Triangulation fraud: How it works and how to prevent it
 You order something online, it arrives exactly as promised, and everything seems fine. However, unbeknownst to you, a fraudster has used stolen credit card details to purchase the item, making you an unwitting participant in a larger scam that also affects the cardholder and the retailer.
This is how triangulation fraud, a type of scam where a criminal secretly uses stolen payment information to fulfill a real customer’s order, typically works. While the customer may remain unaware of the fraud, the retailer and the legitimate cardholder often bear the consequences, including chargebacks and disputed payments.
This guide explains what triangulation fraud is, how it works, and how to recognize the warning signs. It also outlines practical steps for both consumers and e-commerce merchants to reduce the risk of falling victim to this type of fraud.
You order something online, it arrives exactly as promised, and everything seems fine. However, unbeknownst to you, a fraudster has used stolen credit card details to purchase the item, making you an unwitting participant in a larger scam that also affects the cardholder and the retailer.
This is how triangulation fraud, a type of scam where a criminal secretly uses stolen payment information to fulfill a real customer’s order, typically works. While the customer may remain unaware of the fraud, the retailer and the legitimate cardholder often bear the consequences, including chargebacks and disputed payments.
This guide explains what triangulation fraud is, how it works, and how to recognize the warning signs. It also outlines practical steps for both consumers and e-commerce merchants to reduce the risk of falling victim to this type of fraud.
What is triangulation fraud?
Triangulation fraud is a type of e-commerce scam where a criminal secretly acts as a middleman between a legitimate retailer and an unsuspecting shopper. The criminal sets up a fake online store and collects payments from real customers. They then use stolen credit card details (often obtained through data theft or breaches, phishing attacks, carding forums, or credit card skimming) to purchase the ordered products from a legitimate retailer, who ships them directly to the original buyer. The scam typically involves three parties, hence the term triangulation fraud:- The criminal: The person running the scam. They create a misleading online store or marketplace listing and list products, often at noticeably lower prices than retail. However, they typically don’t hold any inventory. Instead, they rely entirely on stolen payment details to fulfill orders through legitimate retailers.
- The shopper: An ordinary customer who believes they’re buying from a legitimate store. The shopper makes the payment and provides shipping information when placing the order, without realizing that the seller is fraudulent.
- The legitimate retailer: The real online store that fulfills the order. They receive the order from the criminal (made using stolen payment details) and ship the product directly to the shopper, only to later face a chargeback when the real owner of the stolen card disputes the transaction. The merchant then loses both the money and the product, often with no recourse to recover either.
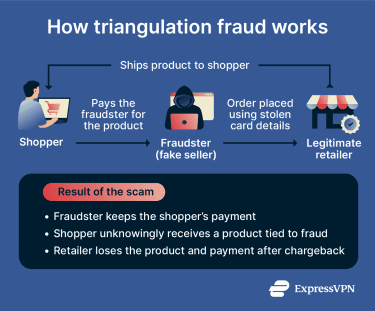 This setup allows the threat actor to profit while the retailer and the real cardholder deal with the consequences of the unauthorized transaction. The customer can also be affected since they enter their payment details on a fraudulent site controlled by the scammer. This means their payment information could potentially be stored, reused, or sold, putting them at risk of future unauthorized charges or other scams.
You might wonder why the criminal goes to the effort of placing the order at all, rather than simply taking the buyer’s money and disappearing. The reason is that having the product delivered makes the transaction appear legitimate to the buyer, so they have little reason to report the seller. This delay can allow the criminal to keep operating the fake store for longer and collect payments from additional customers while using stolen cards to fund the purchases.
This setup allows the threat actor to profit while the retailer and the real cardholder deal with the consequences of the unauthorized transaction. The customer can also be affected since they enter their payment details on a fraudulent site controlled by the scammer. This means their payment information could potentially be stored, reused, or sold, putting them at risk of future unauthorized charges or other scams.
You might wonder why the criminal goes to the effort of placing the order at all, rather than simply taking the buyer’s money and disappearing. The reason is that having the product delivered makes the transaction appear legitimate to the buyer, so they have little reason to report the seller. This delay can allow the criminal to keep operating the fake store for longer and collect payments from additional customers while using stolen cards to fund the purchases.
Real-world example of triangulation fraud
In 2024, police in Montgomery County, Maryland, uncovered a triangulation fraud scheme after a victim reported that their bank card had been used without authorization to buy an item from Dick’s Sporting Goods. Detectives tracked the shipment and discovered that the package had been delivered to a different person who had legitimately purchased the same item from a Poshmark seller. Investigators determined that the Poshmark seller had used stolen credit card information to purchase the item from the retailer and had it shipped directly to the buyer while keeping the payment made on Poshmark. In another triangulation fraud scheme, a Carmel, Indiana resident ran a years-long operation where he and his co-conspirators created fraudulent eBay seller accounts and linked them to fraudulent PayPal accounts. He then listed popular items like PlayStations, handbags, and toys, often at below-market prices to attract buyers. When a customer placed an order, he purchased the item from legitimate online retailers using stolen credit card details and had it shipped directly to the buyer. This allowed him to keep the payment from the marketplace sale, while the retailer ultimately absorbed the loss when the real cardholder later reported the fraudulent charge.How to detect triangulation fraud
Triangulation fraud can be difficult to identify because the transaction often appears legitimate. That said, certain warning signs can help both shoppers and merchants recognize potential triangulation fraud earlier.Warning signs for online shoppers
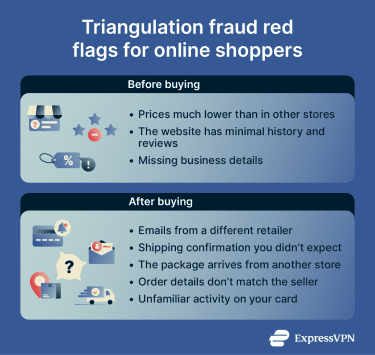
Most buyers don't realize they've been caught up in triangulation fraud until after the fact, if ever. However, there are several patterns worth watching for before and after a purchase. Common warning signs include:- Prices that seem unusually low: Fraudulent stores often advertise products at noticeably lower prices than other retailers to attract buyers quickly.
- Limited or inconsistent contact information: Some fraudulent sites or seller accounts provide little information about the business; shoppers may notice missing addresses, incomplete contact details, or generic support email addresses.
- Unfamiliar or newly created websites: Stores with very little online history, limited reviews, or recently registered domains may require extra scrutiny. On online marketplaces, seller accounts used in triangulation fraud also tend to be fairly new, with few ratings or reviews, yet often claim to carry a suspiciously large inventory of items.
- Pressure to buy quickly: Some fraudsters may pressure buyers to complete transactions quickly, preventing them from taking time to research the seller or verify the listing. Urgency tactics, such as limited-time countdowns and "only 1 left" notices across multiple listings, are often designed to short-circuit due diligence.
- Limited payment options: Some fraudsters restrict payment options to wire transfers, prepaid cards, or cryptocurrency to avoid the chargeback process that would otherwise expose them. However, triangulation fraud can also occur through standard marketplace payments.
- Unusual payment behavior: In some cases, shoppers may notice unexpected emails, order confirmations from a different retailer, or shipping notifications that don’t match the store they purchased from.
- Order arriving in unexpected packaging: If your order arrives in official branded packaging from a retailer you didn't shop with, that's a strong sign your purchase was fulfilled using stolen card details.
Red flags for e-commerce merchants
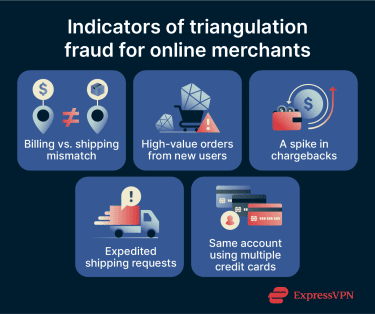
For merchants, some transaction patterns might indicate that an order could be connected to a triangulation fraud scheme. However, no single indicator is conclusive on its own.- Mismatch between billing and shipping details: While this doesn’t automatically indicate fraud, orders in which the shipping address differs significantly from the billing address may require closer review, especially when combined with other signals.
- New customer accounts with high-value purchases: Fraudsters may use newly created accounts or guest checkout to place high-value orders that can’t easily be tied to previous activity.
- Frequent chargebacks for similar transactions: Repeated disputes involving similar products, shipping locations, or order structures may signal a pattern linked to triangulation fraud.
- Multiple orders using different payment details: Repeated purchases from the same account or IP address with varying credit cards or names.
- Expedited or overnight shipping requests: Scammers may try to receive goods before the fraud is detected or the transaction is reversed.
How triangulation fraud impacts e-commerce
The effects of triangulation fraud extend well beyond the loss from a single fraudulent transaction. For merchants, what begins as an isolated chargeback can quickly escalate into a compounding set of financial, reputational, and operational problems.Financial losses and chargebacks
One of the most immediate impacts of triangulation fraud is the financial loss associated with chargebacks. When the real owner of a stolen credit card identifies an unauthorized transaction, they can dispute the payment with their bank. This typically triggers a chargeback process. The retailer that processed the transaction may be required to refund the payment, even though the product has already been shipped. For merchants, this can result in several costs:- Refunded transaction amounts: The merchant loses the payment associated with the fraudulent order.
- Chargeback fees: Payment processors may apply additional administrative fees for each disputed transaction. With multiple attacks, these fees alone can quickly add up to significant costs for merchants.
- Lost inventory and shipping costs: The retailer has already fulfilled the order and covered delivery expenses.
Reputational damage and customer trust
Triangulation fraud also creates a trust problem for merchants, even though they're the victims. Since cardholders are often unaware that the merchant is also a victim, they may be quick to assign blame to them. This can result in negative reviews, poor word-of-mouth, and lasting reputational damage that discourages future customers.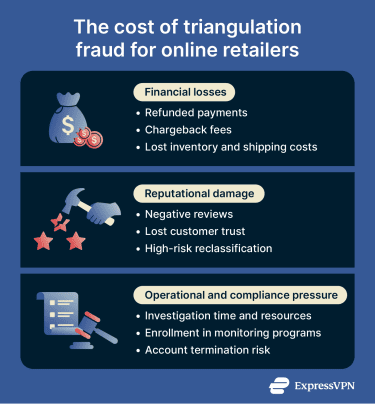
Operational and compliance risks
Triangulation fraud can also increase operational pressure for e-commerce businesses. Fraud investigations, chargeback disputes, and customer support inquiries require time and resources. Merchants might need to:- Review suspicious transactions and order histories.
- Respond to chargeback claims from banks or payment processors.
- Monitor fraud patterns across customer accounts and transactions.
How to prevent triangulation fraud
Triangulation fraud schemes rely on multiple parties and legitimate retail channels, so no single measure can eliminate the risk. However, there are practical safeguards that can reduce the likelihood of fraudulent activity going unnoticed. The following strategies can help both shoppers and businesses limit their exposure to triangulation fraud schemes.How consumers can protect themselves
Shoppers can lower their risk of encountering fraudulent storefronts or having their credit cards used in triangulation schemes by taking a few precautionary steps before making an online purchase. Helpful practices include:- Research unfamiliar stores: Only shop with trusted, reputable vendors and websites. Look for independent reviews, business contact details, seller ratings, review history, and a consistent online presence before purchasing from a new website or vendor.
- Compare prices across retailers: If a product is priced significantly lower than similar listings elsewhere, this should prompt further scrutiny.
- Review the website carefully: Check for clear return policies, customer support information, a checkout page that uses HTTPS, and other indicators of a legitimate business.
- Use payment methods with fraud protection: Credit cards and reputable payment services typically offer dispute mechanisms that can help reverse unauthorized transactions.
- Monitor payment activity: Regularly reviewing bank or card statements can help identify unfamiliar transactions early.
- Use virtual card numbers where available: Some banks and card issuers offer virtual card numbers, which are temporary, often single-use numbers linked to your real account. Using one for an online purchase doesn’t stop triangulation fraud, but it can help with follow-up scams: even if your card details are exposed or collected by a fraudulent seller, the number typically can’t be reused for additional purchases.
How merchants can reduce fraud risk
For merchants, effective prevention combines operational practices with the right technical tools. It works best when both are in place. Some common practices include:- Transaction monitoring: Automated fraud detection tools can flag orders with unusual patterns, such as high-value purchases from new accounts, orders for the same item, or mismatched device fingerprints.
- Reviewing billing and shipping discrepancies: Orders with differences between billing and shipping addresses may warrant additional verification.
- Monitoring chargeback patterns: Repeated disputes involving similar products, locations, or other order characteristics can reveal potential fraud schemes early. However, not all chargebacks result from triangulation scams. Merchants need to differentiate these patterns from friendly fraud, where legitimate cardholders dispute charges they actually authorized.
- Customer verification processes: Some merchants use additional verification steps, such as email verification or phone number validation, to confirm their customer is who they claim to be.
- Monitoring for duplicate storefronts and brand impersonation: In some cases, fraudsters create fake storefronts that imitate legitimate retailers to attract buyers. Monitoring for duplicate storefronts and brand impersonation can help identify potential fraud attempts before buyers are affected.
What to do if you’ve been affected by triangulation fraud
Whether you’re a shopper or an online retailer, there are practical steps you can take to identify the issue, protect yourself, and respond effectively.For shoppers
If you think you may have unknowingly purchased an item through a triangulation fraud scheme, take the following steps:- Stop purchasing from the seller: Avoid placing additional orders if anything about the transaction seems unusual, such as unexpected shipping details or emails from a different retailer.
- Report the seller or fraudulent store: If you purchased through a marketplace like eBay or Amazon, use the platform’s reporting tools to flag the seller. If you bought from a standalone website, report it to your browser’s safe browsing service or a fraud-reporting resource in your country. In the U.S., you can report fraud to the Federal Trade Commission (FTC). Even if you received the item you ordered, reporting suspicious activity can help stop fraudsters from targeting other buyers.
- Check your payment statements: Review your card or bank statements for unfamiliar charges. Even if the original purchase appears legitimate, fraudulent sites might store or reuse your payment details. If anything looks wrong, contact your bank or payment provider so they can investigate suspicious transactions and block further misuse of your card.
For online retailers
If you suspect that an order may be linked to a triangulation fraud scheme, the following steps can help limit the impact:- Delay or hold fulfillment if needed: If the order appears suspicious, pause shipping until additional verification is completed to avoid sending goods tied to fraudulent payments.
- Initiate a chargeback investigation: Review the transaction details, including payment method, billing address, shipping address, and order history, to determine whether the purchase shows signs of fraud.
- Document orders and communications: Preserve records of the suspicious orders, including transaction data, customer messages, IP addresses, shipping details, and any associated email communications. This documentation is valuable both for chargeback disputes and for any subsequent law enforcement inquiry.
- Strengthen verification measures: In triangulation fraud, attackers often use stolen card details that may be incomplete. Apply additional checks such as Address Verification Service (AVS) or Card Verification Value (CVV) validation to confirm that the person placing the order actually has access to the legitimate cardholder’s information.
- Report to authorities: If the fraud is significant or appears to be part of a coordinated scheme, consider filing a report with relevant authorities and payment processors. Providing detailed transaction records and documentation will support any investigation.
FAQs: Common questions about triangulation fraud
Is triangulation fraud the same as regular credit card fraud?
Does triangulation fraud only affect people who shop on unfamiliar websites?
If I paid through a major marketplace, am I automatically protected from triangulation fraud?
Can triangulation fraud happen even if a site uses HTTPS?
Nullam interdum sapien nec neque egestas auctor?
Who is usually liable when triangulation fraud leads to chargebacks?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN