Expressvpn Glossary
Security assessment
What is a security assessment?
A security assessment is a systematic review of an organization's security posture and risks. Organizations conduct security assessments to identify gaps, vulnerabilities, and threats to their cybersecurity.
In practice, the terms "audit" and "assessment" are sometimes used interchangeably. However, a useful distinction is that audits tend to be more formal and criteria-based (often to provide assurance that requirements are being met), while assessments are typically improvement- and risk-focused, with a scope that can range from a single system to an organization-wide review.
Security assessments can involve various activities, such as penetration testing, vulnerability scanning, control reviews, compliance or framework-based evaluations, cloud configuration reviews, and more.
The outcome of a security assessment is usually a report documenting findings, associated risks, and prioritized recommendations to remediate weaknesses.
See also: Security monitoring, security audit, security policy
How does a security assessment work?
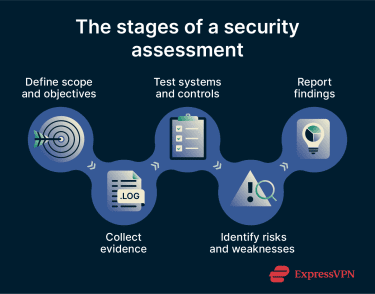 Most security assessments broadly follow these steps:
Most security assessments broadly follow these steps:
- Define scope and objectives: Decide what to assess and the goals of the assessment. Assessments may focus on one or more areas, such as a new payment processing system or alignment with specific security program standards, like International Organization for Standardization (ISO) / International Electrotechnical Commission (IEC) 27001 or a control assessment approach such as the National Institute of Standards and Technology (NIST) SP 800-53A.
- Review systems and evidence: Review architecture and documentation, configurations, logs, and other artifacts for misconfigurations, suspicious activity, and known weaknesses. Document what will be tested and what evidence will be collected.
- Evaluate existing security controls: Choose and conduct activities to test the system’s security controls and identify vulnerabilities or security gaps. Security teams may rely on well-established frameworks or assessment methods to guide the review.
- Analyze and prioritize risk: Connect findings to likely threat scenarios and business impact, then prioritize remediation based on risk and feasibility.
- Report findings: Produce a report that summarizes strengths and weaknesses, documents evidence-based findings, and provides a prioritized remediation roadmap to reduce risk and improve security maturity.
Types of security assessments
A single security assessment may involve one or more of the following activities:
- Vulnerability assessment and scanning: Typically involves using automated tools to scan systems for known vulnerabilities, insecure configurations, exposed services, or missing patches. The main aim is to uncover weaknesses that bad actors may exploit.
- Penetration testing: A form of ethical hacking in which teams carry out authorized, simulated attacks within a defined scope to assess an organization’s defenses. It may uncover hidden vulnerabilities or logic flaws that could enable unauthorized access.
- Risk assessment and threat modeling: Many security assessments include a risk assessment, which seeks to identify, analyze, and prioritize risks. This analyzes the likelihood of certain incidents occurring and their potential financial, reputational, or operational impact.
- Compliance audits: Evaluate an organization's adherence to specific regulations or industry requirements. For example, whether data handling aligns with the General Data Protection Regulation (GDPR) or payment processing aligns with the Payment Card Industry Data Security Standard (PCI DSS).
- Cloud, app, or network reviews: Target specific IT systems, such as enterprise software, end-user applications, and local or cloud networks. Organizations may assess whether security controls are enabled and properly configured, whether updates are effectively managed, and whether authentication occurs securely.
Why is a security assessment important?
Security assessments are important because they are structured processes that help organizations understand their overall security readiness, posture, and risk exposure within a defined scope:
- Improving visibility: Provides a clear snapshot of security strengths, weaknesses, and gaps across the assessed system and environments.
- Supporting decision-making: Enables leaders to make informed strategic decisions grounded in evidence rather than assumptions.
- Benchmarking security maturity: Allows organizations to track progress and measure improvements across assessments performed at regular intervals.
- Demonstrating accountability and building trust: Supports by documenting findings and remediation progress to show that security expectations (regulatory, contractual, and customer) are being addressed for partners and stakeholders.
- Prioritizing remediation: Directs security teams to use resources more efficiently by focusing their efforts on the most important changes first.
- Strengthening preparedness and incident response: Can inform improvements to detection, response, and recovery capabilities to reduce disruption and losses.
Where is it used?
Security assessments are often useful as part of due diligence efforts, especially when organizational changes occur:
- Before launching new systems to production: Identify security weaknesses in new software, hardware, or services before exposure to the public or third parties.
- When onboarding vendors: Assess whether third-party vendors meet the organization’s security expectations and help manage third-party and supply chain risk.
- During mergers and acquisitions: Evaluate the security posture and risks of another organization before completing acquisitions, partnerships, or major investments.
- After incidents or major changes: Support post-incident analysis and reassessment following breaches, system migrations, architecture changes, or policy updates.
- Security programs and governance: Support ongoing security oversight by validating controls, tracking remediation, and informing continuous improvement efforts.
Further reading:
- What is security posture? A complete guide for organizations
- Zero-trust architecture: What it is, how it works, and why it matters
- What is cybersecurity? A simple guide for beginners
- Why software security audits matter

