Expressvpn Glossary
Security monitoring
What is security monitoring?
Security monitoring refers to the process of collecting and analyzing data to detect potentially threatening activity. In enterprise environments, defining what events trigger alerts and responding to those that occur is a core function of teams tasked with maintaining cybersecurity.
How does security monitoring work?
The primary processes of security monitoring are data collection, analysis, and human investigation. Endpoints, firewalls, servers, and cloud applications regularly send logs to a central system, usually a security information and event management (SIEM) platform. The SIEM correlates and processes this data, analyzing it for warning signs based on predetermined rules. If the platform finds and flags potentially malicious activity, an alert is sent to the responsible team.
Once set up, these processes run automatically. Human intervention begins when staff examine SIEM reports. This team, often known as a security operations center (SOC) in larger organizations, reviews and responds to alerts as they come in.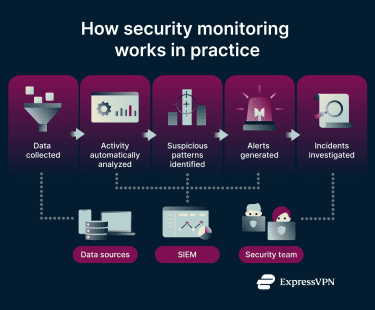
Types of security monitoring
Depending on the size, nature, and needs of an organization, security monitoring may involve several different layers. These can include:
- Endpoint monitoring: Tracks activity on devices and servers to identify malware, abnormal behavior, and unauthorized software.
- Cloud security monitoring: Focuses on access patterns, configuration changes, and workload activity in cloud platforms.
- User activity monitoring: Reviews account behavior and user actions across systems to identify compromised credentials, policy violations, and insider threats.
- Application monitoring: Measures performance, availability, and runtime behavior in applications to identify errors, slowdowns, and abnormal activity.
Why security monitoring is important
Early threat detection is the key benefit of active security monitoring. Incidents that are responded to swiftly are less likely to result in serious consequences. Additionally, the breadth of data provided by security monitoring can help organizations improve their systems over time. Continuous oversight also supports compliance with security and privacy standards, such as the General Data Protection Regulation (GDPR), which require organizations to keep logs or be sufficiently able to detect breaches.
Tools and technologies used in security monitoring
Comprehensive security monitoring incorporates multiple platforms and systems, including:
- SIEM platforms: Centralize and analyze security logs for potential threats by collecting data from across the organization’s infrastructure.
- SOAR systems: Automate investigation and response workflows to reduce manual work and support security operations.
- Intrusion detection and prevention systems (IPS/IDPS): Monitor network traffic for malicious activity and block threats.
- Endpoint detection and response (EDR) tools: Monitor endpoints for signs of compromise and support swift responses.
- Threat intelligence platforms: Deliver up-to-date information on emerging threats to enhance detection and improve resilience.
- Network detection and response (NDR) tools: Use machine learning and behavioral analytics to identify and block potentially malicious traffic.
Security monitoring vs. network monitoring
Though some security monitoring tools work on the network level, network monitoring is a distinct process only indirectly related to security. Rather than block threats, network monitoring tools automatically gather data about a network’s health, recording factors such as uptime, latency, and bandwidth. That said, performance issues can be caused by threats, so network monitoring does play some role in security monitoring.
Best practices for effective security monitoring
Effective security monitoring depends on consistent processes and well-maintained detection capabilities:
- Clear alert thresholds: False positives may be reduced by more strictly defining which events should trigger investigation.
- Centralized log management: Unified SIEM systems can collect and correlate data from across the organization’s infrastructure.
- Balanced automation: Automated detection and response systems may be paired with human oversight for accurate decision-making.
- Updated detection rules: Analytics, signatures, and threat definitions can be regularly updated to maintain relevance.
- Encrypted communication: Logs may be transferred through an encrypted tunnel to enhance privacy and security.
Common challenges in security monitoring
Organizations may struggle with the high volume of alerts generated in modern environments. When detection rules are poorly configured, analysts face alert fatigue, which slows investigation and increases the risk of missing real threats. Some teams also lack the specialized skills required to manage complex monitoring systems or interpret the vast array of threat data. Security monitoring is particularly challenging in hybrid or multi-cloud environments, where data is spread across different platforms and may adhere to different logging standards.
At the same time, monitoring must respect privacy requirements and avoid collecting unnecessary personal information. Balancing visibility with compliance and privacy obligations remains a key operational concern for many organizations.
Further reading
- What is cybersecurity? A simple guide for beginners
- What are network protocols? A complete guide
- Zero-trust architecture: What it is, how it works, and why it matters


