Expressvpn Glossary
Homomorphic encryption
What is homomorphic encryption?
Homomorphic encryption is a cryptographic method that allows computations to be performed on encrypted data without revealing the underlying plaintext. The system processes ciphertext directly and produces an encrypted result that can be decrypted only by the data owner.
The core purpose is to preserve data confidentiality during processing, not only during transmission or storage.
How does homomorphic encryption work?
The process begins when data is encrypted with an encryption key, producing ciphertext that other systems can process but not interpret.
The ciphertext can then be sent to a third-party environment, such as a cloud platform or analytical service. An evaluation function performs allowed operations (such as addition, multiplication, or a supported combination of both) directly on the encrypted data.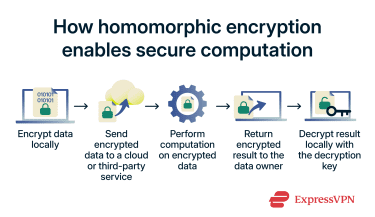 The result is a new ciphertext. When it is decrypted with the corresponding decryption key, the output matches the result that would have been obtained if the same computation had been applied to the original unencrypted data.
The result is a new ciphertext. When it is decrypted with the corresponding decryption key, the output matches the result that would have been obtained if the same computation had been applied to the original unencrypted data.
Types of homomorphic encryption
Homomorphic encryption is commonly classified by the range and depth of operations it supports on encrypted data.
- Partially homomorphic encryption (PHE): Supports a single type of mathematical operation on encrypted data, such as only addition or only multiplication. The chosen operation can be applied an unlimited number of times, which makes PHE suitable when computations follow a fixed pattern.
- Somewhat homomorphic encryption (SHE): Supports both addition and multiplication on encrypted data, but only for a limited number or depth of operations before the ciphertext becomes too noisy to use. It offers more flexibility than PHE while remaining more efficient than fully homomorphic schemes.
- Fully homomorphic encryption (FHE): Supports arbitrary combinations of additions and multiplications on encrypted data, allowing evaluation of general computations that could be performed on plaintext. It provides the greatest flexibility but typically requires significantly more computational resources than PHE or SHE.
Why is homomorphic encryption important?
Homomorphic encryption allows organizations to use external or untrusted computing environments, such as cloud platforms, for processing sensitive data while maintaining confidentiality. This supports secure data sharing and helps meet privacy and regulatory requirements in sectors like healthcare, finance, and government.
By limiting visibility into raw data on processing systems, it also reduces the impact of insider threats and server compromise.
FHE is increasingly discussed for large language models (LLMs) because, unlike end-to-end encrypted messaging (where providers cannot access message contents), LLMs typically require plaintext to process prompts, meaning providers can see conversations.
FHE may enable LLM computations to run directly on encrypted inputs without decrypting them first. As a result, FHE combined with machine learning has become a major area of research, with the goal of reducing privacy, security, and compliance exposure in LLM workflows.
Common use cases
Homomorphic encryption is most often used in scenarios where sensitive data must remain confidential during processing, including:
- Secure cloud data processing: Enables cloud services to analyze or transform encrypted datasets without accessing plaintext.
- Privacy-preserving analytics in regulated industries: Supports analysis of medical, financial, or insurance records while keeping underlying data confidential.
- Encrypted machine-learning workflows: Allow model training or inference on encrypted inputs, reducing exposure of underlying data in AI pipelines.
- Collaborative research on sensitive datasets: Permits organizations to combine or study confidential information without sharing readable records.
- Government and defense environment: Protects classified or sensitive records when computation is outsourced or distributed across systems.
Security and privacy considerations
Homomorphic encryption provides confidentiality while data is being processed, but overall security depends on correct implementation and careful parameter selection. Many practical schemes rely on lattice-based cryptography, such as Learning With Errors (LWE), which is widely believed to offer resistance to known classical and quantum attacks when appropriate parameters are used.
Key management remains critical because only holders of the decryption key can recover processed results. If private keys are lost, access to encrypted outputs may be permanently unavailable; if they are compromised, confidentiality is lost.
Homomorphic encryption also does not eliminate all privacy risks, as metadata about computations, system-level logging, and access-control configurations can still reveal patterns of use or operational details.
Further reading
- The history of encryption
- End-to-end encryption: what it is and why it matters
- Zero-trust data protection explained
FAQ
What is the main advantage of homomorphic encryption?
What’s the difference between full and partial homomorphic encryption?
Is homomorphic encryption used in cloud computing?
How does homomorphic encryption relate to VPNs?
A VPN, by contrast, encrypts data in transit between endpoints but typically decrypts it at the server, which then sees plaintext. The two can be combined, with a VPN protecting network traffic and homomorphic encryption protecting the data during computation.


