Expressvpn Glossary
Cloud security posture management (CSPM)
What is cloud security posture management (CSPM)?
Cloud security posture management (CSPM) is a set of tools and practices designed to identify, monitor, and remediate security risks in cloud environments, including hybrid and multi-cloud environments. It helps organizations maintain visibility and control over cloud configurations across different cloud models as environments scale and change.
How CSPM works
CSPM combines automated tools with defined security practices to continuously assess and manage cloud configuration risk. CSPM tools integrate with cloud service providers to collect configuration and metadata from cloud resources and evaluate it.
CSPM practices then define how these findings are handled. They include establishing approved configuration standards, assigning ownership for remediation, prioritizing risks based on impact, and tracking posture improvements over time. These practices ensure findings are consistently reviewed and resolved rather than treated as one-off alerts.
Common cloud risks CSPM detects
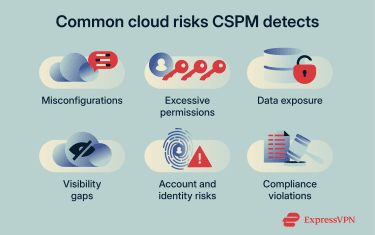 CSPM is commonly used to detect:
CSPM is commonly used to detect:
- Misconfigurations: Incorrect or insecure cloud resource settings, such as public storage access or disabled encryption.
- Excessive permissions: Identity or service roles granted broader access than necessary.
- Data exposure: Cloud data stores that are unintentionally accessible from the internet or unauthorized networks.
- Visibility gaps: Untracked cloud assets, unclear ownership, or unmanaged configurations.
- Account and identity risks: Suspicious access activity, privilege escalation, or compromised credentials.
- Compliance violations: Cloud configurations that do not meet regulatory or internal policy requirements.
Benefits of using CSPM
CSPM continuously assesses cloud environments for configuration risks. It also supports regulatory compliance by evaluating cloud configurations against established standards such as the Health Insurance Portability and Accountability Act (HIPAA) and the Payment Card Industry Data Security Standard (PCI DSS).
By automating configuration checks, CSPM reduces the likelihood of human error during deployment and ongoing changes, and it strengthens access and identity management by highlighting opportunities to tighten permissions.
Limitations of CSPM
CSPM has several inherent limitations that define what it can and cannot address:
- Configuration-focused scope: Evaluates cloud configuration and control plane settings, not runtime threats or active attacks.
- Limited threat detection: Doesn’t detect malware, exploits, or suspicious workload behavior.
- Alert volume: Can generate large numbers of findings that require tuning and prioritization.
- Cloud-only coverage: Focuses on cloud environments and doesn’t protect on-premises infrastructure.
- Policy dependency: Effectiveness depends on the quality and relevance of defined security policies.
CSPM vs. other cloud security tools
CSPM usually works alongside other tools that address different layers of cloud security, including:
| Cloud security posture management
(CSPM) |
Cloud workload protection platform
(CWPP) |
Cloud access security broker
(CASB) |
Cloud infrastructure entitlement management
(CIEM) |
|
| Purpose | Evaluates cloud configuration and posture against security and compliance standards | Protects cloud workloads at runtime | Enforces security policies for user access to cloud services | Analyzes and manages cloud identities and permissions |
| Types of risks it identifies | Misconfigs, public exposure, policy, and compliance violations | Malware, exploits, unauthorized processes, and lateral movement | Shadow IT, risky application usage, data exposure, and anomalous user behavior | Over-privileged roles, unused identities, excessive entitlements |
Further reading
- Security concerns in cloud computing and how to address them
- Zero-trust cloud security explained
- IoT cloud security: Threats and best practices
- Is cloud gaming safe? Security and privacy tips


