Expressvpn Glossary
Encryption key
What is an encryption key?
An encryption key is a cryptographic value that an algorithm uses to encrypt, decrypt, or otherwise protect data. Some keys are secret, such as symmetric keys and private keys, while others, such as public keys, are designed to be shared.
How does an encryption key work?
Encryption keys are generated by software or hardware designed to produce random, unpredictable values. Encryption algorithms use these keys with plaintext data to create ciphertext.
Encryption can be symmetric or asymmetric. This affects how encryption keys are used and shared.
In symmetric encryption, both parties use the same secret key to encrypt and decrypt data, so that key must be shared securely. In asymmetric encryption, two related keys are used instead: a public key, which can be shared openly, and a private key, which is kept secret.
In practice, asymmetric methods are often used to securely exchange or establish a shared symmetric key, which is then used to encrypt the actual data.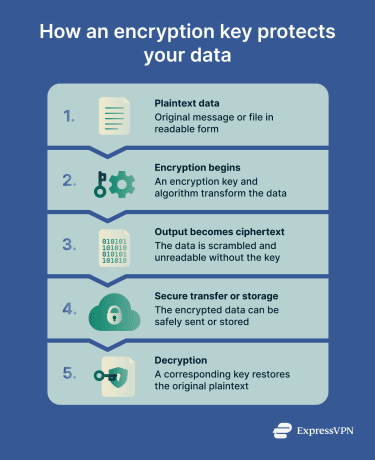
Why is an encryption key important?
Encryption keys are important because they control access to protected data. They also:
- Enable integrity and source authentication: In digital signatures, keys help verify that data has not been altered and that it was signed by the holder of the corresponding private key.
- Protect data in transit and at rest: Secure information as it moves across networks and while it’s stored.
- Limit the impact of exposure: Even if encrypted data is captured, properly managed keys help prevent it from being used.
- Support security and compliance controls: Many standards require strong encryption and key management to protect sensitive information.
Where are encryption keys used?
Encryption keys are used across many systems to protect data and secure communication. Common uses include:
- Secure website connections: Keys protect data sent over HTTPS and Transport Layer Security (TLS).
- Virtual private network (VPN) connections: Keys create encrypted tunnels that protect internet traffic on public and private networks.
- End-to-end encrypted messaging: Keys ensure only the sender and recipient can read messages.
- Device and file encryption: Keys protect data stored on devices and drives, helping prevent access if they’re lost or stolen.
- Wi-Fi and enterprise networks: Keys secure wireless traffic and support centralized protection across multiple devices and locations.
Risks and privacy concerns
Some common risks and privacy concerns when using encryption keys include:
- Weak or predictable key generation: Keys that aren’t truly random are easier to guess.
- Key reuse: Using the same key across systems or sessions increases exposure if it’s compromised.
- Insecure storage: Keys stored in plaintext or accessible locations can be stolen.
- Poor key rotation: Failing to replace keys regularly extends the impact of a breach.
- Permanent data loss: Losing a key without a backup makes encrypted data inaccessible.
Further reading
- Symmetric vs. asymmetric encryption: What’s the difference
- What is AES encryption?
- Encryption protocols explained: What they are and how they work
- What is TLS encryption, and how does it protect your data?
- What is cryptography?



