Expressvpn Glossary
Spanning Tree Protocol (STP)

What is the Spanning Tree Protocol?
The Spanning Tree Protocol (STP) is a network protocol designed to prevent loops in Ethernet networks by blocking redundant paths. Loops can cause problems like network congestion; by helping to avoid these issues, STP promotes network stability and performance.
How does the Spanning Tree Protocol work?
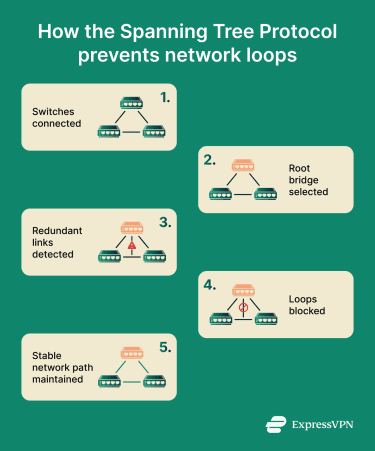 STP follows the following process:
STP follows the following process:
- Root bridge selection: The protocol selects a root switch based on the lowest bridge ID, which is determined by priority and Media Access Control (MAC) address.
- Path calculation: It calculates the optimal routes for data to travel by comparing path costs, which reflect link speed. It selects the lowest-cost paths to the root bridge.
- Port role assignment: Ports are assigned roles (root, designated, or blocked/alternate) to prevent loops.
- Port state management: Redundant ports move through states (blocking, listening, learning, and forwarding) to maintain a loop-free topology.
- Bridge Protocol Data Unit (BPDU) exchange: Switches continuously exchange BPDUs to share information about bridge IDs, path costs, and topology changes, enabling STP decisions to be made and updated.
Types of Spanning Tree Protocol
There are three main varieties of STP:
- STP (IEEE 802.1D): The original protocol.
- Rapid Spanning Tree Protocol (RSTP) (IEEE 802.1w): A faster, upgraded version of STP.
- Multiple Spanning Tree Protocol (MSTP) (IEEE 802.1s): A version of STP that supports multiple spanning tree instances, allowing virtual local area networks (VLANs) to be mapped to each instance for better efficiency.
Why is the Spanning Tree Protocol important?
STP plays a vital role in keeping data flowing smoothly and network operations running correctly in Ethernet networks. By preventing loops, it avoids broadcast storms, where excessive looping traffic overwhelms network devices.
It also allows network redundancy by selectively blocking redundant links while keeping alternative paths available; if a primary link fails, traffic can be rerouted automatically. This helps complex networks, such as those found within data centers and enterprises, to maintain continuous, efficient connectivity.
Security and privacy considerations
To minimize risks when working with STP, network administrators can:
- Enable Root Guard to prevent unauthorized switches from becoming the root bridge.
- Enable BPDU Guard to disable ports that receive unexpected BPDUs, protecting against rogue devices.
- Manually configure bridge priorities to ensure critical switches maintain intended roles in the topology.
- Use BPDU filtering on edge ports to prevent edge devices from sending BPDUs into the network.
- Regularly monitor STP topology changes to detect unusual events that may indicate attacks or misconfigurations.
Common issues with the Spanning Tree Protocol
Possible problems users may run into when working with STP can include:
- Slow convergence times: Traditional STP can take some time to recover from topology changes. RSTP is a much faster alternative.
- Misconfigurations: Incorrect bridge priorities may disrupt the flow of traffic across the network.
- BPDU attacks: Malicious users may spoof BPDUs to modify network topology remotely. BPDU protection or guard technologies can defend against this.
Further reading
- Internet infrastructure: What it is and how it works
- How to change your location: VPNs, proxies, and Tor

