Expressvpn Glossary
Ciphertext

What is ciphertext?
Ciphertext is data that has been converted from readable plaintext into an unreadable form by an encryption algorithm. Its core purpose is to prevent unauthorized parties from accessing or understanding the information while it is stored or transmitted.
How does ciphertext work?
Ciphertext isn’t a process, but the end result of running plaintext through a series of controlled steps based on an encryption key. These steps can include rearranging the data, substituting characters or bits, and performing mathematical operations that scramble the structure of the original message.
The output, which is the ciphertext, appears random to an observer without the key and can’t be interpreted without the matching decryption key, which guides the algorithm in reversing those steps and reconstructing the plaintext.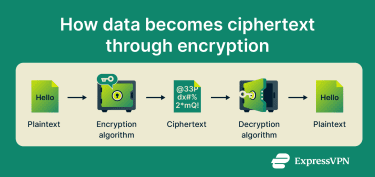
Types of encryption that generate ciphertext
Two main forms of encryption produce ciphertext. Each relies on different key structures and is used in different parts of modern security systems.
- Symmetric encryption: Uses one shared key for both encryption and decryption. It is efficient and suited to situations where the key can be distributed securely in advance. Common uses include full-disk encryption and other high-volume data protection tasks.
- Asymmetric encryption: Uses a public key to encrypt data and a private key to decrypt it. The separation of keys allows secure communication over open networks. It is used in secure key exchange.
Why is ciphertext important?
Ciphertext protects the confidentiality of data in digital systems by ensuring that intercepted or improperly accessed information can’t be understood without the correct decryption key. It supports secure activities such as online transactions, private communication, corporate data exchange, and remote access. It also helps organizations comply with data-protection requirements by keeping sensitive information unreadable to unauthorized parties.
Security and privacy considerations
The security of the ciphertext depends on the strength of the encryption method and the secrecy of the keys. Weak or outdated designs are vulnerable to brute-force attacks (systematically guessing the key), and they can also allow attackers to recover parts of the plaintext or even the key itself.
Modern algorithms like 256-bit Advanced Encryption Standard (AES) and 2048-bit Rivest-Shamir-Adleman (RSA) remain secure against current attacks when properly implemented and used. However, future large-scale quantum computers may be able to compromise some public-key algorithms like RSA, which is why post-quantum algorithms are being designed.
Further reading
- What is data encryption?
- What is data privacy and why it matters
- Symmetric vs. asymmetric encryption
