Expressvpn Glossary
Decryption
What is decryption?
Decryption is the process of converting encrypted data (ciphertext) back into its original readable form (plaintext) using a decryption key and algorithm. It’s a fundamental cryptographic operation that allows authorized parties or systems to recover and use protected information.
How does decryption work?
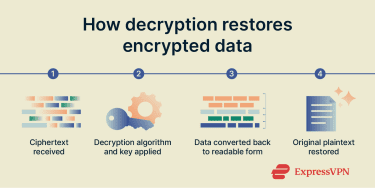 During decryption, encrypted data is received from a sender or retrieved from storage. The system provides the correct cryptographic key (shared in symmetric encryption or private in asymmetric encryption) to the decryption process. The decryption algorithm then uses this key to transform the data back into its original readable form.
During decryption, encrypted data is received from a sender or retrieved from storage. The system provides the correct cryptographic key (shared in symmetric encryption or private in asymmetric encryption) to the decryption process. The decryption algorithm then uses this key to transform the data back into its original readable form.
Types of decryption
Decryption methods differ in how cryptographic keys are used and managed. Common types include:
- Symmetric decryption: Uses the same secret key for both encryption and decryption. Typically fast and efficient for large volumes of data, but it’s dependent on secure key distribution. Often implemented with algorithms such as Advanced Encryption Standard (AES).
- Asymmetric decryption: Uses a key pair, with a public key for encryption and a private key for decryption. Generally slower but well-suited to secure key exchange and identity verification. Commonly implemented with algorithms such as Rivest–Shamir–Adleman (RSA).
- Manual or classical decryption: Historical hand or mechanical techniques that relied on pattern analysis to recover messages, such as substitution and transposition ciphers. While they are no longer considered secure, they were foundational to modern encryption and decryption methods.
Why is decryption important?
Decryption is an integral part of encryption systems. It enables secure communication across public and private networks and allows for the retrieval of encrypted data stored on devices, servers, and in cloud environments. It helps maintain the confidentiality, integrity, and privacy of information by ensuring that only authorized parties can access readable data.
Decryption also forms a core component of modern security technologies such as virtual private networks (VPNs) and HTTPS.
Security and privacy considerations
The security of encrypted data depends on the strength of the encryption algorithm and secure key management. If cryptographic keys are exposed or stolen, attackers can decrypt and read private data. To reduce this risk, organizations use measures such as key rotation, multi-layer encryption, and strict access controls.
Many modern security protocols and services rely on strong standards, such as 256-bit AES encryption, which are designed to make decrypting intercepted data without the correct key extremely difficult.
Decryption vs. encryption
Encryption converts plaintext into ciphertext using a cryptographic algorithm and key, while decryption converts ciphertext back into plaintext using the corresponding key and algorithm. Both processes rely on cryptographic keys to protect information.
Further reading
- What is data encryption?
- Zero-trust data protection explained
- What is data privacy, and why does it matter?
