Expressvpn Glossary
Data leakage
What is data leakage?
Data leakage is the unauthorized or unintended disclosure, exposure, or transmission of sensitive data to unintended or unauthorized recipients, whether intentional or accidental. It matters because sensitive data leaving approved systems, locations, or audiences can create security, privacy, and compliance risks.
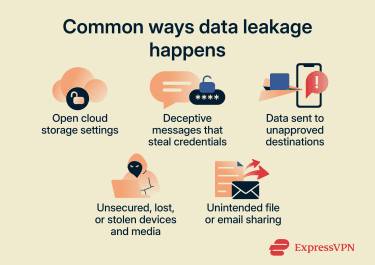
Common causes of data leakage
- Human error and mishandling: Accidental sharing, wrong recipients, unsecured storage, or failure to follow policy.
- Phishing and social engineering: Deception used to steal credentials or trigger unsafe actions that expose data.
- Misconfiguration and weak access controls: Incorrect permissions, excessive privileges, or weak authentication.
- Software and system vulnerabilities: Unpatched or outdated systems that can be exploited to access or disclose sensitive data.
- Third-party exposure: Vendors or partners with access experience a breach or otherwise expose shared data.
- Device and media loss or exposure: Lost or stolen laptops, mobile devices, or removable drives, especially when data is not encrypted.
Types of data leakage
Depending on cause and intent, data leakage may be classified as:
- Accidental leakage: Unintentional exposure, often driven by misconfiguration, routine mistakes, or unsafe handling.
- Process-related leakage: A form of accidental leakage linked to breakdowns in storage, retention, disposal, or approval workflows.
- Transmission-related leakage: Exposure while data is being sent or transferred, for example, through insecure transfer methods, unauthorized uploads, or misdirected communications.
- Malicious leakage: Intentional exposure caused by an attack or harmful misuse of access, including insider activity, malware, or credential theft through social engineering.
Security risks and consequences
Data leakage can expose personal, financial, or confidential business information, creating risks for service providers, organizations, and individuals. When personal or financial data is involved, exposure can increase the likelihood of identity theft, financial fraud, and follow-on attacks such as phishing.
For organizations, leaks can reduce customer trust and harm reputation, particularly if incidents become public. Legal penalties or compliance actions may also apply when regulated data is mishandled. Disclosure of sensitive business information (such as intellectual property, internal strategies, or trade secrets) can weaken a competitive position.
How to prevent data leakage
Data leakage prevention typically uses layered controls to reduce the chance of unauthorized exposure:
- Enforcing strict access controls and role-based permissions to limit data access to approved users.
- Using encryption for stored and transmitted data to reduce exposure if systems or networks are compromised.
- Employing data loss prevention (DLP) tools to detect, monitor, and restrict unauthorized data movement.
- Training employees on secure data-handling practices, including proper storage, sharing, and deletion of sensitive information.
- Applying additional security controls such as multi-factor authentication (MFA), endpoint protection, regular vulnerability scanning and remediation, network firewalls, and zero-trust principles.
- Assessing and monitoring third-party providers to handle sensitive information to identify and reduce data exposure risks.
Data leakage vs. data breach
Both involve the exposure of sensitive information, but they differ in how the exposure happens.
Data leakage often refers to the intentional or unintentional release of data to an untrusted or unauthorized environment, commonly through misconfiguration, weak controls, human error, or misuse of access
A data breach refers more broadly to the loss of control over, or compromise, unauthorized access to, acquisition of, or disclosure of sensitive information. Breaches are often caused by attacks such as credential theft, phishing, or malware, but they can also involve insiders or authorized users acting for unauthorized purposes. A breach can result in data leakage, and the two terms may overlap depending on how an incident is defined.
Further reading
- How data leaks are fueling the surge in identity theft cases
- How to prevent potential data leaks on iOS with ExpressVPN
- Massive social media breaches are exposing your private life
- Data leak on an iPhone: How to view and fix leaked passwords

