Forklaring på stærk VPN-kryptering og -sikkerhed
VPN-kryptering er kompliceret og bygger generelt på gennemtestede implementeringer af avanceret matematik. Læs videre for at lære mere om, hvordan ExpressVPN bruger stærk kryptering til at beskytte dine data og din kommunikation.
Video: Sådan bruger en VPN tunneling og kryptering
Hvor sikker er ExpressVPN's kryptering?
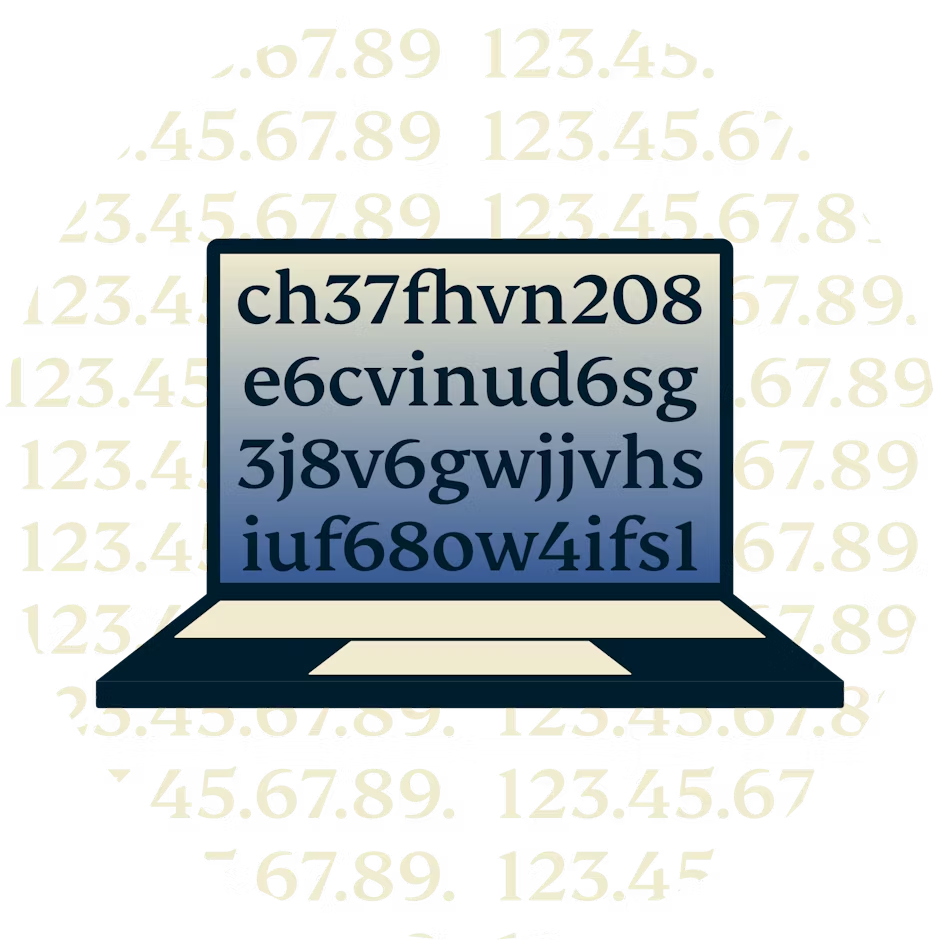
Udover at skjule din IP-addresse og blande din trafik med trafik fra andre brugere krypterer ExpressVPN også din trafik mellem de sikre VPN-servere og din computer. På den måde kan dine data ikke aflæses af tredjeparter som bl.a. din internet- eller wi-fi-udbyder.
ExpressVPN bruger AES (Advanced Encryption Standard) med 256-bit-nøgler – også kendt som AES-256. Det er den samme krypteringsstandard, som bruges af den amerikanske regering og sikkerhedseksperter over hele verden til at beskytte hemmelige oplysninger.
256-bit-nøgler betyder, at der er 2^256 eller 1,1 x 10^77 mulige kombinationer. Det er 115.792.089.237.316.195.423.570.985.008.687.907.853.269.984.665.640.560.000.000.000.000.000.000.000.000 mulige kombinationer! Et brute-force-angreb med et keyspace på 256-bit er for at sige det simpelt, umuligt, selv hvis alle verdens stærkeste supercomputere arbejdede lige så længe, som universet har eksisteret – milliarder og milliarder af gange.
VPN-protokoller: Lightway
ExpressVPN har et stort udvalg af VPN-protokoller for at implementere en stærk kryptering mellem din computer og den VPN-serverplacering, du forbinder til. Når du bruger ExpressVPN-appen, kan du nemt skifte mellem protokollerne, selvom vi anbefaler, at du vælger den automatiske indstilling. Den vælger nemlig den protokol, der er bedst til din hastighed og sikkerhed.
Udover at tilbyde en række standardprotokoller, herunder OpenVPN og IKEv2, udviklede ExpressVPN Lightway, der er designet til at overgå dem alle med hensyn til hastighed, pålidelighed og sikkerhed. Prøv den selv. Lær mere om Lightway.
Her er nogle af funktionerne i ExpressVPN's kryptering med Lightway:
Servergodkendelse
Ligesom HTTPS og OpenVPN bruger Lightway certifikater til at beskytte brugeren mod man-in-the-middle-angreb. Din VPN-klient har et forudindlæst certifikat, der bruges til at godkende en VPN-server. Når du bruger en ekstern eller open source Lightway-klient, vil du selv kunne indlæse certifikatet for at forbinde til VPN-servere.
De to kodningsmetoder, der anvendes i Lightway, er AES-256-GCM og ChaCha20/Poly1305. På grund af den fremragende hardwareacceleration af AES, der er tilgængelige i de fleste enheder, vil Lightway som standard ofte bruge denne velafprøvede cipher. ChaCha20 kan kun bruges på routere med lavere effekt eller billigere mobile enheder.
HMAC-bekræftelse
HMAC står for Keyed-Hash Message Authentication Code. En "Message Authentication Code" sikrer, at en hacker, der har mulighed for at læse dataene i realtid, ikke kan ændre data under overførsel. TLS og OpenVPN bruger også hashes til godkendelse (deraf H'et i HMAC).
Kontrolkanalskryptering
For at sikre integriteten og fortroligheden af krypterede data, selv på lavtydende hardware, bruger ExpressVPN AES-256-GCM. AES er en af de mest udbredte symmetriske krypteringsstandarder, baseret på Rijndael-koden, der blev udviklet af de belgiske kryptografer Joan Daemen og Vincent Rijmen i 1998. 256 refererer til den faste størrelse af hver krypteret blok, 256 bits. GCM (Galois/Counter Mode) giver din computer mulighed for at kryptere flere pakker på én gang, hvilket sikrer, at hastigheden på din forbindelse aldrig bliver langsommere.
Datakanalskryptering
Datakanalskryptering beskytter mod, at dine oplysninger er synlige for de parter, dine data sendes gennem. ExpressVPN bruger en symmetrisk krypteringsordning, hvor nøglen udveksles ved hjælp af den elliptiske kurve, som bygger på Diffie-Hellman-nøgleudveksling. ExpressVPN-serveren og din VPN-app bruger smartmatematik til at udveksle og verificere en hemmelig nøgle, som derefter bruges til at kryptere dataene for hele sessionen.
Post-kvantebeskyttelse
Ved at integrere post-kvantesupport med DTLS 1.3, forbedrer vi vores VPN-tjeneste, så den er beskyttet over for fremskridt inden for kvantecomputere.
Lightway inkluderer som standard post-kvantebeskyttelse, der beskytter dig mod angribere med adgang til både klassiske og kvantecomputere. ExpressVPN er en af de første VPN'er, der implementerer post-kvanteunderstøttelse, hvilket fremtidssikrer vores brugere til en kvantesikker verden.
Download ExpressVPN på alle dine enheder
Få den bedste VPN til iOS, Mac, iPhone, Android og flere.

Et ExpressVPN-abonnement giver dig softwareløsninger til alle enheder i dit hjem, inklusive spillekonsoller som PlayStation og Xbox samt smart-tv-systemer som Apple TV, Amazon TV Fire Stick og Samsung Smart TV. Få en VPN APK til dine Android-enheder, eller download ExpressVPN til iOS. Du kan endda få en VPN-udvidelse til Chrome.
Samt VPN-udvidelser til dine yndlingsbrowsere
Ofte stillede spørgsmål
Kan man stole på ExpressVPN?
Som en virksomhed, der fokuserer på dit privatliv, har ExpressVPN arbejdet nat og dag for at skabe tillid hos både vores kunde r og branchen, bl.a. i samarbejde med Center for Democracy and Technology for at udvikle et sæt standarder, som VPN-tjenester skal kunne vise for at opnå troværdighed .
Vi har også udviklet brancheførende sikkerhedsinitiativer som:
- TrustedServer, en uafhængigt revideret VPN-serverteknologi, der leverer fantastiske beskyttelse af privatliv; og
- Lightway, en specialbygget VPN-protokol, der er hurtigere, mere pålidelig og mere sikker end standardprotokoller. Vi har open source-kernekode for fuld gennemsigtighed.
Hvordan ved jeg, at ExpressVPN er sikker?
Sikkerhed er i centrum for alt, vi laver hos ExpressVPN. Vi sigter ikke bare mod at designe vores apps og systemer til at tilbyde et højt niveau af privatliv og sikkerhed, men får også rutinemæssigt uafhængige revisorer til at validere vores sikkerhedsudsagn. Det er en af de bedste måder for vores brugere at vide, om de kan stole på vores tjenester, når det kommer til at beskytte dem. Se den fulde liste over revisioner og læs de fulde rapporter.
Er ExpressVPN sikker og lovlig?
Ja. ExpressVPN giver en super sikkerhed til din onlineoplevelse, især på offentlige wi-fi-netværk. Så har du altid en beskyttet adgang til ethvert netværk.
Derudover er VPN'er lovlige i langt de fleste jurisdiktioner i verden og bruges i stor udstrækning af både enkeltpersoner og virksomheder, når de vil beskytte deres data. Selv i områder, hvor brug af en VPN nogle gange ikke anbefales, støtter mange regeringer stiltiende deres brug af embedsmænd, akademikere eller virksomheder, så de kan være konkurrencedygtige i en forbunden verden. Det er simpelthen ikke praktisk for lande at forbyde alle VPN'er.
Men husk nu på, at ulovlig onlineaktivitet altid er ulovlig, uanset om du bruger en VPN eller ej.
Kan ExpressVPN hackes?
ExpressVPN tager dit privatliv ekstremt seriøst og tager alle tænkelige foranstaltninger for at forbedre og beskytte sikkerheden af vores tjeneste. ExpressVPN indsamler derfor ikke brugernes forbindelses- eller trafiklogfiler, og vores egen TrustedServer-teknologi sørger for, at alle data slettes fra serverne ved hver eneste genstart. Læs mere om vores metoder, der gør systemer svære at kompromittere og dermed minimere potentielle skader, hvis et tilfælde skulle opstå.
Samtidig beskytter brugen af en VPN dig mod hackingmetoder som bl.a. packet sniffing og man-in-the-middle-angreb. Faktisk er brugen af en VPN god praksis for alle salgs forbindelser, men kan være specielt praktisk, når du browser på usikre HTTP-hjemmesider. Udlændinge, rejsende og alle andre personer på farten bør bruge en VPN, når de er på usikre netværk som et gratis offentligt wi-fi-netværk.
Er ExpressVPN virkelig privat?
ExpressVPN forbedrer i høj grad dit privatliv, da din onlinetrafik krypteres, og du får anden IP-adresse. Det betyder mindre overvågning og sporing fra tredjeparter. Vi gemmer heller aldrig logfiler over din online browsingaktivitet. Selv hvis nogle regeringsinstitutioner eller andre juridiske enheder tvinger os til at levere brugerdata, kan vi ikke levere data, vi ikke har.
Sælger ExpressVPN dine oplysninger?
Nej. ExpressVPN er først og fremmest et firma, der ligger vægt på dit privarliv, og vi gemmer derfor ingen aktivitets- eller forbindelseslogfiler. ExpressVPN gemmer heller aldrig data, der tillader at spore specifikke netværksaktiviter eller adfærd og forbinde det til en individuel bruger. Det betyder, at der slet ikke eksisterer data, der kan sælges.
ExpressVPN indsamler og bruger kun personlige oplysninger til de formål, der er angivet i vores privatlivspolitik, og vi sælger ikke dine personlige oplysninger til tredjeparter .
Lær mere om at bruge en VPN
-
![En bærbar computers sikre forbindelse til internettet.]()
-
![En plante ved sin bærbare computer med ExpressVPN.]()
-
![Bærbar computer med flere browservinduer.]()
Fjern blokering af hjemmesider
Få adgang til dine foretrukne webtjenester og omgå censur
Sikkerhed og privatliv
Værktøjer og tjenester
Er du klar til at prøve den bedst krypterede VPN?
VPN-kryptering er essentielt. Prøv ExpressVPN. Du er 100 % dækket af vores 30-dages pengene-tilbage-garanti.