Expressvpn Glossary
Substitution cipher
What is a substitution cipher?
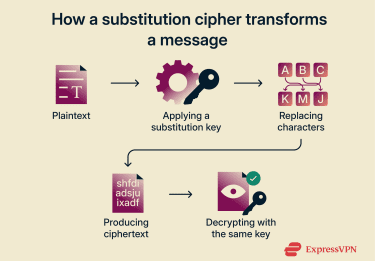
A substitution cipher is one of the oldest classical encryption methods used in classical cryptography. It replaces each element of the original message with symbols or letters according to a predetermined system (key). Its primary purpose is to obscure the message's content, making it unintelligible to unauthorized parties.
How a substitution cipher works
- Each character from the original message is substituted: Every letter or symbol in the plaintext is replaced with another character based on a predefined rule (the substitution alphabet).
- Substitution can be fixed or more complex: In a simple substitution cipher, each character maps to one replacement character. More advanced variations may use multiple mappings to reduce predictability.
- The same key is used to decode the ciphertext: The recipient applies the inverse substitution mapping defined by the key to recover the original message.
- Most substitutions apply to letters, but other characters can be used: Numbers, punctuation, or symbols may also be included, depending on how the cipher alphabet is defined.
Types of substitution ciphers
- Simple (monoalphabetic) substitution: A cipher that replaces each letter in the plaintext with one specific letter from a fixed cipher alphabet. The mapping remains consistent throughout the message, making the cipher straightforward but vulnerable to frequency analysis.
- Caesar cipher: A basic form of simple substitution that shifts each letter by a fixed number of positions within the alphabet. For example, with a shift of 3, A becomes D. Because there are only 25 non-trivial shifts (or 26 including “no shift”), this cipher is easy to break and is primarily used for educational purposes.
- Polyalphabetic ciphers: Ciphers that use multiple substitution alphabets, changing the substitution as the message progresses according to a key or scheme. This approach reduces the occurrence of repeated patterns and makes frequency analysis less effective.
- Homophonic substitution: A cipher that assigns multiple ciphertext symbols to a single plaintext character to obscure letter frequency patterns. While it complicates frequency analysis, it does not offer strong security by modern standards.
Strengths of substitution ciphers
Substitution ciphers are easy to understand and implement because they follow straightforward rules, making them useful for illustrating basic encryption concepts. Historically, they have been important in the development of classical cryptography and have influenced modern methods of secure communication.
Weaknesses and security risks
- Easy to break with analysis: Because the structure of the language does not change, (monoalphabetic) substitution ciphers are vulnerable to frequency analysis, where common letters and patterns reveal the key when enough ciphertext is available.
- No protection against modern attacks: Substitution ciphers offer no defense against automated tools or contemporary cryptographic techniques.
- Not suitable for sensitive data: They should not be used to secure digital communications or private information.
Further reading
FAQ
Is a substitution cipher secure?
How is a substitution cipher different from a transposition cipher?
What is the simplest substitution cipher?
Can substitution ciphers be broken easily?
Do modern systems still use substitution concepts?
These S‑boxes replace input values with other values according to a defined lookup table in order to introduce confusion and strengthen security against cryptanalysis.


