Expressvpn Glossary
Security policy
What is a security policy?
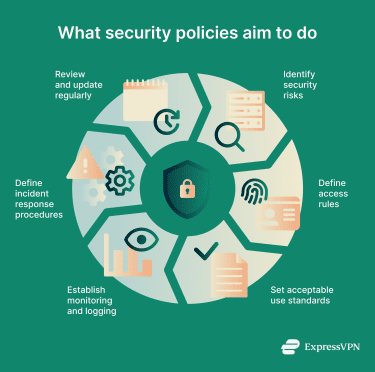
A security policy is an organization's documented set of rules that defines how it manages, protects, and shares information and technology resources. It dictates who can access what, how information is handled, and how security events are reported and escalated.
At its core, a security policy sets clear expectations for the safe and responsible use of technology.
What a security policy typically includes
 Security policy documents can be quite comprehensive, covering a wide array of topics. Common subjects include:
Security policy documents can be quite comprehensive, covering a wide array of topics. Common subjects include:
- Scope and ownership: What the policy covers, who approves/maintains it, and who it applies to.
- Access rules: Who can use systems, networks, and data, and under what conditions.
- Authentication requirements: How users prove their identity, such as through passwords and multi-factor authentication (MFA).
- Acceptable use standards: How company devices, software, and accounts may be used.
- Data protection requirements: How sensitive or confidential information should be handled and stored.
- Monitoring and logging: How system activity is tracked to detect misuse or threats, often paired with user notice and compliance requirements.
- Incident response: How potential security issues are reported and who is responsible for responding.
- Compliance references: How the policy aligns with legal, regulatory, and contractual requirements.
- Enforcement and exceptions: Consequences for noncompliance and how exceptions are requested/approved.
Types of security policies
Security policies usually fall into three broad categories:
- Administrative (organizational) policies: Cover the people and processes behind security. They define roles and responsibilities, describe how training is handled, and explain how incidents should be reported and managed.
- Technical (architecture) policies: Focus on how systems and software are protected. This includes areas like encryption standards, firewall rules, network security settings, and access controls.
- Physical (environment) policies: Protect physical assets such as offices, servers, and devices. These often include badge access, video surveillance, and rules for securing laptops and other equipment.
Why security policies matter
Security policies play a central role in protecting modern organizations. Specifically, they support:
- Clearer expectations: Transparent policies provide employees with clear guidance on handling and safeguarding sensitive information.
- Reduced risk: Consistent requirements lower the chance of mistakes or unsafe behavior.
- Lower breach likelihood: Defined access and acceptable-use standards can reduce the risk of unauthorized access, especially when enforced with appropriate controls.
- Improved compliance: Policies can support meeting legal, regulatory, and contractual requirements, but compliance depends on implementation and evidence.
- Faster response and recovery: Clear incident-response roles and requirements help speed up incident handling.
Common security policy examples
Organizations often maintain several policies that address specific areas of concern. Common examples include:
- Password policy: Sets requirements for creating, using, and managing passwords.
- Data protection policy: Defines how sensitive information should be classified, stored, shared, and retained.
- Acceptable use policy (AUP): Explains how company systems, accounts, and data may be used.
- Email and communication policy: Covers the safe use of email and messaging tools.
- Network security policy: Governs how networks are accessed and protected.
- Remote work or bring your own device (BYOD) policy: Defines requirements for personal or remote devices connecting to company systems.
- Incident response policy: Outlines how security issues should be reported and handled.
Security risks when policies are missing or ignored
When security policies are weak or not enforced, organizations face greater exposure to threats. Weak passwords, unsafe device use, and mishandled data can increase the risk of unauthorized access, malware infections, and data exposure.
Without clear rules and defined responsibilities, responses to security incidents may be inconsistent, raising the risk of missed obligations, regulatory consequences, and financial loss. Gaps in access governance and user activity monitoring can also increase insider risk.
Further reading
- VPNs, firewalls, endpoint security: What does your team really need?
- The 7 pillars of zero-trust security
- What is cybersecurity? A simple guide for beginners


