Expressvpn Glossary
Broken access control
What is broken access control?
Broken access control is a security vulnerability in which an application fails to correctly enforce authorization, which results in allowing users to access data or perform actions beyond their intended permissions.
How does broken access control happen?
Broken access control happens when authorization checks aren’t enforced at the point where actions are executed. This typically occurs when the server trusts data sent by the client, such as user IDs or role values stored in session tokens or cookies. If the server accepts these values without validation, an attacker can modify them to access other users’ data or gain additional privileges.
It can also happen when permission checks are enforced only in the user interface, applied inconsistently across services, or checked only at the start of a workflow. In these cases, attackers can bypass restrictions by directly calling backend API endpoints or altering request parameters.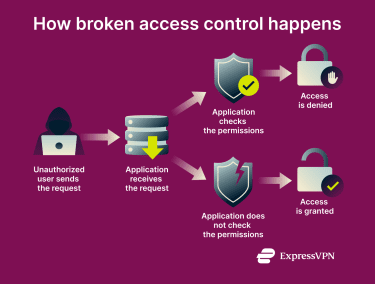
Where does broken access control occur?
Broken access control can surface in a variety of contexts, including:
- Web applications with role‑based features: Sites that assign roles (such as admin, editor, or viewer) depend on strong server‑side controls to ensure each user can only perform the actions they’re allowed to.
- Mobile apps that call backend APIs: Mobile applications typically talk to a server to fetch or update data. If the server trusts information sent by the client, attackers can manipulate requests and bypass authorization.
- Administrative panels and dashboards: Control interfaces for content management systems, IoT devices, and other tools may have hidden or poorly tested endpoints that could have been overlooked during development.
- Multi‑tenant SaaS environments: Software‑as‑a‑Service (SaaS) providers host multiple customers on shared infrastructure. Proper authorization is needed to keep each tenant’s data and permissions separate.
- Microservices and internal tools: Modern applications are frequently built from many small services that expose APIs. Inconsistent authorization logic across these services can lead to gaps that allow unauthorized access.
Risks and privacy concerns
Broken access control can result in unauthorized access to personal, financial, or confidential data belonging to other users or organizations. This exposure increases the risk of identity theft, financial abuse, and misuse of sensitive information.
From a privacy standpoint, such failures may violate data protection laws and contractual obligations by allowing data to be accessed outside its intended scope.
Further reading
- Why software security audits matter
- Cybersecurity tips for small businesses
- Security concerns in cloud computing
- How to implement zero trust

