Expressvpn Glossary
Block cipher
What is a block cipher?
A block cipher is a symmetric-key cryptographic algorithm that encrypts data in fixed-size blocks using a cryptographic key. Each block of plaintext is transformed into a ciphertext block of the same length. The encryption process is reversible, allowing decryption with the same key to recover the original data.
The purpose of a block cipher is to securely protect data by converting readable information into an encrypted form that prevents unauthorized access. It enables confidential communication and data integrity by allowing authorized parties to encrypt and decrypt information using a shared secret key.
How a block cipher works
In practice, block ciphers are applied to fixed-size blocks and combined with a mode of operation to handle longer inputs and produce the final ciphertext.
- Data is divided into blocks: The algorithm operates only on input blocks of a specific size and maps each block to a same-length output block, for example, 128-bit blocks for Advanced Encryption Standard (AES).
- A symmetric key is applied to each block: Each plaintext block is transformed under the secret key, producing a corresponding fixed-size ciphertext block.
- Encryption: Many standardized block ciphers use multiple rounds of transformations (for example, substitutions and permutations). AES is one example that uses repeated rounds with byte substitution and cyclic shifting, along with other mixing and key-addition steps.
- Blocks form the ciphertext: The encryption process converts plaintext blocks into ciphertext blocks, which together represent the encrypted output.
- Decryption: The decryption function is the inverse of the encryption function and restores the original plaintext when the correct secret key is used.
Common block cipher modes of operation
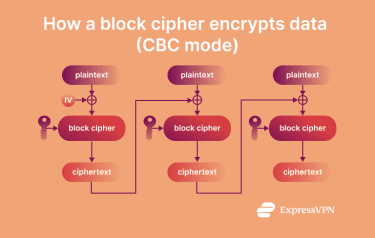
Block ciphers encrypt fixed-size blocks of data, but simply encrypting each block independently can leak patterns and weaken security. Different modes of operation were developed to address these issues while balancing security, performance, and practical requirements such as parallel processing. Some modes provide confidentiality only, while authenticated modes add integrity/authenticity.
- Electronic codebook (ECB): Encrypts each plaintext block independently, enabling parallel encryption and decryption of multiple blocks. However, if the data contains many identical blocks, it's possible to recover some information about the original plaintext because identical plaintext blocks produce identical ciphertext blocks.
- Cipher block chaining (CBC): An initialization vector (IV) is used for the first block and must be unpredictable (it doesn't need to be secret). CBC prevents pattern leakage by combining each plaintext block with the previous ciphertext block before encryption. The trade-off is that encryption is sequential because each block depends on the previous ciphertext block (while decryption can be parallelized). However, CBC by itself does not provide integrity protection.
- Counter mode (CTR): Encrypts a sequence of counter blocks, then applies an exclusive OR (XOR) operation with the plaintext to produce ciphertext, allowing blocks to be encrypted in parallel again for better performance. CTR requires a unique counter block sequence for a given key and, on its own, does not provide integrity protection.
- Galois/Counter mode (GCM): Builds on CTR by adding authentication, providing both confidentiality and data integrity while supporting parallel encryption. GCM also requires a unique IV/nonce per key.
Examples of block ciphers
The following algorithms are well-defined examples of block ciphers specified in cryptographic standards:
- AES: Encrypts and decrypts data in 128-bit blocks with key sizes of 128, 192, or 256 bits. Widely used for electronic data protection.
- Triple Data Encryption Standard (3DES): Also called TDEA, it encrypts 64-bit blocks by applying the DES algorithm three times, using either two-key or three-key variants. Under current NIST guidance, 3DES/TDEA should not be used to apply cryptographic protection to new information (and encryption with three-key TDEA is disallowed after December 31, 2023, except where other NIST guidance specifically allows it).
- Camellia: Encrypts 128-bit blocks using keys of 128, 192, or 256 bits. The algorithm includes a key-scheduling part and a data-randomizing part as part of its encryption design.
Strengths and limitations of block ciphers
Block ciphers provide high security when used with strong keys and well-suited algorithms, making brute-force attacks impractical at modern key sizes. Modern standardized block ciphers are designed to resist common cryptanalytic attacks, including differential and linear cryptanalysis. Block ciphers are effective for encrypting large or structured data sets, especially when combined with secure modes of operation that prevent pattern exposure.
However, block ciphers operate on fixed block sizes, so modes require padding to handle data that isn't an exact multiple of the block size, which adds complexity and potential risks if implemented incorrectly. Certain modes, such as ECB, can leak patterns by producing identical ciphertext blocks for identical plaintext, reducing confidentiality.
Performance varies with the algorithm, mode, and implementation. Some modes support parallel processing (for example, CTR), while others impose sequential dependencies. Additionally, block ciphers are often used for real-time data via stream-like modes, but buffering and latency characteristics depend on the chosen mode and its implementation.
Block cipher vs. stream cipher
| Block cipher | Stream cipher | |
| How data is processed | Encrypts data in fixed-size blocks | Encrypts data as a continuous stream, usually bytes/words |
| Usage | Used with a mode of operation (often with an IV/nonce) to encrypt data securely beyond one block | Uses a key (typically with a nonce/IV and counter) to generate a keystream, which is combined with the data as it flows |
| Handling of multiple data units | Requires a mode of operation to securely process many blocks together | Designed to process data continuously without block-handling modes |
| Typical application context | AES, 3DES, and Camellia | Wired Equivalent Privacy (WEP), Salsa20, and ChaCha20 |


