Expressvpn Glossary
Perimeter security
What is perimeter security?
Perimeter security is the set of technologies, policies, and controls used to protect the boundary between an internal network and external networks, such as the internet. It acts as a first filter that reduces the volume of threats that reach internal systems.
How does perimeter security work?
Perimeter security works by inspecting and filtering traffic at the edge of a network. When data packets attempt to enter or leave the protected environment, security controls evaluate them against predefined rules and policies. Traffic that meets the criteria is allowed through; traffic that does not is blocked or flagged.
This inspection can happen at different levels, from basic packet filtering based on IP addresses and ports to deeper content inspection that analyzes the actual payload of traffic. Authentication mechanisms may also be applied to verify the identity of users or devices before granting access.
Common perimeter security tools
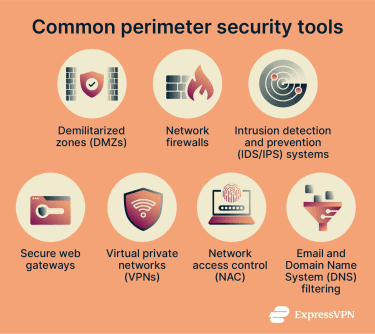 Network perimeter security is typically implemented through several categories of boundary protection that control access between internal networks and external environments:
Network perimeter security is typically implemented through several categories of boundary protection that control access between internal networks and external environments:
- Demilitarized zones (DMZs): Isolated network segments placed between external and internal networks to host public-facing services while limiting direct access to internal systems.
- Network firewalls: Filter inbound and outbound traffic according to defined security policies at network entry and exit points.
- Intrusion detection and prevention (IDS/IPS) systems: Monitor network traffic for known attack patterns or abnormal behavior and generate alerts or automatically block threats.
- Secure web gateways: Inspect web traffic moving between internal users and the internet to prevent access to malicious or unsafe content.
- Virtual private networks (VPNs): Provide encrypted connections and authenticated access for remote users or external networks connecting to internal resources.
- Network access control (NAC): Restricts network access based on device identity, authentication status, or security posture before allowing connections through the network.
- Email and Domain Name System (DNS) filtering: Detect and block malicious domains, phishing attempts, or harmful communications before they reach internal systems.
How is perimeter security applied in different environments?
In corporate networks and data centers, perimeter security typically involves dedicated hardware appliances deployed at network gateways to monitor and control traffic. Large organizations may also segment their internal networks into zones with separate perimeters that limit lateral movement in the event of a breach.
In cloud environments, perimeter security is implemented through virtual network controls such as security groups, network access control lists (ACLs), and web application firewalls (WAFs). For remote work scenarios, VPNs typically extend the perimeter to cover devices outside the physical office.
Risks and privacy concerns
Perimeter security introduces certain operational and privacy considerations:
- Reduced effectiveness in modern environments: Cloud services, remote access, and mobile devices can extend activity beyond traditional network boundaries.
- Configuration risks: Misconfigured firewalls or access rules may expose services or allow unauthorized connections.
- Privacy considerations: Traffic inspection and logging may involve processing sensitive or personal data.
- Perimeter bypass: Threats may enter through compromised credentials or trusted connections that pass perimeter checks.
Further reading
- Zero-trust architecture: What is it, how it works, and why it matters
- Deep packet inspection (DPI): How it works and why it matters
- VPN vs. firewall: Key differences and when to use each
- VPNs, firewalls, endpoint security: What does your team really need?


