-

What is IIoT and why its security matters more than ever
In modern industry and operations, more devices than ever are connected to networks and each other through the Industrial Internet of Things (IIoT). This connectivity allows factories, plants, utiliti...
-

How can you protect your home computer?
Many people underestimate how vulnerable their personal computers are. Without corporate-grade defenses or IT oversight, home setups are often easy targets. At the same time, new trends such as malwar...
-
The ultimate guide to recursive DNS: Everything you need to know
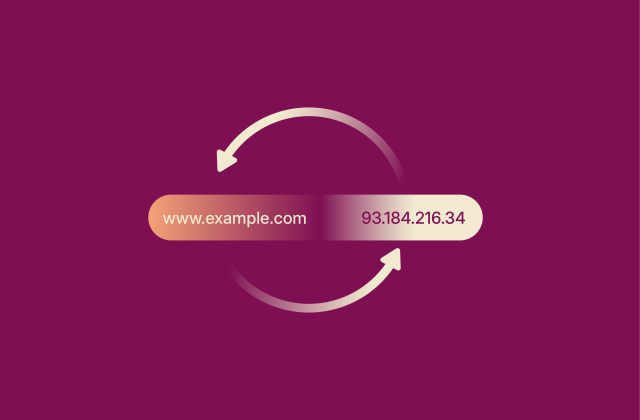
The internet runs on a complex system called the Domain Name System (DNS) that turns human-readable domain names into machine-readable IP addresses. A recursive DNS server is a vital part of this syst...
-

What is computer networking and how VPNs fit in
Computer networks form the backbone of modern digital communication. Learning how these networks operate will help you better understand the modern digital landscape and make smarter decisions about p...
-

Domain hijacking vs. DNS poisoning: Key differences and how to stay protected
Domain-based attacks, which target the control or resolution of internet domains, are one of the major cyber threats of today. Two common and high-impact forms of domain-based attacks are domain hijac...
-

Spotify Private Session: What it is and how to use it
Your listening habits can be deeply personal, and sometimes you might not want everyone to know what music or podcast you’re streaming. Spotify's Private Session feature gives you a way to keep that...
-

A complete guide to MPLS VPN services for secure and reliable connectivity
In enterprise networking, the choice of how to connect offices, data centers, and remote users has a direct impact on performance, reliability, and cost. One solution is a multiprotocol label switchin...
-

What is DNS TTL? Best practices for privacy and performance
Every time you visit a website, your device sends a request to a Domain Name System (DNS) server, which looks up the domain name and then sends you the numerical IP address associated with it. The res...
-

What is 128-bit encryption, and is it still secure in 2026?
128-bit encryption remains a cornerstone of online security, protecting everything from virtual private network (VPN) traffic to mobile apps. It’s widely used and has never been reported to have bee...
-

Zeus virus (Zbot malware): What it is and how to stay protected
The Zeus virus is best known for fueling large-scale financial cybercrime and stealing banking credentials. Although the original Zeus virus is no longer active, it spawned numerous variants that rema...

Spring deal: Get a free upgrade for 3 months on annual offers.
Spring deal: Free upgrade on annual offers. Claim now!
Claim Now!

