Card testing fraud explained: How it works and how to stop it
Card testing fraud is a common tactic used by cybercriminals. It involves testing whether a stolen card is valid, typically by making small purchases or authorization attempts. This can lead to larger financial fraud attempts, and it impacts both businesses and consumers.
In this article, you’ll learn how card testing fraud occurs, attack patterns used, effective fraud detection methods, and how to prevent further attacks.
What is card testing fraud?
Card testing fraud is a tactic used by cybercriminals to check the validity of stolen credit or debit card details. They make small transactions to see if the card number works and whether the issuing bank approves the authorization. Such small transactions may be less likely to trigger certain fraud detection thresholds, which often prioritize larger or unusual purchases.
If the transaction goes through, the fraudster can make larger purchases or sell the verified card details on the dark web to other cybercriminals.
How card testing fraud works
Card testing (a part of the carding process) begins when cybercriminals obtain payment card details from data breaches, phishing or social engineering scams, malware, or card-skimming attacks. Fraudsters can also buy stolen card numbers on dark web marketplaces. Once they have the card information, they’ll test the card’s validity.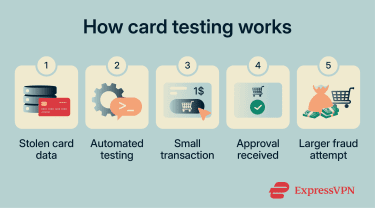
They use small-value transactions, typically through an automated script, to verify that the card is valid and whether it has funds. These transactions may be less noticeable to cardholders and may not appear on statements if they’re put in an authorization hold, which can make the activity less noticeable.
Attackers may also target “add card” forms, free trial signups, or donation pages that perform card validation checks. These systems may run $0 or $1 verification requests designed to confirm that a card is active, allowing fraudsters to extract approval signals without completing a purchase.
Signs of card testing fraud
There are several red flags that businesses and consumers may notice when cybercriminals engage in card testing fraud. Identifying these early on can help prevent additional charges or larger fraud attempts.
Warning signs for businesses
Businesses can look for the following patterns:
- High decline rates: Card testers often run large batches of stolen card numbers. Because many are invalid, expired, or blocked, this can result in an unusually high number of declined transactions within a short timeframe.
- Sudden spike in low-value attempts: A surge in small transactions within a brief period can indicate card testing activity. These transactions may involve inconsistent customer details, such as mismatched names or disposable email addresses.
- Multiple attempts from one IP: Humans can’t realistically submit large numbers of payment attempts with different cards in rapid succession, but automated scripts can. That’s why repeated attempts from a single IP (especially with many different cards) are a strong indicator of automated card testing.
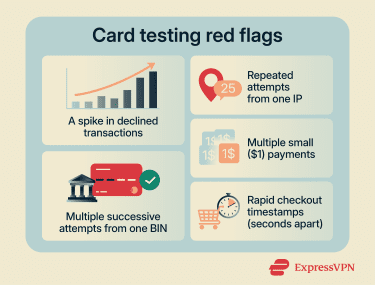
- Multiple attempts from one bank identification number (BIN): The first 6–8 digits of a card number identify the issuing bank and card type. Stolen card data is often sold or distributed in batches from the same issuer, so attackers may test many cards with the same BIN sequentially to quickly determine which ones are still active.
- Repeated retries with slight billing variations: Multiple failed attempts followed by small changes to billing details (such as different ZIP/postal codes) may indicate attempts to bypass Address Verification System (AVS) checks. This is because fraudsters often know only partial card data (card number, expiration date, and CVV). They may not know the billing ZIP or address, which many payment gateways use as an additional fraud check. To get around this, automated scripts may try multiple transactions with different ZIP codes until one passes AVS validation.
While not all signs are obvious, a high decline rate in a short timeframe is a very telling red flag, as it likely indicates some kind of automated testing (something that legitimate customers have no reason to do).
Warning signs for consumers
Consumers can also look for red flags and take action right away, which may include contacting their bank to freeze or replace the card. Here’s what to look for:
- Small unrecognized charges: Small, unfamiliar transactions (such as $1 or $2 payments) are one of the most common signs of card testing. These may lead to larger fraudulent purchases if they go unnoticed.
- Temporary authorization holds: Some test transactions may appear as pending or on-hold charges in a banking app. Even if they disappear after a few days, they can indicate that someone attempted to use your card details.
- Increased fraud alerts from issuers: Banks use fraud detection systems to monitor transactions for suspicious activity. If you receive multiple verification requests or alerts about unfamiliar transactions in a short period, it may indicate someone is attempting to test your card details.
- Unexpected trial signups or account activations: Notifications about new subscriptions, free trials, or accounts you didn’t create (especially when paired with small verification charges) could indicate your card is being tested through validation forms.
- Repeated declined attempt alerts: Push notifications or messages about declined or unsuccessful purchases you didn’t initiate may indicate someone is actively testing your card.

Types of card testing attacks and common attack patterns
Card testing is often an automated, structured process designed to avoid detection. Here are some common attack patterns.
Bot-driven card testing
As mentioned, many card testing attacks are automated, carried out by bots, scripts, or headless browsers (a browser controlled by code without a user interface). They enter the stolen credentials into checkout pages or payment forms to verify their validity. The process happens very fast, which allows attackers to test large numbers of credentials.
Bots may attempt to bypass merchant defenses; for instance, they can slow down the transaction speed to avoid detection, switch merchants if detection controls are triggered, and adjust inputs in response to validation errors.
Distributed IP and proxy testing
To avoid detection, fraudsters may use proxy services, which let them distribute their testing attacks over multiple IP addresses. Instead of sending all attempts from one location, the traffic appears to come from different sources, which makes it more difficult for businesses to detect testing based only on repeated activity from one IP address.
Some of the tools fraudsters use also allow them to simulate legitimate user behavior, for example, using different device characteristics or varying the cart content on purchase pages.
Card-on-file testing attempts
Some attackers may also target “add card” forms or subscription sign-up pages instead of traditional checkout pages. These card-on-file testing attempts may be less noticeable than repeated checkout attempts, as these systems are designed to validate payment details by performing AVS, CVV, or $0/$1 authorization checks (which may be less noticeable to users).
By submitting stolen card information to these forms, attackers can determine whether a card is active without necessarily making a complete purchase (which carries more detection risks).
Related fraud typologies
Card testing is rarely an isolated attack. It’s generally one part of a broader attempt to misuse personal or financial data, and it can overlap with other types of online fraud.
Account takeover
Account takeover occurs when someone using previously exposed credentials gains access to an existing online account. Once inside, the attacker may use stored payment details to attempt financial fraud, change login information to gain persistent access, or make purchases without the account holder’s knowledge. In some cases, attackers first test stolen card details and then use the working cards within compromised accounts to carry out larger transactions.
Identity theft
Identity theft involves the unauthorized use of someone’s personally identifiable information (PII), such as name, address, or financial details, to commit fraud. Fraudsters can use this information to open new accounts, support payment fraud attempts, and pass verification checks.
Impact of card testing fraud
Card testing affects customers and businesses alike, with results including financial losses, higher processing costs, operational disruption, and identity or account risk. Below, we go over the most common aftereffects.
Effects on businesses
Businesses, including merchants, payment gateways, and online service providers, are directly affected by card testing fraud.
Chargebacks and revenue loss
If card testing fraud is successful, attackers may make larger purchases that the cardholder later disputes. This can result in chargebacks and revenue loss, as the business has to reimburse the customer for the fraudulent charges made to their credit card.
Higher processing costs and risk flags
If merchants receive multiple chargeback demands and notice multiple declined transactions, payment processors could reclassify them as high-risk. This can result in higher processing fees and increased scrutiny from payment processors; heightened fraud activity may even lead to a merchant being enrolled in a card monitoring program.
In extreme cases, the increased scrutiny from payment processors and card issuers may result in losing the ability to process credit card payments or increased decline rates for legitimate payments.
Operational disruption and support load
Card testing fraud often involves numerous payment authorization attempts in a short timeframe, which can strain a merchant’s network and burden their infrastructure. This can slow down the website or disrupt legitimate transactions.
Mitigating the fraud attempt typically involves increased activity from the IT, fraud, or security teams and possibly implementing advanced fraud protection systems. These can lead to further operational costs and increased support load.
Effects on consumers
Consumers are directly affected by card testing fraud through unauthorized charges made to their credit or debit cards. Criminals will test the cards on merchant websites or payment gateways, potentially moving to larger transactions if initial tests are successful.
Consumers have to initiate disputes with their bank or the card issuer, which takes time and effort. While refunds are typically accepted in cases of fraud, it’s still not guaranteed that the bank will reimburse cardholders promptly.
How to prevent card testing fraud
Protecting yourself or your business against card testing fraud is a multi-step process.
Best practices for businesses
Businesses should implement several technical safeguards to protect against card testing fraud.
Transaction monitoring and velocity rules
Monitoring systems that detect early signs of card testing play an important role in prevention. Here’s how monitoring systems can be used:
- Real-time alerts: Real-time notifications help businesses respond quickly to potential card testing attempts, reducing the likelihood of additional fraudulent transactions.
- Device fingerprinting: A unique identifier for a user’s device based on things like browser settings or screen size. It lets fraud systems recognize when the same device is being used for repeated suspicious attempts (even if the IP address is different). It can also link high-risk activities across multiple user sessions and accounts.
- Automatically flag suspicious activity: Systems should identify and flag patterns like multiple failed payment attempts, inconsistent billing details, rapid series of small transactions (through velocity rules), or repeated retries using slight variations in card information.
- Customizable risk thresholds: Transaction patterns vary across industries. Monitoring systems should allow businesses to adjust thresholds and rules (via rules engines) based on their typical customer behavior and risk profile. Fraud scoring can also evaluate transactions using multiple signals (like IP reputation, device data, or transaction history) and decline them automatically.
Rate limiting and checkout friction
Rate limiting can reduce the effectiveness of automated card testing by restricting how many times a user can attempt specific actions (such as submitting payment details or completing purchases) in a given timeframe.
Merchants can limit how many payment attempts are allowed from a single IP address or temporarily suspend checkout access after repeated retries. Because card testing relies on quick, repeated attempts, limiting how often transactions can be submitted makes automated bot testing less effective.
Checkout friction is another small verification step that can distinguish between real users and bots. This can mean:
- CAPTCHA challenges
- Multi-factor authentication (MFA) for high-risk transactions
- Requiring account login before checkout
- Additional verification after repeated declines
While this may introduce friction for legitimate users, it’s an effective transaction security method against card testing attempts.
Card verification and authentication
Stricter card verification and authentication measures can help identify and deter card testing bots without adding too much friction for real users. This can involve:
- Mandatory Card Verification Value (CVV): Since Payment Card Industry (PCI) standards prohibit storing CVV codes after authorization, many large data breaches don’t include CVV data.
- AVS verification: AVS checks compare the billing address entered at checkout with the details on file. If details don’t match, the transaction may be flagged for review or declined.
- 3D Secure: This authentication protocol adds an extra security layer in online card transactions, requiring users to identify themselves with the card issuer. Verification steps can be biometric confirmation or approval via a banking app.
Card testing is more likely to succeed when merchants don’t implement strong authentication or verification controls. These measures can make automated card validation attempts much more difficult and increase the chance of early detection and mitigation.
IP and location risk controls
Reviewing IP and location data can help assess whether a transaction appears legitimate or higher risk. Many financial fraud prevention systems assign risk scores for IP addresses that showcase known abuse patterns. These can include IPs known to be associated with data centers or bot networks.
Comparing the IP address with the billing country or the card-issuing country may also surface red flags. For instance, a card issued in one country being used from an unrelated region could warrant additional verification. While the checks don’t automatically mean a transaction is suspicious, they can raise awareness about elevated risk.
Web application firewall (WAF) protection
A web application firewall (WAF) can filter incoming web traffic before it can reach the website or payment pages. It inspects requests and can automatically block patterns associated with automated abuse, like high-volume submissions, repeated payment attempts, or traffic from known malicious sources.
By catching suspicious activity early, a WAF helps reduce exposure to bots and other automated attacks.
Best practices for consumers
- Enable transaction alerts: Most banking apps let users receive real-time notifications for card transactions. Enabling these for purchases or authorization attempts can help you spot suspicious activities quickly.
- Review your statements regularly: Checking the bank or card statements for unfamiliar small transactions or authorization holds can help spot card testing fraud in its early phases.
- Avoid saving card details on unfamiliar websites: Saving payment details on untrusted or rarely used websites may increase the risk of misuse if those services experience a data breach.
- Use virtual or disposable cards when available: Some banks or financial services let you use temporary card numbers for online purchases. These can limit your exposure if the card details are compromised.
- Report suspicious activity immediately: Immediately reporting any suspicious activities on your card to the bank or card issuer can help mitigate the fraud attempt by freezing the card or investigating the activity.
How to respond to card testing fraud
After detecting card testing fraud, businesses and consumers should act quickly to minimize damage.
What businesses should do
Businesses need to act fast once card testing fraud has been identified, as this will help contain the activity and assess its scope.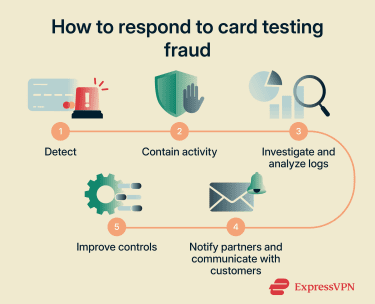
Immediate containment actions
The first priority after identifying suspicious card testing activities is containment. This can include:
- Enabling CAPTCHA or step-up authentication.
- Disabling vulnerable APIs or card-on-file validation forms.
- Temporarily pausing checkout if activity is severe.
- Tightening rate limits on checkout and payment endpoints.
- Temporarily blocking suspicious IP ranges or device fingerprints.
At this stage, the goal is to disrupt automated bot attacks and prevent further card validation attempts while not adding excessive friction for legitimate users.
Investigation and root cause analysis
After containing the threat, merchants and businesses can start analyzing how or why it happened. This can include reviewing transaction logs and timestamps, velocity patterns and retry behavior, and entry points used (like APIs or subscription forms).
Fraud detection tool responses during the incident may also offer information to inform improvements to fraud controls. Understanding whether existing security controls failed or were bypassed can help identify security gaps.
Reporting and recovery for businesses
Card testing incidents can impact payment processor and consumer relationships. To manage the situation, businesses may choose to:
- Notify the acquiring bank or payment processor.
- Document the incident for internal records.
- Monitor chargeback levels closely.
- Review fraud monitoring program thresholds.
Payment partners can provide additional monitoring or recommend temporary control adjustments to stabilize the situation. In more coordinated attacks, early reporting to the authorities may also help.
Customer support and communication
If cardholders are affected, transparent communication is essential to maintain trust and reduce confusion. Businesses may choose to inform customers of suspicious activities and explain any temporary service disruptions.
It’s also a good idea to advise customers to contact their bank if any unauthorized charges appear.
What consumers should do
- Report the suspicious activity: Contact your bank or card issuer immediately to report unexpected charges or repeated declines. They can freeze or replace your card.
- Dispute fraudulent transactions: Work with your bank to reverse any unauthorized charges.
- Update credentials: If your card details were stored on other accounts or e-commerce sites, you should change the passwords and enable MFA to prevent further abuse. A password manager like ExpressKeys can help with this.
- Look out for phishing attempts: Card testing may be part of larger identity theft attempts, so be suspicious of any unusual or unexpected communications.
- Report to the authorities (optional): For significant or repeated incidents, you can file a report with local law enforcement. This helps create a record and may assist in larger investigations.
FAQ: Common questions about card testing fraud
How do I stop card testing fraud?
What are the signs of card testing fraud?
How can businesses detect card testing quickly?
What tools help prevent card testing fraud?
Is card testing fraud a serious crime?
How is card testing different from chargeback fraud?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN