Expressvpn Glossary
Password spraying
What is password spraying
Password spraying is a credential-based attack where cybercriminals try a few common passwords against many accounts at once. Spreading entry attempts in this manner helps the attacker avoid account lockouts that could alert users to the malicious activity.
How password spraying works
Typically, password spraying is a cycle of account discovery and controlled login attempts:
- Acquire usernames: Attackers construct usernames from employee lists and naming formats, or enumerate them from Active Directory (a widely used directory service that supports authentication and authorization) and domain controllers.
- Select passwords: This technique targets weak, popular passwords that are used in most environments. Attackers may look to public password wordlists, which list commonly used passwords. Sometimes, attackers tailor passwords to the target by incorporating their company name or personal interests.
- Run a spraying round: Attackers attempt one or a few common passwords across a large set of usernames, limiting their entry attempts to stay under account lockout thresholds.
From here, the process repeats over time. If a login attempt is successful, attackers take control of the account and its privileges. Accounts that aren’t successfully breached can be targeted again in a future spray attack after some time has passed, once lockouts are no longer a concern.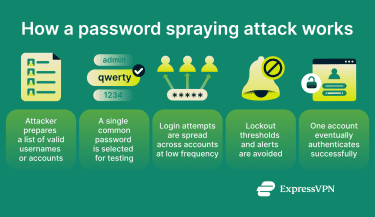
Why attackers use password spraying
Attackers may favor password spraying as they can carry it out using commonly available tools. It doesn’t require a sophisticated strategy or advanced technical expertise. Here are some more reasons why they may choose it over other credential-based attacks:
- Lower effort per target: The technique targets many users, allowing attackers to minimize the time and effort spent on each account.
- Effective at large scale: Password spraying works well against large volumes of usernames. For this reason, it’s suitable for environments with many accounts, like large organizational networks.
- Reduces detection risk: Attackers can limit their entry attempts, spreading them over time to stay below detection thresholds.
Common targets of password spraying
Attackers typically target authentication systems with large numbers of user accounts, including:
- Email accounts: Email is often tied to password resets for other accounts, making it a high-value target.
- Corporate and cloud login portals: These serve as centralized entry points to many user accounts and internal resources.
- Virtual private network (VPN) gateways: Corporate VPN services can serve as authentication entry points, giving users access to internal networks.
- Single sign-on (SSO) services: A single successful SSO login can grant access to multiple connected applications and services.
- Social media accounts: These platforms hold large numbers of personal and business accounts behind password-based logins.
How password spraying attacks can be prevented
Password spraying attacks depend on the use of common passwords. Strong and unique passwords, such as those generated with password managers, significantly reduce the risk of a successful password spraying attack. Multi-factor authentication (MFA) can further prevent attackers from gaining entry to an account by requiring two or more forms of authentication. Even if attackers guess the right password, they may still be unable to breach the account.
Password spraying vs. other credential attacks
Brute force attacks
Brute force attacks target a single account and involve repeatedly trying many different passwords until one works. Unlike password spraying, this generates repeated failed logins on one account, making lockouts likely. Attackers may use this method when they're after a specific high-value account and suspect the password is easy to guess.
Credential stuffing
Credential stuffing uses username and password pairs leaked in data breaches, distinguishing it from password spraying where attackers guess passwords by using commonly used words and combinations. It tests them against popular online services through automated, large-scale login attempts. The attack targets users who reuse the same password across multiple accounts.
Risks and impact of password spraying
- Account takeover: Attackers can fully take over accounts by changing the credentials, locking out legitimate users.
- Data theft: Compromised accounts can give attackers access to email content, contact information, and other sensitive data.
- Lateral movement: Attackers may use the compromised account to reach other systems. For example, they might be able to access internal networks or cloud infrastructure.
Further reading
- The best way to store your passwords securely
- How do hackers get passwords? Tips to stay safe
- Cybersecurity lessons: Privilege escalation via file read/write


