Logic bomb: Definition, examples, detection, and prevention

Among the many forms of cyberattacks, logic bombs can be particularly difficult to address. Rather than immediately attacking a system, a logic bomb is embedded in software or a system and can remain dormant for weeks, months, or even years before activating. Because it may be hidden within otherwise legitimate code, it can be hard to detect before it triggers.
This article examines the types of logic bombs, explains how they work, and provides practical guidance on detecting and preventing logic bomb attacks.
What is a logic bomb?
A logic bomb is malicious code intentionally embedded in a software system, designed to execute a harmful action when specific conditions are met. The term itself reflects this two-part structure: "logic" refers to the conditional trigger, and "bomb" refers to the damage that follows once that trigger is satisfied.
Unlike a computer virus, a logic bomb doesn’t inherently self-replicate or spread to other systems. It sits within existing software and remains inactive until its predefined conditions occur. While the trigger mechanism may resemble routine conditional code, what defines a logic bomb is its deliberately destructive payload.
For instance, an employee might embed code that deletes critical company files if their user account is ever removed from the system, ensuring damage is done in the event of their termination.
Also read: Malware vs. virus: Key differences explained.
How does a logic bomb work?
A logic bomb attack generally follows three broad stages: the code is planted in a system, it waits for specific conditions to be met, and then it executes its payload. The following sections break down each stage.
How are logic bombs planted?
Logic bombs are most commonly planted by insiders (developers, system administrators, or contractors) who have legitimate access to modify software, configurations, or system components. Because these changes may be made using authorized access, they can be harder for standard security controls to distinguish from legitimate activity.
However, logic bombs can have other attack vectors. External attackers may deploy logic-bomb functionality through malware, compromised software updates, or malicious files and links delivered through phishing.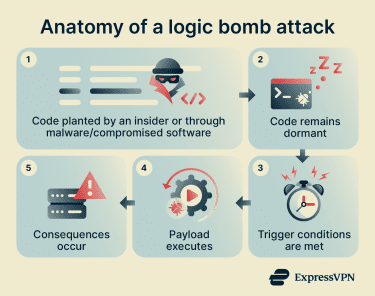
Common activation triggers
Logic bombs activate only when specific trigger conditions align. Most activation triggers fall under one of these categories:
- Time-based: The bomb activates on a specific date or after a set interval. Logic bombs that rely solely on time-based triggers are sometimes called "time bombs" or “time bomb malware.”
- Event-based: The bomb fires when a specific system event occurs, such as a user account deletion, a file access, or a process running.
- Hybrid: The bomb requires multiple conditions to be met before it executes; for example, it activates only after a certain date and only if a particular file has been opened.
Typical payloads and outcomes
The damage a logic bomb causes depends on what the attacker designed it to do. Common payloads include:
- System disruption: Shutting down or disabling applications, services, networks, or automated processes.
- Data deletion or corruption: Deleting, altering, or encrypting files so they become inaccessible or unusable.
- Unauthorized access: In some cases, installing a backdoor or otherwise enabling later access to a system.
These payloads can lead to serious downstream consequences for victims:
- Operational downtime: Business operations are interrupted, causing delays and lost productivity.
- Data loss or integrity issues: Critical information can be permanently lost or corrupted.
- Financial damage: Organizations may face lost revenue, recovery costs, or regulatory fines.
- Reputational harm: System failures or data breaches can erode public trust and credibility.
- Safety risks: In industrial or medical settings, disruptions can create physical hazards or endanger users.
Also read: What is ransomware? How it works and how to prevent attacks.
Logic bomb examples and notable incidents
Here are some notable incidents that illustrate the real-world impact of logic bombs:
Omega Engineering
Timothy Lloyd, the only computer system administrator at Omega Engineering, a New Jersey-based manufacturer of industrial measurement devices, planted a time bomb in the company's network. According to the Third Circuit opinion and the U.S. Department of Justice (DOJ), the code deleted about 1,200 company programs on July 31, 1996, several weeks after Lloyd was fired.
Because the files were permanently deleted and couldn't be recovered, Omega had to pursue recovery and rebuilding efforts rather than simply restoring them from usable backups.
The deletion crippled Omega’s manufacturing capabilities. According to the DOJ, the company’s losses were estimated at around $10 million in sales and future contracts. Lloyd was convicted of computer sabotage and sentenced to 41 months in federal prison.
Medco Health Solutions
The DOJ states that in October 2003, Yung-Hsun Lin, a Unix system administrator at Medco Health Solutions (a drug plan management company), planted a logic bomb across roughly 70 company servers. Lin feared he would be laid off during Medco's spinoff from Merck, a company that makes medicines and vaccines.
The code was set to deploy automatically on April 23, 2004, his birthday. After it failed to deploy, Lin reset it for the following year. A Medco administrator investigating a system error discovered the hidden code in January 2005, and the company neutralized it before it could detonate. Medco's IT security team subsequently cleaned up the malicious scripts at a cost of between $70,000 and $120,000. Lin later pleaded guilty and was sentenced to 30 months in federal prison and ordered to pay $81,200 in restitution.
South Korea cyberattack
According to the March 2023 National Cybersecurity and Communications Integration Center (NCCIC) report, a coordinated cyberattack struck South Korean banks and broadcasters, including Shinhan Bank, NongHyup, Jeju Bank, KBS, MBC, and YTN. The report says that attackers used spear-phishing emails and compromised patch management systems to deliver wiper malware known as DarkSeoul, which included a time-triggered logic bomb.
At 2:00 PM local time, the malware activated and began overwriting master boot records and hard drive data, rendering tens of thousands of computers and servers inoperable. Banking and broadcasting services were disrupted, and affected organizations shifted to recovery operations and backups. Most banking services resumed within two days, though full recovery took a bit longer.
Was Stuxnet a logic bomb?
Stuxnet, discovered in 2010, was a highly sophisticated cyberweapon widely attributed to the U.S. and Israel, though neither government has publicly acknowledged responsibility. It targeted Iranian uranium-enrichment centrifuges; multiple analyses specifically link the operation to the Natanz enrichment facility.
Stuxnet included a logic-bomb component: it activated its sabotage routines only when it detected specific Siemens Step 7 and programmable logic controller configurations. If those conditions weren't met, its destructive payload remained inactive.
However, Stuxnet was far more than a logic bomb. It also functioned as a worm, used a rootkit to conceal its presence, and exploited four zero-day vulnerabilities. Describing it as simply a logic bomb would miss the broader picture.
After Stuxnet was discovered, defenders responded with Microsoft security patches, antivirus detection and removal, Siemens cleanup guidance for affected industrial systems, and manual inspection of infected programmable logic controllers and Step 7 environments.
How to detect a logic bomb
If a logic bomb is detected before it triggers, organizations may be able to prevent the payload from executing and reduce or avoid damage. The following strategies can help organizations detect logic bombs early.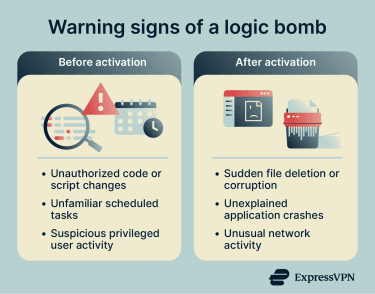
- Conduct regular code reviews: Periodically audit existing codebases, scripts, and configurations for unauthorized or suspicious modifications. Static analysis (reviewing code without executing it to identify patterns, anomalies, or hidden logic) can help surface anomalies, risky patterns, or potentially malicious logic.
- Use file integrity monitoring (FIM): FIM tools track changes to critical files, configurations, and system components, and can alert security teams to unauthorized modifications. The National Institute of Standards and Technology (NIST) paper on Security and Privacy Controls for Information Systems and Organizations recommends integrity-verification tools to detect unauthorized changes to software, firmware, and information.
- Monitor privileged users: Users with elevated access (such as administrators, developers, and contractors) have the greatest ability to plant logic bombs. Monitoring and auditing their activity, including code changes, administrative actions, and unusual access patterns, can help surface suspicious behavior.
- Deploy automated detection tools: Endpoint protection platforms, intrusion detection systems (IDS), and behavioral analysis tools can flag unusual file changes, unexpected program behavior, or suspicious code execution. Traditional signature-based antivirus software may miss novel or highly customized logic bombs, so layered detection is important.
- Watch for signs of detonation: If a logic bomb has already triggered, early indicators may include sudden file deletion or corruption, unexpected application errors, failed services, abrupt configuration changes, or unusual system behavior. Catching these signs quickly can help limit the damage and speed up recovery
How to prevent logic bomb attacks
The following measures can help reduce the risk:
Secure development and code governance
Secure development means integrating security practices throughout the software development lifecycle: from planning and design to coding, testing, and deployment. This approach may be part of a Development, Security, and Operations (DevSecOps) model and includes defining security requirements early, applying secure coding standards, conducting threat modeling, and testing for vulnerabilities before release.
The goal is to reduce the chance that insecure or harmful logic is introduced during development. Code governance establishes oversight and control over how code is created, modified, and approved.
Effective governance typically involves strict version control, restricted access to code repositories, mandatory peer reviews, formal change approval processes, and clear audit trails. These controls help ensure that code changes are attributable to specific individuals and reviewed before deployment.
Together, secure development and strong code governance make it structurally harder for unauthorized or malicious code to reach production systems. NIST’s Secure Software Development Framework (SSDF) provides structured guidance on implementing these practices.
Also read: Why software security audits matter.
Least privilege and access controls
Access controls determine who can access certain files, applications, or settings, and what actions they can take. Common controls include user roles and permissions, supported by authentication measures such as strong passwords and multi-factor authentication (MFA).
A core best practice is the principle of least privilege: giving users only the access necessary to perform their job functions. Fewer privileges mean fewer opportunities for someone to insert or trigger malicious code. Proper access controls can also help prevent privilege escalation, in which a user gains higher-level permissions to access or modify sensitive systems.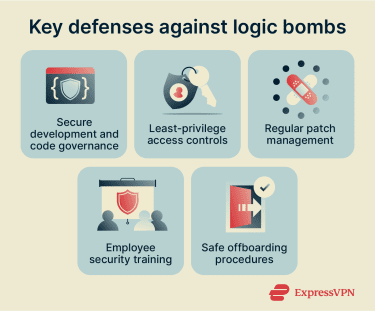
Patch management
Keeping software and systems up to date is critical, as security patches can fix vulnerabilities that attackers might exploit to introduce malicious code or gain the access needed to plant it. Patch management, the process of identifying, testing, deploying, and monitoring updates, helps close these gaps systematically.
Employee training and safe offboarding
Organizations should train staff on cybersecurity best practices, including recognizing phishing attempts and social engineering tactics used to deliver malicious code. However, it's equally important to address insider risk directly. Many documented logic bomb incidents have involved trusted employees or contractors who planted malicious code using their legitimate access.
Safe offboarding is a critical control in this context. When employees, contractors, or vendors leave an organization, promptly revoke their access to systems, files, and applications to prevent former users from exploiting lingering privileges.
What to do if you suspect a logic bomb
Note: The steps below are intended as a general overview. If you suspect a logic bomb in your organization, report it to your IT or security team immediately. Incident response should always be handled by trained professionals.
The general process involves three stages. First, contain the threat by isolating the affected device or network segment. Disconnecting compromised systems can help limit further damage, block remote access, and prevent any associated malicious activity from affecting additional systems.
Next, investigate the incident to confirm whether a logic bomb is present, determine how it was introduced, identify which systems may be affected, and understand any trigger conditions or persistence mechanisms. This typically involves forensic analysis of logs, code, and system changes.
Finally, recover and harden systems by removing the malicious code, restoring affected files and configurations to a known good state, validating backups, and verifying that no unauthorized changes remain. The post-incident review should identify the root cause, evaluate the effectiveness of the response, and lead to concrete security improvements that reduce the risk of future incidents.
FAQ: Common questions about logic bombs
Why are logic bombs dangerous?
Are logic bombs always malicious?
Who created the first logic bomb?
What is a famous logic bomb example?
What is the difference between a virus and a logic bomb?
How can I protect myself against logic bombs?
What are the symptoms of a logic bomb infection?
Can a logic bomb be neutralized once activated?
What industries are most affected by logic bombs?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN