Expressvpn Glossary
Post-quantum cryptography
What is post-quantum cryptography?
Post-quantum cryptography (PQC) is a type of cryptography designed to remain secure in a future with powerful quantum computers. It refers to new public-key methods and digital-signature algorithms, intended to replace today’s widely used public-key algorithms, which could become unsafe against quantum attacks.
See also: Public key encryption, quantum cryptography, TLS handshake
Why post-quantum cryptography matters
The following factors contribute to the importance of PQC:
- Quantum threats: Large-scale quantum computers may be able to break widely used public-key encryption and signature schemes. Sensitive data encrypted and stored today could be decrypted later (“harvest now, decrypt later”), creating long-term privacy and security exposure.
- Long-term privacy and resilience: PQC helps preserve confidentiality and trustworthy authentication over long time horizons, including for data and systems that must remain secure for many years.
- Ongoing transition and infrastructure protection: Governments and organizations are beginning large-scale transitions as standards finalize and adoption grows. Migration takes years, and PQC helps protect communications, identity systems, and critical digital infrastructure as cryptography is upgraded.
How post-quantum cryptography works
PQC uses mathematical problems believed to be resistant to attacks by large-scale quantum computers. Common approaches include lattice-based schemes (used for key establishment and some digital signatures) and hash-based schemes for digital signatures.
These algorithms are designed to replace or complement current public-key systems. During migration, they are often deployed in hybrid key-establishment designs that combine a post-quantum algorithm with a classical algorithm to reduce transition risk. They're also intended to work with existing network protocols, which can negotiate supported algorithm suites, though deployments may require updates and accommodations for larger keys or messages to maintain interoperability.
The National Institute of Standards and Technology (NIST) has published its first PQC standards. They include the Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM) for key establishment. ML-KEM was originally submitted as CRYSTALS-Kyber. They also include the Module-Lattice-Based Digital Signature Algorithm (ML-DSA) for digital signatures. ML-DSA was originally submitted as CRYSTALS-Dilithium. NIST also standardized the Stateless Hash-Based Digital Signature Algorithm (SLH-DSA) from SPHINCS+. SLH-DSA is a hash-based digital signature scheme.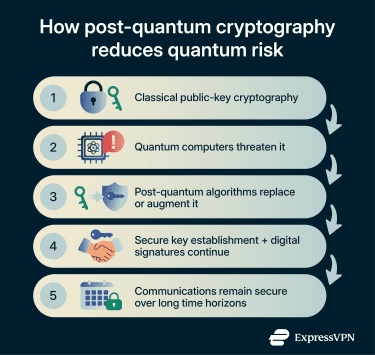
Key features of quantum-resistant algorithms
Quantum-resistant algorithms are designed for:
- High computational difficulty: Based on problems believed to be hard for both classical and quantum computers, with no efficient attacks currently known at standard security levels.
- Quantum resilience: Designed to avoid the weaknesses exploited by major quantum algorithms, including Shor’s algorithm, which threatens Rivest-Shamir-Adleman (RSA) and many elliptic-curve systems, and, where relevant, Grover’s algorithm (which can reduce the effective security margin of some symmetric and hash-based constructions).
- Functional coverage: Provide the core public-key functions required in modern systems, primarily key establishment and digital signatures.
- Different structures and larger keys: Use different mathematical foundations than RSA or elliptic curve cryptography (ECC), commonly relying on structures such as lattices or hash-based constructions, and often requiring larger key, ciphertext, or signature sizes than traditional public-key schemes.
Post-quantum cryptography vs. classical cryptography
| Classical public-key cryptography | Post-quantum cryptography | |
| Algorithms in scope | RSA, ECC, Diffie–Hellman | Lattice-based and hash-based schemes (among others) |
| Quantum exposure | Vulnerable to large-scale quantum attacks against public-key methods | Intended to resist known quantum attacks targeting public-key cryptography |
| Deployment maturity | Widely deployed and highly interoperable across systems | Adoption is ongoing; rollout differs by ecosystem and vendor |
| Operational impact | Typically, smaller keys/messages and predictable performance | Some algorithms use larger keys/messages and can have different performance and compatibility across devices and software stacks |
Challenges and limitations of post-quantum cryptography
- Larger keys and messages: Some post-quantum schemes use larger public keys, ciphertexts, or signatures, which can increase bandwidth, storage, and handshake/certificate sizes.
- Performance and platform variation: Speed and memory use can differ across servers, desktops, mobile devices, and constrained hardware. Implementation choices can significantly affect latency and resource consumption.
- Evolving standards and ecosystems: Core standards exist, but guidance continues to develop, and supporting software libraries, protocol profiles, and compliance requirements may change as adoption expands.
- Migration and operational risk: Transitions must be carefully managed to avoid introducing vulnerabilities, such as misconfiguration, inconsistent algorithm support across systems, or weak integration during staged rollouts.
Further reading
- What is post-quantum cryptography?
- What is quantum-resistant encryption?
- Quantum VPN: What it is and why it matters
- What is quantum cryptography?


