Expressvpn Glossary
Access control list (ACL)
What is an access control list?
An access control list (ACL) is a set of rules that defines who can access a resource, such as a file, directory, or network interface, and what operations are allowed for that resource. Network administrators use these lists to allow or deny access by filtering unwanted traffic.
How does an access control list work?
When a user or device requests access to a resource, the system checks the resource’s ACL to see who’s allowed and what actions are permitted. Based on these predefined rules, it either passes or gets denied, and it may be logged for auditing purposes.
On network devices, ACLs inspect packet headers, including IP addresses and ports, and then allow or block the traffic based on the rules.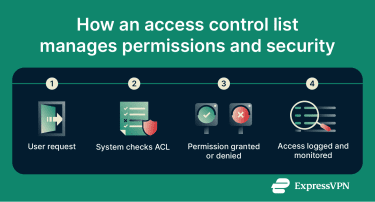
Types of access control lists
- File system ACLs: These assign, read, write, and execute rights to specific users or groups.
- Network ACLs: Network ACLs filter traffic on network devices using IP addresses, protocols, and ports.
- Standard ACLs: These check the source IP address of the data packet entering or leaving the network.
- Extended ACLs: These examine where the traffic comes from, where it’s going, and which port it uses.
Why are access control lists important?
ACLs prevent unauthorized access to sensitive systems and data. They also improve network visibility by letting administrators see who accessed resources. Additionally, ACLs are used to isolate network segments to limit lateral movement within internal systems.
While no law mandates ACLs, they’re an important aspect of regulatory compliance and help protect confidential data.
Security and privacy considerations
Poorly configured ACLs can block legitimate access or expose user data, and static lists become liabilities if not updated consistently.
Multi-factor authentication (MFA) and regular internal reviews should be used alongside ACLs to protect sensitive data, as well as a virtual private network (VPN) to encrypt network data and limit data tampering.
Common use cases
- File protection: ACLs are used to limit who can view or modify corporate documents; for example, an ACL could allow the HR team to view employee payment information without other colleagues getting access to it.
- Network segmentation and compliance: Organizations help reduce breaches by isolating network segments and applying rules on routers and firewalls. Cloud storage companies use ACLs to help remain compliant by only allowing specific identities to access important data.
- Traffic filtering: ACLs can be used to set up rules for filtering inbound and outbound traffic, such as denying IP addresses from an unknown source.
- Internet of Things (IoT) and guest networks: ACLs can restrict devices to specific servers and prevent guest users from reaching internal systems.
Advantages and Limitations
Advantages:
- Provides granular permissions.
- Works at the file, application, and network layers.
- Simple to implement for small to medium networks.
Limitations:
- Becomes cumbersome to manage in large networks.
- Misconfiguration may block legitimate traffic or create security gaps.
- Static ACLs require regular manual updates as user roles change.
Further reading
FAQ
What’s the main purpose of an ACL?
An access control list (ACL) is a set of rules that defines which users, systems, or processes are permitted to access a resource and specifies the operations they are allowed to perform. It supports enforcement of security and compliance policies.
How does an ACL differ from a firewall rule?
Access control lists (ACLs) are applied to specific interfaces or resources and provide basic, ordered rule sets for permitting or denying traffic. Firewalls offer broader, stateful inspection and policy enforcement across networks, often including additional capabilities such as intrusion detection and threat filtering.
Can ACLs prevent data breaches?
Access control lists (ACLs) reduce the risk of but don’t fully prevent breaches by restricting access and blocking unwanted traffic.


