Expressvpn Glossary
File integrity monitoring
What is file integrity monitoring?
File integrity monitoring (FIM) is a cybersecurity process that detects and flags unauthorized or unexpected changes to files and system settings. It typically monitors critical operating system files, application binaries, and configuration items by comparing current states against a known-good baseline and reporting deviations.
It matters because it helps identify tampering, misconfigurations, and indicators of compromise that can affect system security and reliability.
How does file integrity monitoring work?
FIM starts by establishing a trusted baseline that records the approved state of selected files. The baseline typically includes cryptographic hashes and key metadata such as ownership, permissions, and modification details.
The system then watches those files and other monitored items for changes. When a change is detected, the current file state is compared to the baseline or policy rules. If the change is unexpected or not recognized as an approved update, the tool generates an alert and logs details such as what changed, when it changed, and, where supported, the account or process associated with the change.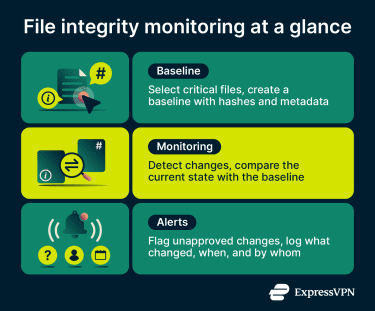
Types of file integrity monitoring
Several approaches are used for FIM:
- Agent-based monitoring: Installs software on servers or endpoints to monitor selected files, registries, or configurations locally and report changes.
- Agentless monitoring: Monitors systems without installing software on the monitored workload, often using remote inspection, platform APIs, or cloud-integrated scanning to identify changes.
- Real-time monitoring: Detects changes as they occur, often using operating system–level event sources (for example, kernel mechanisms) to capture file events immediately or near real time.
- Scheduled scanning: Checks file state at set intervals, which can reduce system impact but may delay detection between scan windows.
- Cloud-native FIM: Monitors cloud workloads and assets, such as containers and Infrastructure-as-Code (IaC) templates, using cloud platform integrations, APIs, and runtime controls.
These categories can overlap, since some tools support multiple approaches depending on the environment and deployment model.
Why is file integrity monitoring important?
FIM is important because unexpected changes to files or configurations can indicate malware, unauthorized access, or attempts to disable security controls. Without monitoring, these changes may be harder to detect quickly.
It improves visibility by detecting and recording changes to critical systems, helping teams identify suspicious activity more quickly and confirm that approved security settings remain in place after patching or hardening.
FIM also helps create a record of what changed, when it changed, and which account was linked to the change. This supports incident investigation, compliance reporting, and change reviews that can inform broader least-privilege and access-control efforts.
Where is file integrity monitoring used?
Organizations deploy FIM across systems where unauthorized changes create security, availability, or compliance risk, including:
- Compliance-regulated environments: Systems subject to requirements under frameworks and laws such as the General Data Protection Regulation (GDPR), the Payment Card Industry Data Security Standard (PCI DSS), the Health Insurance Portability and Accountability Act (HIPAA), or the Sarbanes-Oxley Act (SOX), where organizations may use FIM to support integrity, audit, and change-monitoring requirements.
- Web servers and content management systems: Platforms that depend on stable configuration files and application components.
- Servers and endpoints: Critical infrastructure such as domain controllers and production systems.
- Cloud workloads: Virtual machines, cloud-hosted servers, and other monitored workloads, where configuration drift or unauthorized file changes can affect security and deployments.
- Network appliances: Devices such as firewalls and virtual private network (VPN) gateways, where configuration changes can directly affect security controls.
Risks and privacy concerns
Legitimate updates can be flagged as suspicious if baselines and approved-change processes are unclear. In environments with frequent patching or automated deployments, this can create too many alerts and make real issues harder to spot.
FIM can also create privacy and data-handling risks because logs and integrity records may contain sensitive filenames, paths, hashes, or metadata such as ownership and permissions, and, in some implementations, additional change details. These risks increase if the data is stored or transmitted insecurely.
Noise reduction can introduce blind spots. If exclusions are overly broad, important files or directories may no longer be monitored, allowing unauthorized changes to go undetected.
Logging practices also matter. Incomplete records, inconsistent timestamps, or short retention periods can weaken investigations and compliance reporting. On limited systems, high log volume can also increase storage and performance pressure.
Further reading
- What is threatware? A complete guide to risks and protection
- What is ransomware? How it works and how to prevent attacks
- Supply chain attack: How it works and how to stay protected
- What is a rootkit, and why is it so dangerous?
- Fileless malware: What it is and how to stop it

