-
What is home title theft (deed fraud)? How to spot it and protect your home
Home title theft, also known as deed fraud (or title fraud), is a scam in which someone files fraudulent property documents to make it appear that they own the property. It often doesn’t require mov...
-
How to delete a Gmail account: Step-by-step guide (desktop, iPhone, Android)
A Gmail address can stick around for years, long after it stops being useful. Keeping old accounts active can expand a digital footprint and leave more personal data tied to logins that aren’t regul...
-
How to clear cache on an iPad for optimal performance
Clearing your iPad's cache can help in specific situations, such as when a browser or app is slow, outdated content is displayed, or storage space is low. The key is knowing what type of cache to clea...
-
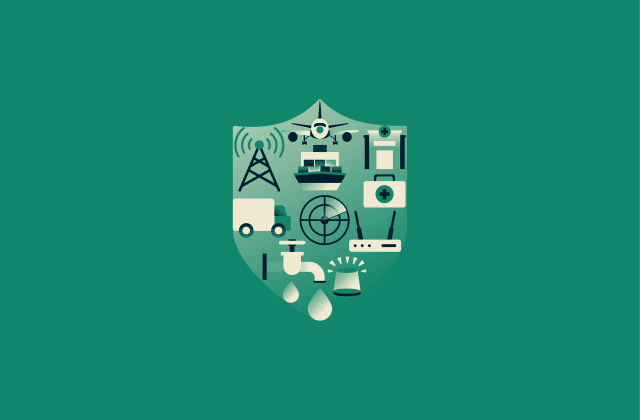
Understanding critical infrastructure security: A comprehensive overview
Power, water, healthcare, transportation, and communications are all vital in daily life. When these services are disrupted, the impact can spread quickly. Critical infrastructure security focuses on ...
-

How to fix “Connection timed out” in Minecraft easily
Fixing a “Connection timed out” error in Minecraft depends on what’s causing it. The error can be triggered by a range of factors, from local network conditions to server-side problems, but beca...
-
What is a personal hotspot, and how does it work?
A personal hotspot turns a smartphone into a portable internet access point, allowing other devices to get online through it. This guide explains how it works, the main hotspot options, how to set it ...
-
Virtual server vs. physical server: Key differences explained
The server setup you choose affects reliability, scalability, and cost. Virtual and physical servers solve different problems, so it’s worth understanding the trade-offs before you commit. In this g...
-
What is bluebugging, and how does it work?
Bluetooth uses pairing and device permissions to control access. When those controls are weak, misconfigured, or bypassed, a nearby attacker may access functions beyond what Bluetooth should permit. T...
-

What is TrickBot malware, and how to stop it
TrickBot is a widely deployed malware toolkit associated with credential theft and the enabling of ransomware. While major disruptions reduced its operations, the infection patterns and response steps...
-
What is OAuth 2.0, and how does it work
Modern apps rarely operate in isolation. Email clients connect to calendars, productivity tools link to cloud storage, and apps request access to existing accounts instead of creating new logins. Thes...
-
- Pricing
- VPN for Teams
-
-
ExpressVPN Intudstry-leading, ultra-fast VPN with secure servers in 105 countries.
-
ExpressMailGuard Private email relay service to protect your inbox and identity.
-
ExpressKeys Secure password management, multi-factor authentication, and more.
-
ExpressAIComing soon The first consumer AI powered by confidential computing for privacy-led intelligence.
-
Identity Defender Powerful suite of ID protection, monitoring, and data removal tools
- View All Products
-
- My Account

