-
What is the SMTP protocol, and how does it work?
The Simple Mail Transfer Protocol (SMTP) is the standard protocol for sending and relaying email across the internet. When an email is sent, the email app (or webmail) submits the message to an outgoi...
-
Protect yourself from AOL phishing email address attacks
Phishing scams targeting America Online (AOL) users have existed since the early days of the internet, and still affect users today. They typically impersonate AOL support, claim there’s an urgent a...
-

What is private DNS? The complete guide to privacy and security
The Domain Name System (DNS) is often called the internet's phonebook: it helps translate human-readable domain names like example.com into IP addresses (and other DNS records) that devices use to loc...
-
Understanding critical infrastructure security: A comprehensive overview
Power, water, healthcare, transportation, and communications are all vital in daily life. When these services are disrupted, the impact can spread quickly. Critical infrastructure security focuses on ...
-
What is the OSI model? Understanding its layers and functions
Modern networks underpin everything from everyday web browsing to large-scale cloud systems, and their moving parts can be hard to describe consistently. The Open Systems Interconnection (OSI) model i...
-
What is cloud networking? A comprehensive overview
Cloud services power everything from everyday apps to critical business systems, and cloud networking enables those services to be reachable and manageable. Because it’s often confused with broader ...
-
What is security posture? A complete guide for organizations
To protect their IT systems, data, and customers from digital threats, organizations benefit from an overall cybersecurity approach. In practice, “security posture” is the umbrella term for how a ...
-
Bluetooth security guide: How to stay safe from wireless attacks
Bluetooth connects everything from speakers and keyboards to phones, wearables, and cars. It’s convenient, but any wireless technology can introduce risk. This guide outlines how Bluetooth works at ...
-
Chase fraud alert email: How to identify and respond to phishing
Chase regularly contacts clients by email for various reasons. The trouble is that scammers actively imitate the company, sending messages meant to trick targets into clicking links or sharing sensiti...
-
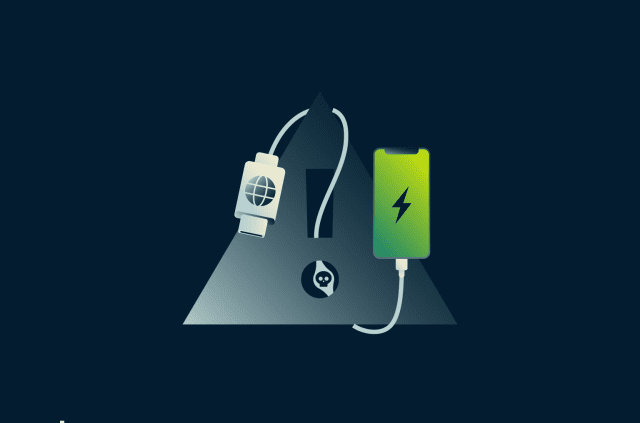
How to protect your phone from juice jacking attacks
It’s inevitable: phones need regular recharging, and sometimes that means topping up in public. Security researchers have shown that it's theoretically possible to compromise a phone through a proce...
-
- Pricing
- VPN for Teams
-
-
ExpressVPN Intudstry-leading, ultra-fast VPN with secure servers in 105 countries.
-
ExpressMailGuard Private email relay service to protect your inbox and identity.
-
ExpressKeys Secure password management, multi-factor authentication, and more.
-
ExpressAIComing soon The first consumer AI powered by confidential computing for privacy-led intelligence.
-
Identity Defender Powerful suite of ID protection, monitoring, and data removal tools
- View All Products
-
- My Account

