake uses three steps to establish a connection between two hosts, such as a computer and a website. This process sets up the parameters needed for reliable, ordered byte-stream transfer between the two systems. Simplified, the process looks like this:
- The client initiates the connection request.
- The server acknowledges the request and responds.
- The client confirms the response.
This exchange happens through data packets that contain specific sequence numbers:
- Client sends a synchronize packet (SYN) to the server with a random number, such as 50.
- Server responds with a synchronize-acknowledge packet (SYN-ACK) containing its own random SYN number (such as 60) and the active client’s SYN plus one (51).
- Client replies with an acknowledge packet (ACK) containing the latter’s SYN plus one (61).
Once the SYN, SYN-ACK, and ACK packets are successfully exchanged and received by both the client and the server, the TCP connection is established.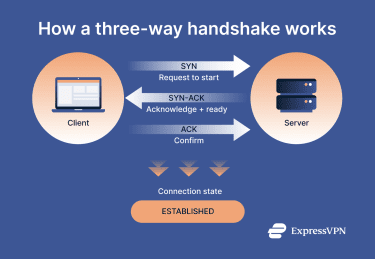
Why is the three-way handshake important?
The TCP three-way handshake is what allows two devices on a network to establish a reliable, two-way connection before any real data is exchanged. By confirming that both sides are reachable and ready to communicate, it prevents confusion caused by half-open or stale connections and sets up the sequencing needed for reliable, ordered data delivery. This process also lays the groundwork for TCP’s flow and congestion control, helping manage how much data is sent at once to avoid overwhelming either side.
The handshake establishes a stable and predictable connection and therefore underpins many everyday internet activities. It’s used whenever your device opens a TCP connection, such as when loading websites over HTTP or HTTPS, sending and receiving email, logging into another computer via Secure Shell (SSH), or connecting to services like virtual private networks (VPNs) that rely on TCP.
In practice, most online interactions that require dependable, two-way communication depend on the three-way handshake working in the background.
Risks and privacy concerns
Given that the three-way handshake is the foundation of most internet connections, attackers often target it to try to disrupt communication between services. While this isn’t typically risky for general users, it may impact service availability, privacy, and performance. Some concerns include:
- Servers can be overwhelmed: Attackers can initialize a SYN flood, sending repeated connection requests (often spoofed) and ignoring the server’s SYN-ACK replies. This can lead to slowdowns or crashes as the server keeps track of all unfinished requests.
- Misconfigurations weaken network resilience: Poorly configured systems may handle failed or incomplete connections improperly, making the network easier to disrupt.
- Basic connection details are exposed: The handshake process reveals basic network-level information like the IP addresses of the communicating systems, but the contents of the session are encrypted and protected.
- Network devices can disrupt connections: Network devices between two endpoints (like firewalls) can interfere with handshake signals, sometimes disrupting connections. This is called a middlebox interference.
Further reading
- What are network protocols? A complete guide
- How does the internet work?
- DoS vs. DDoS attacks: Key differences and how to protect yourself
- TCP vs. UDP: Understanding the key differences and best use cases


