Expressvpn Glossary
Media Access Control (MAC)
What is Media Access Control?
Media Access Control (MAC) is a sublayer of the data link layer (Layer 2) in the Open Systems Interconnection (OSI) networking model. It defines how devices access a shared network medium and identify network interfaces on a local network using MAC addresses.
How does Media Access Control work?
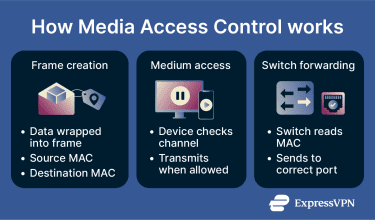
The MAC layer handles several key functions when data is ready to be sent across a local network:
- Encapsulates data into a frame: Takes data from the upper layer and packages it into a structured unit called a frame.
- Adds source and destination MAC addresses: Includes the sender’s and receiver’s hardware addresses so devices on the local network can identify each other.
- Adds error-detection information: Appends a Frame Check Sequence (FCS) that allows the receiving device to detect whether the frame was corrupted during transmission.
- Controls when transmission occurs: Follows defined access rules that determine how devices access a shared network medium to prevent interference when multiple devices share it.
Why is Media Access Control important?
MAC is essential for stable and efficient local networking: it’s what enables multiple devices to share the same network without interfering with one another.
On a local network, many devices may use the same physical medium, such as an Ethernet cable or a wireless signal. Without defined rules for access, transmissions could overlap, leading to data corruption and unreliable communication. The MAC sublayer establishes those rules, ensuring orderly and efficient use of the network medium.
MAC is also essential for device identification. Using unique MAC addresses allows frames to be delivered to the correct destination within a local network. In addition, MAC supports data integrity by including error-detection mechanisms that help devices identify corrupted frames.
Where is it used?
MAC is used in most local and short-range networking technologies:
- Ethernet local area networks (LANs).
- Wi-Fi networks and wireless access points.
- Bluetooth and other short-range links.
- Enterprise network access control (NAC) systems.
- Internet of Things (IoT) networks and home routers.
Risks and privacy concerns
Although MAC is essential for local networking, it has certain security and privacy limitations.
- MAC spoofing and filtering limitations: MAC addresses can be changed through software, allowing a device to impersonate another. Because of this, network security measures based solely on MAC address filtering can be easily bypassed.
- Device tracking on local networks: Since a MAC address uniquely identifies a network interface, it can potentially be used to monitor or track devices on shared networks, such as public Wi-Fi. Modern operating systems reduce this risk by using MAC address randomization.
- Rogue access points: Malicious wireless networks may collect MAC addresses from nearby or connected devices for profiling or monitoring purposes.
Further reading
- What is a MAC address and why does it matter?
- What is MAC address spoofing?
- What is Ethernet? A full guide for VPN and cybersecurity users
- What is a VLAN? A complete guide to virtual LANs

