Expressvpn Glossary
One-time password (OTP)
What is a one-time password?
A one-time password (OTP) is a temporary system-generated code that’s intended to be used just once during a login or transaction attempt. It provides an extra layer of security by making the login or transaction unique and short-lived.
How does a one-time password work?
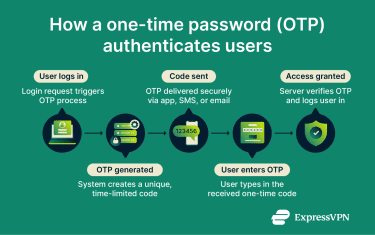 In a login or transaction that requires an OTP, the system creates a random code, either alphanumeric or numeric, and sends it to the user via a separate channel from where the login or transaction is taking place, such as an authentication app, hardware token, email, or SMS. The code can then be used as a form of authentication; upon entry, the server checks that the code matches what was generated and that it hasn’t expired. If all checks pass, the system approves the login or transaction.
In a login or transaction that requires an OTP, the system creates a random code, either alphanumeric or numeric, and sends it to the user via a separate channel from where the login or transaction is taking place, such as an authentication app, hardware token, email, or SMS. The code can then be used as a form of authentication; upon entry, the server checks that the code matches what was generated and that it hasn’t expired. If all checks pass, the system approves the login or transaction.
Types of one-time passwords
- Time-based OTP (TOTP): This code uses a clock-based system and changes at predetermined intervals, usually every minute or less. The user and the system share a secret key and a timer; the system verifies the user’s identity when they enter the code within the allotted time.
- Hash Message Authentication Code-based OTP (HOTP): Here, the system and the authentication device share a secret key and keep a counter value. Each time a new code is needed, the counter goes up by one on the device, and the device uses the secret key and the new counter value to generate a short numeric code.
- Hardware token OTP: A dedicated physical device (like a small key fob or USB token) generates an OTP (either time-based or counter-based) that can be entered manually.
Why are one-time passwords important?
OTPs are essential for preventing unauthorized access to sensitive accounts and blocking fraudulent transactions. Even if a threat actor steals or guesses a user’s password, they still need the single-use code that is received separately. This extra step can prevent many attacks.
OTPs can also help organizations comply with security and privacy regulations that require multi-factor authentication (MFA).
OTP vs. static passwords
Static passwords remain the same for every login instance, which makes it easy for attackers to reuse and exploit them when they are compromised. In contrast, OTPs are session-specific and have a short expiration time, so even if someone intercepts them, they can’t reuse the code for future access.
Security and privacy considerations
- SMS-based OTPs are less secure: Hackers can use techniques like SIM swapping to intercept or compromise text communications containing OTP codes.
- App-based or hardware tokens offer increased security: These reduce vulnerability to network-based attacks by generating codes locally rather than through the internet, SMS, or email.
- Network security measures can help prevent OTP interception: Virtual private networks (VPNs) and other forms of traffic encryption can help prevent OTPs sent over the internet from interception on insecure networks.
Common OTP use cases
- Accessing online banking accounts: Banks usually require OTPs to verify users’ identities and prevent fraudulent access to accounts.
- Authorizing financial transactions: When a transfer or payment is initiated, apps or websites may request an OTP to validate the action.
- Connecting to secure business networks: To help ensure that only authorized individuals have access to a company’s network, organizations can require users to enter an OTP when logging in remotely or from a new device.
- Verifying new device logins and password resets: If a user signs into an app or website on a new device or requests a password change for their account, OTP verification can be enforced to confirm their identity.
Further reading
- What is two-factor authentication (2FA), and how to set it up securely
- 2FA vs MFA: Key differences and how to choose the right one
- What is phishing-resistant MFA, and why does it matter?


