Expressvpn Glossary
PGP encryption
What is PGP encryption?
Pretty Good Privacy (PGP) is a type of encryption that secures data so that only the intended recipient can read it. It uses a public-key model, where data is encrypted with a public key and decrypted with a matching private key. This lets information be exchanged safely even when the communication channel isn’t trusted.
PGP encryption is most commonly used for email, but the same method can also protect files, verify software, or safeguard archives.
How does PGP encryption work?
PGP encryption is designed to protect data while allowing access to be controlled. To do this effectively, it uses hybrid encryption: a combination of symmetric and asymmetric encryption.
Symmetric encryption
Symmetric encryption uses a single secret key that’s shared to encrypt and decrypt data. It’s fast and efficient, making it suitable for protecting the contents of messages, files, and attachments. However, it can be compromised if the shared key falls into the wrong hands.
Asymmetric encryption
Asymmetric encryption uses a pair of mathematically linked keys (one public, one private) generated by the recipient. The sender uses the recipient’s public key to encrypt data before sending. This data can only be decrypted by the recipient’s private key, making sure that it can’t be intercepted on the way.
The keys used in asymmetric encryption are much larger. This means they’re more secure, but it also makes the method inefficient at encrypting large amounts of data because it’s slower than symmetric encryption. That’s why PGP uses a mix of the two.
PGP encryption: Step-by-step example
 When an email protected by PGP is composed, the sender’s PGP software generates a one-time session key and uses it to encrypt the email contents. This step encrypts the data itself and is handled symmetrically so large amounts of information can be encrypted efficiently.
When an email protected by PGP is composed, the sender’s PGP software generates a one-time session key and uses it to encrypt the email contents. This step encrypts the data itself and is handled symmetrically so large amounts of information can be encrypted efficiently.
Because anyone who obtains the session key could read the email, PGP then protects the session key using asymmetric encryption. The session key is encrypted with the recipient’s public key, which is then sent alongside the encrypted email.
When the email arrives, the recipient’s PGP software uses its private key to recover the session key and then uses that session key to decrypt the email contents.
PGP can also apply a digital signature. The sender creates the signature using their own private key, and the recipient verifies it using the sender’s public key. If the message is altered after signing, the verification check fails, allowing the recipient to detect tampering.
Why is PGP encryption important?
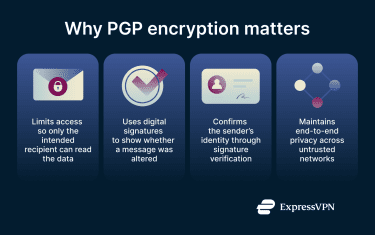 PGP offers several benefits that strengthen the privacy and reliability of digital communication:
PGP offers several benefits that strengthen the privacy and reliability of digital communication:
- Access control and confidentiality: Only the intended recipient can decrypt the protected content, whether it’s stored or transmitted. This makes PGP suitable for communication that requires strong end-to-end privacy.
- Message integrity: Digital signatures help recipients confirm that the message hasn’t been modified after it was sent.
- Sender authenticity: Signatures also verify who wrote the message, reducing the risk of impersonation or forged communication.
Security and privacy considerations
PGP is effective when the keys and software that support it are handled carefully. Several factors can influence how secure PGP-encrypted emails and files are:
- Private key protection: Anyone who obtains a private key can read emails and access files that have been encrypted with that key. It must stay on a trusted device and be secured with a strong password.
- Software integrity: PGP tools should be kept up to date to ensure they use current algorithms and aren’t exposed to known vulnerabilities.
- Key verification: Public keys should be confirmed through a trusted source before they’re used, since an attacker could try to distribute a fake key to intercept messages.
- Secure backups: Because encrypted messages can’t be recovered without the matching private key, the key should be backed up in a protected place. This could be an offline storage device or another secure environment that only the user can access.
- Device security: Even strong encryption can’t protect data on a compromised device. Malware can capture plaintext before it’s encrypted or after it’s decrypted. Devices hosting sensitive data should be kept up to date and be sufficiently secured against malware.
Further reading
- What is data encryption?
- End-to-end encryption: What it is and why it matters
- Zero-trust data protection explained
FAQ
Is PGP still secure today?
What’s the difference between PGP and GPG?
In practice, when people refer to using “PGP encryption,” they are often using GPG or a similar compatible tool behind the scenes.


