Expressvpn Glossary
Stateful firewall
What is a stateful firewall?
A stateful firewall monitors the state of active network connections and evaluates traffic based on whether packets belong to an established session. It identifies and blocks packets that don’t match expected connection behavior or defined session rules.
By assessing traffic in the context of an entire session and not in isolation, the firewall makes filtering decisions based on connection history rather than individual packets alone.
How a stateful firewall works
A stateful firewall maintains a record of active connections in a structure commonly known as a firewall state table. It stores the session data found in packet headers, such as IP addresses, ports, protocol type, and connection status. If the data packet matches an existing session, it allows the return traffic. If it doesn’t match or violates expected connection patterns, the firewall blocks it.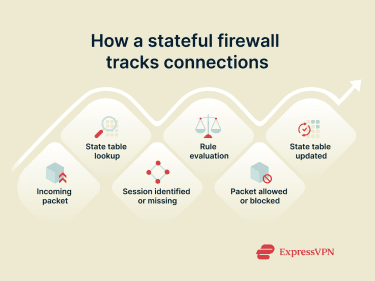
Stateful firewalls monitor common network protocols such as Transmission Control Protocol (TCP) and User Datagram Protocol (UDP). With a TCP connection, the firewall inspects all three stages of its connection to identify any possible threats. For stateless protocols like UDP, the firewall creates and stores context data so it can track the virtual connection. By doing so, it can inspect the entire session instead of each packet individually.
Key features of a stateful firewall
A stateful firewall is defined by its ability to evaluate traffic in context rather than as isolated packets. Its key features include:
- Connection-aware packet filtering.
- Automatic handling of return traffic for established sessions.
- Dynamic tracking of session state and connection status.
- Improved detection of spoofed or unexpected packets.
- Ongoing updates to the firewall state table as traffic flows.
These features allow the firewall to distinguish between legitimate response traffic and unsolicited or abnormal packets.
Stateful vs. stateless firewall
The main difference between a stateful and stateless firewall is how they evaluate traffic.
A stateful firewall tracks ongoing sessions and evaluates packets based on their relationship to an existing connection. It uses session context to determine whether traffic is expected, making it more effective at blocking unexpected or malicious traffic. Stateful firewalls also automatically manage return traffic and the flow of data within a session, providing a context-aware layer of security.
A stateless firewall evaluates each packet individually, relying only on predefined rules such as IP addresses, ports, and protocols. It can’t determine whether packets belong to a legitimate session, making it faster but less secure than a stateful firewall.
Strengths and weaknesses of a stateful firewall
| Advantages | Limitations |
| Filters traffic based on connection state rather than individual packets | Requires additional memory and processing to maintain session state |
| Distinguishes between expected and unsolicited traffic | Performance can be affected as the number of active sessions grows |
| Automatically manages return traffic for established connections | State table size increases with higher traffic volumes |
| Reduces acceptance of spoofed or out-of-context packets | Configuration and management are more complex than simple packet filtering |
| Maintains ongoing awareness of session behavior | Doesn’t provide the application-level inspection of more advanced next-generation firewalls (NGFWs) |
Security risks without stateful inspection
Networks that lack stateful inspection may face increased exposure to certain risks. Without session awareness, it becomes more difficult to identify spoofed packets, unexpected return traffic, or suspicious patterns from port scans, TCP session hijacking, or amplification-based denial-of-service (DoS) attacks. Abnormal connection patterns may also be harder to detect, increasing susceptibility to network-based attacks that exploit simple packet-filtering rules.
Further reading
- VPN vs. firewall: Key differences and when to use each
- What is a firewall & how does it work
- How to open ports on a router


