Expressvpn Glossary
Next-generation firewall
What is a next-generation firewall?
A next-generation firewall (NGFW) is a network security device that builds on a traditional stateful inspection firewall by adding application-aware inspection and typically integrated intrusion prevention capabilities. It makes traffic filtering decisions using context beyond basic network and transport data, such as identifying applications and enforcing policy based on that application-level visibility.
Key features of a next-generation firewall
- Deep packet inspection (DPI): Examines packet contents to support application identification and detect policy violations (often in combination with threat prevention engines).
- Intrusion prevention system (IPS): Detects and blocks known exploits and suspicious traffic patterns.
- Application filtering: Identifies and controls applications regardless of port or protocol.
- User identity awareness: Associates traffic with users or groups for policy enforcement (implementation varies by vendor/environment).
- Encrypted traffic inspection: Decrypts and inspects Transport Layer Security (TLS) sessions where permitted and configured.
- Threat intelligence integrations: Uses external threat intelligence feeds (and, in some products, optional sandboxing) to help identify and block emerging threats.
How a next-generation firewall works
An NGFW examines traffic at multiple Open Systems Interconnection (OSI) layers, typically, Layer 3 (network), Layer 4 (transport), and Layer 7 (application), and can use techniques such as signature-based intrusion prevention (and, depending on the product, additional behavioral or heuristic methods) to detect and block malicious activity.
It can identify applications regardless of port, associate traffic with user identities for policy enforcement, and log events to support consistent policy enforcement across on-premises and distributed environments.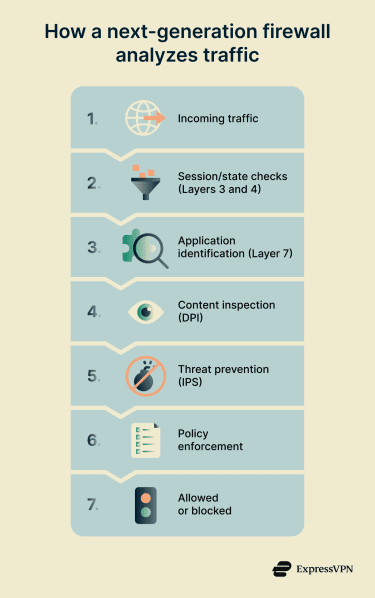
Advantages and limitations
| Advantages | Limitations |
| Improves detection and blocking beyond basic port/protocol filtering | Higher performance requirements can increase latency under load |
| Reduces gaps from applications that don't rely on fixed ports | More complex to deploy and tune; configuration errors can reduce effectiveness |
| Can support more consistent policy enforcement across on-premises and distributed environments | Secure Socket Layer (SSL) / TLS inspection adds operational risk (certificate management, compatibility issues) |
| Supports clearer audit trails for investigations and governance (via centralized logging) | Higher total cost (hardware, licenses, operational effort) |
Common use cases
- Business and data centre protection: Enforce security controls at network boundaries and between internal zones.
- Remote work security: Extend access and application policies to remote connections when traffic is routed through NGFW controls.
- Application monitoring: Identify application usage for policy and governance purposes.
- Threat prevention at the perimeter: Block common inbound exploit attempts and known malicious traffic patterns.
- Cloud environments: Enforce a consistent policy for traffic entering, leaving, or moving within cloud networks.
NGFW vs. traditional firewall
Traditional firewalls primarily base decisions on IP addresses, ports, and protocols, with more limited visibility into application context and user identity (depending on firewall type and configuration).
An NGFW adds application awareness and integrated threat prevention to support more context-driven policy decisions and reduce reliance on fixed ports or simple protocol patterns for identifying traffic and threats.
Security risks without a next-generation firewall
- Reduced threat prevention: Known exploit attempts and other malicious traffic patterns are more likely to pass through basic port/protocol filtering.
- Encrypted blind spots: Threats within SSL/TLS traffic may go undetected when encrypted traffic is not decrypted and inspected.
- Limited identity-based control: Policies based on users, groups, and roles can be harder to enforce, weakening least-privilege access controls.
- Higher breach likelihood: Lower visibility and fewer inline inspection controls can increase the risk of unauthorised access and data exposure.
- Evasion through allowed traffic: Attacks that use common ports and application-layer techniques are more likely to blend into permitted traffic when controls rely mainly on ports and protocols.
Further reading
- What is a firewall, and how does it work
- VPN vs. firewall: Key differences and when to use each
- VPNs, firewalls, endpoint security: What does your team really need?


