Expressvpn Glossary
Security automation

What is security automation?
Security automation is the use of software that assists with specific security tasks such as detecting, investigating, and remediating threats. It focuses on managing repetitive and predictable activities that would otherwise require manual effort from analysts. By applying predefined rules, scripts, or playbooks, these systems can generate alerts and trigger response actions with limited human intervention.
How does security automation work?
Security automation typically follows a structured, end-to-end workflow that moves from raw system data to documented outcomes.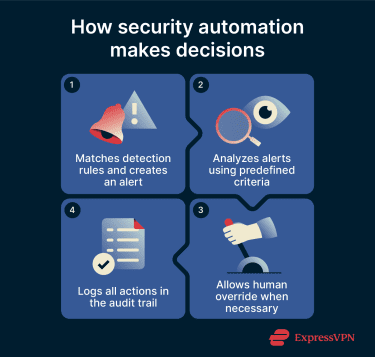
- Detection: Custom detection rules analyze incoming data and automatically trigger alerts when defined conditions are met.
- Analysis: Using AI, machine learning (ML), or automation workflows, the system evaluates alerts to determine whether activity indicates a real incident.
- Response: When rule conditions are met, the system can automatically initiate predefined remediation or containment actions.
- Reporting: Incidents and actions are documented, supporting structured reporting and ongoing analysis of security events.
Types of security automation tools
Security automation appears in several specialized tool categories, each designed for a distinct role within modern security programs.
- Security orchestration, automation, and response (SOAR): Integrates and coordinates separate security tools from a central platform to automate prevention and response activities.
- Extended detection and response (XDR): Collects data from endpoints, networks, cloud services, email, Software-as-a-Service (SaaS) applications, and identity systems to deliver coordinated protection.
- Security information and event management (SIEM): Collects, aggregates, and analyzes large volumes of data from applications, devices, servers, and users in real time.
- Vulnerability management tools: Provide a risk-based approach to discovering, prioritizing, and remediating vulnerabilities and misconfigurations on an ongoing basis.
Key considerations
Security automation systems can produce false positives, where legitimate activity is incorrectly identified as a threat. Additionally, high volumes of inaccurate alerts may require manual review and tuning.
Excessive privileges could increase the potential damage if an account is compromised, and logs may contain sensitive or personally identifiable information (PII). This could create privacy risks if not properly protected. Finally, third-party integrations and remote access paths can expand the overall attack surface.
Further reading
- XDR in cybersecurity: What it is and why it matters
- NDR vs. XDR: Key differences and how to choose
- What is big data security and privacy?
- IoT cybersecurity: What it is and why it's critical for modern networks

